Thank you for visiting nature.com. You are using a browser version with limited support for CSS. To obtain the best experience, we recommend you use a more up to date browser (or turn off compatibility mode in Internet Explorer). In the meantime, to ensure continued support, we are displaying the site without styles and JavaScript.
- View all journals
- Explore content
- About the journal
- Publish with us
- Sign up for alerts
- Reverse Engineering
- Published: 13 December 2018

How we made Bluetooth
- Jaap Haartsen 1
Nature Electronics volume 1 , page 661 ( 2018 ) Cite this article
10k Accesses
3 Citations
12 Altmetric
Metrics details
- Electrical and electronic engineering
- Information theory and computation
Bluetooth allows electronic devices to communicate over short distances and is used by billions of devices worldwide. Jaap Haartsen recalls the developments that led to the establishment of the Bluetooth wireless technology standard.
In 1990, after completing my PhD at Delft University of Technology, I was hired by Nils Rydbeck who had just started the Ericsson–GE mobile phone division in Research Triangle Park, North Carolina, USA. Rydbeck also headed the Ericsson mobile phone division in Lund, Sweden, and had created an ideal environment for young engineers to play around with different ideas and technologies without being restricted by commercial barriers. My first manager was Paul Dent, a great inventor who taught me how to map ideas into patent applications. I initially worked on digital cellular telephony, but after a while I moved to indoor communications.

In the summer of 1994, I moved to Lund, where Rydbeck asked me to work on a new concept: a short-range radio link between a cellular phone and nearby electronic devices, supporting both voice and data. At the time, there was an ongoing project called Cornelius that investigated a wireless link between a phone and a voice headset. However, this was based on an analogue technology and did not support data. And because of the choice of spectrum, it could not be used worldwide. I started to look at other technologies, like the cordless phone standard Digital Enhanced Cordless Telecommunications (DECT) or wireless local area network (WLAN) 802.11, but none fulfilled the requirements of peer connectivity, support for voice and data, and low-power consumption.
Later in 1994, I attended an IEEE conference in The Hague, the Netherlands, that hosted symposia on both personal, indoor and mobile radio communications, and wireless computer networks, the first with focus on voice and the second on data. At the conference, I learned more about the use of the 2.4 GHz industrial, scientific and medical (ISM) radio band as a global spectrum for communications, and knew that this would be the way forward. Regulations, such as the US Federal Communications Commission (FCC) Part 15, however, put restrictions on the use of the ISM band, and, therefore, frequency hop (FH) spreading or direct-sequence (DS) spreading would be required. Spreading distributes the signal power over a larger part of the frequency spectrum, which can be accomplished either by jumping back and forth with a narrowband, low-rate signal (FH) or by using a wide bandwidth with a high-rate signal (DS). Furthermore, since this was a licence-free band, a radio system operating in it had to deal with interference from other users, ranging from garage door openers to baby monitors. To deal with this interference, I selected frequency hopping because, instantaneously, the radio occupies only a small part of the spectrum and nearby interferers can be suppressed by channel filtering. And at the same time, the radio, on average, hops through the entire ISM band, providing robustness against fading and static interferers.
One of the challenges in the radio system was establishing a connection quickly. For optimal robustness, the 80 MHz of the 2.4 GHz band was divided into 79 frequencies (matching the carrier plan of the WLAN 802.11 FH variant). When not connected, the device is hopping around in the spectrum, scanning at a low duty cycle for other devices that may want to connect. The other device does not know when the first device will scan and at what frequency. There is both an uncertainty in time and in frequency. How to solve this problem at low power consumption and low latency? The solution was to reduce the frequency uncertainty by not using all 79 carriers during connection establishment, but only 32 carriers. Since this did not satisfy the FCC Part 15 requirements for FH, spreading codes were used at connection establishment to satisfy the FCC’s hybrid FH/DS spreading requirements.
Early in 1995, Sven Mattisson joined the Ericsson division in Lund. An expert on radio implementations, he started to work on the hardware development of the radio. The intent was to make a low-power radio in complementary metal–oxide–semiconductor (CMOS) technology without any external components. With the hardware team, I worked on system solutions to create a full CMOS implementation. In Lund, the project was called MC Link. MC came from a multi-communicator Ericsson was developing: a small personal assistant that could be connected to the cellular phone via a wireless link.
In 1997, after nearly four years as a research project, Ericsson hired Örjan Johansson to create a business around the short-range radio concept. An ecosystem was needed, involving other industries. Intel was the first interested party. Together with key people from Intel, including Jim Kardach and Simon Ellis, other companies were approached: Nokia, Toshiba and IBM. The codename Bluetooth was used for this international project. Together, the five companies created the Bluetooth Special Interest Group in 1998. The rest is history. The technology was publicly announced in May 1999 and the first specifications were released in July 1999. In 2000, Ericsson launched its first Bluetooth product: a wireless voice headset. Interestingly, it came with an adaptor for the phone since the phones did not yet have Bluetooth embedded.
Author information
Authors and affiliations.
Jaap Haartsen Consultancy Company, Rolde, the Netherlands
Jaap Haartsen
You can also search for this author in PubMed Google Scholar
Corresponding author
Correspondence to Jaap Haartsen .
Rights and permissions
Reprints and permissions
About this article
Cite this article.
Haartsen, J. How we made Bluetooth. Nat Electron 1 , 661 (2018). https://doi.org/10.1038/s41928-018-0186-x
Download citation
Published : 13 December 2018
Issue Date : December 2018
DOI : https://doi.org/10.1038/s41928-018-0186-x
Share this article
Anyone you share the following link with will be able to read this content:
Sorry, a shareable link is not currently available for this article.
Provided by the Springer Nature SharedIt content-sharing initiative
Quick links
- Explore articles by subject
- Guide to authors
- Editorial policies
Sign up for the Nature Briefing newsletter — what matters in science, free to your inbox daily.
The Bluetooth technology: merits and limitations
Ieee account.
- Change Username/Password
- Update Address
Purchase Details
- Payment Options
- Order History
- View Purchased Documents
Profile Information
- Communications Preferences
- Profession and Education
- Technical Interests
- US & Canada: +1 800 678 4333
- Worldwide: +1 732 981 0060
- Contact & Support
- About IEEE Xplore
- Accessibility
- Terms of Use
- Nondiscrimination Policy
- Privacy & Opting Out of Cookies
A not-for-profit organization, IEEE is the world's largest technical professional organization dedicated to advancing technology for the benefit of humanity. © Copyright 2024 IEEE - All rights reserved. Use of this web site signifies your agreement to the terms and conditions.
Internet of things technology, research, and challenges: a survey
- Published: 02 May 2024
Cite this article

- Amit Kumar Vishwakarma 1 ,
- Soni Chaurasia 2 ,
- Kamal Kumar 3 ,
- Yatindra Nath Singh 4 &
- Renu Chaurasia 5
127 Accesses
Explore all metrics
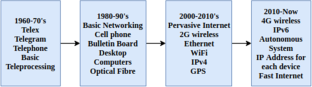
The world of digitization is growing exponentially; data optimization, security of a network, and energy efficiency are becoming more prominent. The Internet of Things (IoT) is the core technology of modern society. This paper is based on a survey of recent and past technologies used for IoT optimization models, such as IoT with Blockchain, IoT with WSN, IoT with ML, and IoT with big data analysis. Suppose anyone wants to start core research on IoT technologies, research opportunities, challenges, and solutions. In that case, this paper will help me understand all the basics, such as security, interoperability, standards, scalability, complexity, data management, and quality of service (QoS). This paper also discusses some recent technologies and the challenges in implementation. Finally, this paper discusses research possibilities in basic and applied IoT Domains.
This is a preview of subscription content, log in via an institution to check access.
Access this article
Price includes VAT (Russian Federation)
Instant access to the full article PDF.
Rent this article via DeepDyve
Institutional subscriptions

Similar content being viewed by others

RETRACTED ARTICLE: A Review and State of Art of Internet of Things (IoT)

IoT Reference Model

Blockchain for healthcare data management: opportunities, challenges, and future recommendations
Data availability.
Available on request.
Ghorbani HR, Ahmadzadegan MH (2017) Security challenges in internet of things: survey. In: 2017 IEEE conference on wireless sensors (ICWiSe)
Brock DL (2013) The electronic product code (EPC) a naming scheme for physical objects. http://www.autoidlabs.org/ uploads/media/MIT-AUTOID-WH-002.pdf
IoT Analytics (2014) Why the internet of things is called internet of things: definition, history, disambiguation. https://iot-analytics.com/internet-of-things-definition/
Internet of Things (2005) International telecommunication union (ITU), Geneva. https://www.itu.int/net/wsis/tunis/newsroom/stats/The-Internet-of-Things-2005.pdf
Internet of Things (2010) https://en.oxforddictionaries.com/definition/us/ internetofthings
Manyika Chui M, Bisson P, Woetzel J, Dobbs R, Bughin J, Aharon D (2015) Unlocking the potential of the internet of things. https://www.mckinsey.com/~/media/McKinsey
Vermesan O, Friess P, Guillemin P, Gusmeroli S, Sundmaeker H, Bassi A, Jubert IS, Mazura M, Harrison M, others (2011) Internet of things strategic research roadmap
Artik cloud (2017) https://developer.artik.cloud/documentation/getting-started/index.html
Fusion Connect (2014) https://autodeskfusionconnect.com/iot-devices
(2016) https://docs.aws.amazon.com/iot/latest/developerguide/what-is-aws-iot.html
Guth J, Breitenbücher U, Falkenthal M, Leymann F, Reinfurt L (2016) Comparison of IoT platform architectures: A field study based on a reference architecture. In: 2016 Cloudification of the internet of things (CIoT)
Balani, Naveen and Hathi, Rajeev, Enterprise IoT: A Definitive Handbook. In: CreateSpace Independent Publishing Platform, 2015
GE Predix (2017) https://docs.predix.io/en-US/platform
Soliman M, Abiodun T, Hamouda T, Zhou J, Lung CH, (2013) Smart home: integrating internet of things with web services and cloud computing. In: 2013 IEEE 5th International conference on cloud computing technology and science
Google Cloud (2016) https://cloud.google.com/solutions/iot-overview
Familiar B (2015) IoT and microservices. In: Microservices, IoT, and Azure. Apress, Berkeley, CA. In: Internet of Things;Web services:Azure IOT
Microsoft IoT platform (2015) https://docs.microsoft.com/en-us/rest/api/iothub/?redirectedfrom=MSDN
High R (2012) The era of cognitive systems: an inside look at ibm watson and how it works. In: Internet of Things;Web services:Azure IOT
IBM Watson IoT (2017) https://www.ibm.com/internet-of-things
Deering S, Hinden R (2017) Internet Protocol, Version 6 (IPv6) Specification. https://tools.ietf.org/html/rfc8200
WInter Ed T, Thubert P, Brandt A, Hui J, Kelsey R, Levis P, Pister K, Struik R (2012) ipv6 routing protocol for low-power and lossy networks. https://tools.ietf.org/html/rfc6550
Saputro N, Akkaya K, Uludag S (2012) A survey of routing protocols for smart grid communications. http://www.sciencedirect.com/science/article/pii/S1389128612001429 , vol 56
Yi P, Iwayemi A, Zhou C (2011) Building automation networks for smart grids. In: International journals of digital multimedia broadcasting
Fairhurst G Jones T (2018) Transport features of the user datagram protocol (UDP) and lightweight UDP (UDP-Lite). https://www.rfceditor.org/info/rfc8304
Palattella MR, Accettura N, Vilajosana X, Watteyne T, Grieco LA, Boggia G, Dohler M (2013) Standardized protocol stack for the internet of (Important) things. In: IEEE communications surveys tutorials, vol 15
Karagiannis V, Chatzimisios P, Vazquez-Gallego F, Alonso-Zarate J (2015) A survey on application layer protocols for the internet of things. Transaction on IoT and Cloud Computing
Banks A, Gupta R (2014) MQTT Version 3.1.1. Edited by Andrew Banks and Rahul Gupta. OASIS Committee Specification Draft 02 / Public Review Draft 02. http://docs.oasis-open.org/mqtt/mqtt/v3.1.1/csprd02/mqtt-v3.1.1-csprd02.html
Bormann C, Castellani AP, Shelby Z (2012) CoAP: An Application Protocol for Billions of Tiny Internet Nodes. IEEE Internet Computing
Shelby Z, Hartke K, Bormann C (2014) The constrained application protocol (CoAP). https://tools.ietf.org/html/rfc7252
Johansson P, Kazantzidis M, Kapoor R, Gerla M (2001) Bluetooth: an enabler for personal area networking. IEEE Network
Kirsche M, Klauck R (2012) Unify to bridge gaps: Bringing XMPP into the Internet of Things. In: 2012 IEEE international conference on pervasive computing and communications workshops
Naik N, Jenkins P (2016) Web protocols and challenges of Web latency in the Web of Things. In: 2016 Eighth international conference on ubiquitous and future networks (ICUFN)
Han Dm, Lim Jh (2010) Smart home energy management system using IEEE 802.15.4 and zigbee. IEEE Transactions on Consumer Electronics
Eriksson J, Balakrishnan H, Madden S (2008) Cabernet: vehicular content delivery using wifi. https://doi.org/10.1145/1409944.1409968
Ratasuk R, Vejlgaard B, Mangalvedhe N, Ghosh A (2016) NB-IoT system for M2M communication. In: 2016 IEEE Wireless communications and networking conference
ANDRIES MI, BOGDAN I, NICOLAESCU SV, SCRIPCARIU L (2007) WiMAX features and applications. http://www.agir.ro/buletine/687.pdf
Kucharzewski L, Kotulski Z (2014) WiMAX networks architecture and ata security. Annales UMCS Informatica AI X
Adams JT (2006) An introduction to IEEE STD 802.15.4. In: 2006 IEEE aerospace conference
Atzori L, Iera A, Morabito G (2010) The internet of things: a survey. journal = Computer Networks. http://www.sciencedirect.com/science/article/pii/S1389128610001568 , vol.54
Mainetti L, Patrono L Vilei A (2011) Evolution of wireless sensor networks towards the Internet of Things: A survey. In: SoftCOM 2011, 19th international conference on software, telecommunications and computer networks
Miorandi D, Sicari S, De Pellegrini F, Chlamtac I (2012) Internet of things: Vision, applications and research challenges. http://www.sciencedirect.com/science/article/pii/S1570870512000674 , vol 10, pp 1497–1516
Xu LD, He W, Li S (2014) Internet of things in industries: a survey. In: IEEE Transactions on industrial informatics, vol 10
Botta A, De Donato W, Persico V, Pescapé A (2016) Integration of cloud computing and internet of things: a survey. http://www.sciencedirect.com/science/article/pii/S0167739X15003015 , vol 56
Seyedzadegan M, Othman M (2013) IEEE 802.16: WiMAX Overview, WiMAX Architecture. http://www.ijcte.org/papers/796-Z1030.pdf
Abdulzahra AM, Al-Qurabat AK, Abdulzahra SA (2023) Optimizing energy consumption in WSN-based IoT using unequal clustering and sleep scheduling methods. Internet of Things 22:100765
Chaurasia S, Kumar K (2023) ACRA:Adaptive Meta-heuristic Based Clustering and Routing Algorithm for IoT-Assisted Wireless Sensor Network. Peer to Peer Networking and Application. Springer
Chaurasia S, Kumar K (2023) MBASE: Meta-heuristic Based optimized location allocation algorithm for baSE station in IoT assist wireless sensor networks. Multimedia Tools and Applications, pp 1–33
Senthil GA, Raaza A, Kumar N (2022) Internet of things energy efficient cluster-based routing using hybrid particle swarm optimization for wireless sensor network. Wirel Pers Commun 122.3: 2603-2619
Prasanth A, Jayachitra S (2020) A novel multi-objective optimization strategy for enhancing quality of service in IoT-enabled WSN applications. Peer Peer Netw Appl 13:1905–1920
Article Google Scholar
Vaiyapuri T, et al (2022) A novel hybrid optimization for cluster-based routing protocol in information-centric wireless sensor networks for IoT based mobile edge computing. Wirel Pers Commun 127.1: 39-62
Dhiman G, Sharma R (2022) SHANN: an IoT and machine-learning-assisted edge cross-layered routing protocol using spotted hyena optimizer. Complex Intell Syst 8(5):3779–3787
Seyfollahi A, Taami T, Ghaffari A (2023) Towards developing a machine learning-metaheuristic-enhanced energy-sensitive routing framework for the internet of things. Microprocess Microsyst 96:104747
Donta PK et al (2023) iCoCoA: intelligent congestion control algorithm for CoAP using deep reinforcement learning. J Ambient Intell Humaniz Comput 14(3):2951–2966
Rosati R et al (2023) From knowledge-based to big data analytic model: a novel IoT and machine learning based decision support system for predictive maintenance in industry 4.0. J Intell Manuf 34.1:107–121
Babar M et al (2022) An optimized IoT-enabled big data analytics architecture for edge-cloud computing. IEEE Internet Things J 10(5):3995–4005
Article MathSciNet Google Scholar
Lv Z, Singh AK (2021) Big data analysis of internet of things system. ACM Trans Internet Technol 21(2):1–15
Qiu Y, Zhu X, Jing L (2021) Fitness monitoring system based on internet of things and big data analysis. IEEE Access 9:8054–8068
Rahman A et al (2021) Smartblock-sdn: An optimized blockchain-sdn framework for resource management in iot. IEEE Access 9:28361–28376
Zhao Y et al (2023) A lightweight model-based evolutionary consensus protocol in blockchain as a service for IoT. IEEE Transactions on Services Computing
Saba T et al (2023) Blockchain-enabled intelligent iot protocol for high-performance and secured big financial data transaction. IEEE Transactions on Computational Social Systems
Abed S, Reem J, Bassam JM (2023) A review on blockchain and IoT integration from energy, security and hardware perspectives. Wirel Pers Commun 129(3):2079–2122
Javanmardi S et al (2023) An SDN perspective IoT-Fog security: A survey. Comput Netw 229:109732
Qayyum A et al (2023) Secure and trustworthy artificial intelligence-extended reality (AI-XR) for metaverses. ACM Computing Surveys
Rawat P, Chauhan S (2021) Clustering protocols in wireless sensor network: A survey, classification, issues, and future directions. Comput Sci Rev 40:100396
Albouq SS et al (2023) A survey of interoperability challenges and solutions for dealing with them in IoT environment. IEEE Access 10:36416–36428
Rana B, Singh Y, Singh PK (2021) A systematic survey on internet of things: Energy efficiency and interoperability perspective. Trans Emerg Telecommun Technol 32(8):e4166
Sasaki Y (2021) A survey on IoT big data analytic systems: current and future. IEEE Internet of Things Journal 9(2):1024–1036
Alfandi O et al (2021) A survey on boosting IoT security and privacy through blockchain: Exploration, requirements, and open issues. Cluster Comput 24(1):37–55
Bian Jet al. Machine learning in real-time internet of things (iot) systems: A survey. IEEE Internet of Things J 9(11): 8364–8386
Donta PK et al (2022) Survey on recent advances in IoT application layer protocols and machine learning scope for research directions. Digital Commun Netw 8(5):727–744
Download references
No funding was received to carry out this work.
Author information
Authors and affiliations.
Management science and technology, Khalifa University, Abu Dhabi, UAE
Amit Kumar Vishwakarma
Computer science & Engineering, SGT University, Gurugram, India
Soni Chaurasia
Department of Information Technology, IGDTUW, New Delhi, India
Kamal Kumar
Electrical Engineering, IIT Kanpur, Kanpur, India
Yatindra Nath Singh
Computer science & Engineering, AIT, Rooma, Kanpur, India
Renu Chaurasia
You can also search for this author in PubMed Google Scholar
Contributions
Equally contributed.
Corresponding author
Correspondence to Soni Chaurasia .
Ethics declarations
Conflicts of interest.
No conflict of interest.
Consent to Publish
As per journal policy.
Additional information
Publisher's note.
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
Reprints and permissions
About this article
Vishwakarma, A.K., Chaurasia, S., Kumar, K. et al. Internet of things technology, research, and challenges: a survey. Multimed Tools Appl (2024). https://doi.org/10.1007/s11042-024-19278-6
Download citation
Received : 18 October 2023
Revised : 13 March 2024
Accepted : 18 April 2024
Published : 02 May 2024
DOI : https://doi.org/10.1007/s11042-024-19278-6
Share this article
Anyone you share the following link with will be able to read this content:
Sorry, a shareable link is not currently available for this article.
Provided by the Springer Nature SharedIt content-sharing initiative
- Semantic intelligence
- IoT protocol
- IoT application
- Research possibilities
- IoT Platforms
- IoT optimization models
- Find a journal
- Publish with us
- Track your research

IMAGES
VIDEO
COMMENTS
Bluetooth is one of the popular technology standards for exchanging data over short distances. In this paper, a study of Bluetooth protocol and its applications is presented.
The Bluetooth TM wireless technology is designed as a short-range connectivity solution for personal, portable, and handheld electronic devices. Since May 1998 the Bluetooth SIG has steered the development of the technology through the development of an open industry specification, including both protocols and application scenarios, and a qualification program designed to assure end-user value ...
Bluetooth is a method for data communication that uses short-range radio links to replace cables between computers and their connected units. Industry-wide Bluetooth promises very substantial benefits for wireless network operators, end workers, and content developers of exciting new applications. This article delves into the implementation and architecture of Bluetooth. It also describes the ...
In 1990, after completing my PhD at Delft University of Technology, I was hired by Nils Rydbeck who had just started the Ericsson-GE mobile phone division in Research Triangle Park, North ...
This literature review is critical as it provides a consolidated analysis of papers related to different cybersecurity aspects of Bluetooth technology. However, given the vastness of this research area and the prolific implementation in peripheral devices, we could have likely missed some papers, as we have focused our research on ACM and IEEE DLs.
Bluetooth is sometimes confused with another wireless technology, 802.11b. 802.11b is a standard specification for wireless LANs, but Bluetooth is capable of so much more. 802.11b also work in the 2.4-GHz band, but uses direct-sequencing spread-spectrum (DSSS), which sends data over several different frequencies simultaneously, instead of individually.
The objective of this paper is to provide a comprehensive survey of existing threats to Bluetooth technology, thereby letting users know about these vulnerabilities. We have performed a comprehensive survey to identify major security threats for Bluetooth technology and presented them with illustrations. 3. Background3.1. Bluetooth
Bluetooth technology started off as a wireless, short-range cable replacement technology but it has undergone significant developments over the last two decades. Bluetooth radios are currently embedded in almost all computing devices including personal computers, smart phones, smart watches, and even micro-controllers. For many of us, Bluetooth is an essential technology that we use every day ...
the technology potentially puts both individuals and businesses at risk. To investigate this idea, an understanding of the practical pervasiveness of various Bluetooth protocols needs to be examined in conjunction with identifying documented viable attacks on Bluetooth-enabled devices. This research paper is derived from an MSc thesis
This chapter introduces the security of current Bluetooth technology. Bluetooth devices form an ad‐hoc network for data transmission. Bluetooth uses a technique called spread spectrum frequency hopping to transmit data among 79 different frequencies. The chapter discusses the details of current Bluetooth security solutions. Bluetooth security is provided because of security threats that may ...
The state-of-the-art approaches with respect to Bluetooth scatternet formation are reviewed and compared, to give an overview of the state of the state-of-the-art. -A Bluetooth ad hoc network can be formed by interconnecting piconets into scatternets. The constraints and properties of Bluetooth scatternets present special challenges in forming an ad hoc network efficiently. This paper, the ...
Bluetooth technology, disruptive agents can eavesdrop and compromise the integrity of communication as data is transmitted wirelessly. Intentionally, hackers can jam Bluetooth channels of communication, alter data, and even capture and ... A few research papers have therefore been published on the topics of both the flaws and vulnerabilities in ...
We present results from a 7-day trial of a Bluetooth-enabled card by the New Zealand Ministry of Health to investigate its usefulness in contact tracing. A comparison of the card with traditional contact tracing, which relies on self-reports of contacts to case investigators, demonstrated significantly higher levels of internal consistency in detected contact events by Bluetooth-enabled cards ...
With the latest standard releases, Bluetooth technology is becoming more and more relevant for building and industrial automation. At the same time, Bluetooth is now becoming fundamental for contact tracing applications, to support monitoring and containment of the COVID-19 pandemic. Critical facilities such as nursing homes and hospitals have been severely exposed to the pandemic, but the ...
Bluetooth/sup TM/ wireless technology is a proposed publicly available specification for radiofrequency (RF), short-range, point-to-multipoint voice and data transfer. It also supports point-to-point connections. It operates in the 2.4 GHz ISM (industrial, scientific and medical) band and is based on a low-cost, short-range radio link that facilitates ad-hoc connections for stationary and ...
This paper, the research contributions in this arena are brought together, to give an overview of the state-of-the-art. Simply stated, Bluetooth is a wireless communication protocol. Since it's a communication protocol, you ... wireless technology era, Bluetooth was aimed at unifying the telecom and computing industries.
Implementation of Bluetooth technology in processing aspheric mirrors. NASA Astrophysics Data System (ADS) Chen, Dong-yun; Li, Xiao-jin. 2010-10-01. This paper adopts the Bluetooth wireless transmission to replace the conducting rings currently using in the active lap process to overcome the cost and abrasion problems brought by the conducting rings, which has great significance for reducing ...
The world of digitization is growing exponentially; data optimization, security of a network, and energy efficiency are becoming more prominent. The Internet of Things (IoT) is the core technology of modern society. This paper is based on a survey of recent and past technologies used for IoT optimization models, such as IoT with Blockchain, IoT with WSN, IoT with ML, and IoT with big data ...