An official website of the United States government
The .gov means it’s official. Federal government websites often end in .gov or .mil. Before sharing sensitive information, make sure you’re on a federal government site.
The site is secure. The https:// ensures that you are connecting to the official website and that any information you provide is encrypted and transmitted securely.
- Publications
- Account settings
Preview improvements coming to the PMC website in October 2024. Learn More or Try it out now .
- Advanced Search
- Journal List
- HHS Author Manuscripts


DEVELOPING, SUSTAINING, AND MAXIMIZING TEAM EFFECTIVENESS: AN INTEGRATIVE, DYNAMIC PERSPECTIVE OF TEAM DEVELOPMENT INTERVENTIONS
Marissa l. shuffler.
Clemson University
DEBORAH DIAZGRANADOS
Virginia Commonwealth University
M. TRAVIS MAYNARD
Colorado State University
EDUARDO SALAS
Rice University
Organizations regularly make significant investments to ensure their teams will thrive, through interventions intended to support their effectiveness. Such team development interventions (TDIs) have demonstrated their value from both a practical and empirical view, through enabling teams to minimize errors and maximize expertise and thereby advance organizational gains. Yet, on closer examination, the current state of the TDI literature appears so piecemeal that the robustness of extant scientific evidence is often lost. Accordingly, we seek to provide a more cohesive and dynamic integration of the TDI literature, evolving thinking about TDIs toward a system of interventions that can be optimized. Drawing on the existing theoretical and empirical literatures, we first broadly define TDIs. We then offer an in-depth look at the most common types of TDIs, in terms of summarizing the state of the science surrounding each TDI. Based on this review, we distinguish features that make for an effective TDI. We then advance a more integrative framework that seeks to highlight certain interventions that are best served for addressing certain issues within a team. In conclusion, we promote a call for evolving this robust yet disjointed TDI literature into a more holistic, dynamic, and intentional action science with clear empirical as well as practical guidance and direction.
INTRODUCTION
Time and money have always been critical com- modities for organizations; indeed, one of the major goals of an effective organization is to maximize resources while minimizing costs. The incorporation of teams has increasingly become a prominent solution used by organizations to achieve this balance. Teams are defined as two or more individuals inter- acting dynamically, interdependently, and adaptively toward a common goal, with each member having a specific role to fill within the boundary of the team ( Salas, Dickinson, Converse, & Tannenbaum, 1992 ). In part, the prevalence of teams within orga- nizations is due to the complex problems that orga- nizations often face and the synergistic benefits that the use of teams can provide to organizations—that is, teams offer the capability to achieve what cannot be accomplished by one individual acting alone ( Hackman, 2011 ).
Some have heralded teams to be a basic building block of organizations today ( Stewart & Barrick, 2000 ). Subsequently, there is no lack of theory, research, and consultants in the area of teams and their development ( Cannon-Bowers & Bowers, 2010 ). In fact, given their prominence in organizations, significant investments have been devoted to ensuring teams will succeed, including investment in scholarship as well as practical tools and resources ( Lacerenza, Marlow, Tannenbaum, & Salas, 2018 ; Shuffler, DiazGranados, & Salas, 2011 ). As a result, numerous scientific reviews have been undertaken to extract the individual, team, system, organizational, and environmental factors that define and shape effective teamwork ( Humphrey & Aime, 2014 ; Mathieu, Maynard, Rapp, & Gilson, 2008 ; Salas, Shuffler, Thayer, Bedwell, & Lazzara, 2015 ).
Yet, even with this aforementioned knowledge at hand, organizational teams still fail on a regular— sometimes daily—basis ( Tannenbaum, Mathieu, Salas, & Cohen, 2012 ). Furthermore, although some organizational teams may not actually be failing, their performance may be less than desirable, plateauing or starting to spiral toward decline. Perhaps, even more challenging, the factors that help a team maintain adequate performance may be different from those that assist a team surpass their current performance levels and attain superior performance. As a result, teams, leaders, and organizations often need to intervene by leveraging a range of mechanisms, conditions, tools, and resources that can help them take action to enhance team effectiveness ( Hackman, 2011 ; Kozlowski & Ilgen, 2006 ).
We broadly define these actions taken to alter the performance trajectories of organizational teams as TDIs. Given the complex nature of team effectiveness, it is not surprising that there is a wide array of these TDIs discussed within the scholarly organizational literature. When designed and implemented using evidence-based practices and principles from the scientific literature, TDIs can serve a vital role in improving team effectiveness ( Shuffler et al., 2011 ). However, the often lucrative nature of team development consulting has also resulted in many popular culture resources that are not actually effective. As a result, scientifically derived, evidence-based TDIs are too often lumped with more haphazard, “feel good” TDIs, as ifthey are all one in the same. Certainly, team building (TB) comes to mind as an often misused and abused TDI catchall that can evoke strong, overly positive or negative affective reactions based on experiences ( Cannon-Bowers & Bowers, 2010 ). Further complicating the issue, although there are distinct types of TDIs recognized in the literature that may potentially complement one another, they have been developed and evaluated in relative isolation from one another ( Weaver, Dy, & Rosen, 2014 ) and to varying degrees of scientific rigor. Accordingly, an organized perspective that distinguishes TDIs backed by a solid science is much overdue.
As such, this review addresses four major needs that must be resolved to advance TDI research and practice in organizations. First, we address the need for a clear defmition of what a TDI is—moving beyond what may broadly be considered a TDI to more specifically distinguishing the features of an effective TDI ( Need 1 ). Second, we offer in one place a more indepth review of the different types of TDIs that have garnered substantial attention in the academic litera- ture ( Need 2 ). In identifying major themes in these literatures, we offer guidance as to the state of the science in terms of each TDI’s current or potential contribution. Third, in an effort to discuss what makes TDIs effective, we leverage a relatively simple heuristic of “what,” “why,” “who,” “when,” and “how,” to synthesize the impact that TDI characteristics have in shaping whether a particular TDI is ultimately successful or not for a given context or team. Using our definition and this heuristic, we address a third need in terms of creating a foundation for better understanding how the various TDIs can be better integrated so they may work together ( Need 3 ). We leverage structural elements of prominent team effectiveness models (i.e., McGrath, 1964 ; Marks, Mathieu, & Zaccaro, 2001 ), and based on our review of the literature, introduce an integrative framework that considers dynamic team developmental needs to offer direction for determining what TDI or combination of TDIs may be most effective in shaping team performance trajectories.
Last, to push the science and practice of TDIs toward a more holistic evolution ( Need 4 ), we conclude with future directions in terms of considerations regarding potential advancements for empirically and methodologically applying a more integrative perspective to TDIs, especially across organizational contexts. Each of these needs is particularly important to address, given that we view TDI research and practice as being at a critical crossroads: TDIs can either evolve dynamically to keep up with practical organization demands or continue with the same static lens that is quickly becoming irrelevant.
CONCEPTUALIZING TDIs: AN ORGANIZING DEFINITION
We began our introduction with the most inclusive definitions in terms of what could possibly be included as a TDI. This is purposeful in terms of directing a focus on bounding TDIs as requiring intentional action(s) targeted at team performance trajectories. More specifically, these actions may attempt to (1) improve and support teams that may be struggling or failing, (2) maintain and sustain teams that are adequately performing, and (3) grow and maximize the capacities of teams ready to mature to a higher level of performance. As such, this drills down from broader categories such as organizational development interventions or human resource efforts, to set the team as the focal unit of analysis for this type of intervention. However, the simplistic nature of this definition leaves room for including TDIs that may make attempts yet fail every time to impact team performance trajectories. Moving from this rather broad conceptualization, our first aim is to drill down further into TDIs as a meaningful term, reviewing the extant scientific literature to critically evaluate what an effective TDI looks like and what the broad state of the science looks like regarding trends and patterns in TDI research.
IDENTIFYING IMPACT: CURRENT STATE OF THE SCIENCE WITHIN TDIs
Literature review approach.
We conducted a series of searches for academic publications within the broader organizational behavior, management, and psychology literatures. Databases searched included PsycInfo, Academic OneSource, MedLine, and Google Scholar. Broad and more specific terms, such as “TDIs,” “team development,” “team training (TT),” and “TB,” were used; a full list is available from the first author. When systematic reviews and meta-analyses of TDIs were identified, the reference lists were searched to ensure all relevant articles were included. Although we did not set a timeframe for our searches, the vast majority of sources came from the past 50 years, in line with similar reviews that acknowledge the early 1970s as the start of a concerted interest in team development ( Tannenbaum, Beard, & Salas, 1992 ). Likewise, we excluded sports team sources, a common occurrence in the team literature due to the niche nature of such work as compared with other organizational teams ( Klein, DiazGranados, Salas, Le, Burke, Lyons, & Goodwin, 2009 ; Salas, Cooke, & Rosen, 2008a ). Finally, to be retained, the article had to describe some clear form of TDI.
Our initial searches in these sources resulted in more than 5,000 potentially relevant articles that were then sorted to remove irrelevant articles (e.g., sports coaching and patient health interventions performed by health-care teams instead of team interventions). In particular, although some of our resulting TDI types [e.g., team leadership (TL), team composition (TCo), and team performance monitoring] have broader literatures beyond just that focused on an intervention perspective, we excluded any sources that did not focus on interventions in some form. Both qualitative and quantitative empirical articles were retained if the intervention they described met the aforementioned broad definition, including case studies, experimental, and quasi- experimental designs. In addition, we retained sys- tematic reviews and meta-analyses for confirming our overarching themes within and across TDIs. Overall, our final sample consisted of 514 articles.
Next, we reviewed these articles with two intentions. First, we examined the approaches, findings, and contributions to establish common themes across TDIs, to address Need 3 (integration of TDIs) and Need 4 (future directions). Second, we grouped articles based on the types of TDIs they addressed, enabling us to develop within-TDI themes regarding quality of the research thus far, as well as important themes for understanding the impact of and considerations for different TDIs to address Need 1 (defining TDIs) and Need 2 (review of the literature). Each of the first three authors reviewed the literatures separately and then met to discuss themes within and across TDIs, reconciling any disagreements with one another and with input from the fourth author to produce a final set of themes within and across TDIs.
Current State of the Science
There is a value in addressing an in-depth review (Need 2), especially in terms of identifying the TDIs that target the developmental needs of teams. Specifically, there have been several dominant view- points of how teams develop: (1) teams develop linearly (i.e., consistently in the same pattern over time; Tuckman, 1965 ) or (2) teams experience some type of temporally based punctuated shift as described in the punctuated equilibrium model ( Gersick, 1988 ). Recognizing that teams may function more cyclically than linearly, other models have further incorporated this structure, such as in the input-process-output (IPO) model advanced by McGrath (1984), Steiner (1972) , and Hackman (1987) , that conceptualizes team effectiveness as a system of inputs, processes, and outcomes that influence one another. By using the lens of the IPO model, we are able to organize our review based on the target of each TDI reviewed. Similar reviews exploring the effectiveness of individual TDIs do exist in the extant literature and we have relied on these to guide us, especially in identifying and synthesizing key empirical findings. However, each review highlights only a single TDI at a time, limiting our ability to create a more comprehensive perspective. Thus, although a full empirical, meta-analytical review is beyond the scope of our current review, it is critical to provide some deeper insight into the different categories of TDIs.
As such, the following section offers summaries of ten types of TDIs, organized by the IPO framework. In particular, TDIs that primarily focus on team inputs include team task analysis (TTA), TCo interventions, team work designs (TWDs), and team charters (TChs). Team process-focused TDIs include team performance monitoring and assessment (TPMA), whereas the intervention focused on team outcomes is team debriefs (TD). Finally, there are several TDIs we label as “multifaceted,” given that they can address factors from more than one IPO category. These multifaceted TDIs include TB, TT, team coaching (TCa), and TL. Because of the variance in the depth of literature for each category, some offer more empirical evidence than others.
Team Task Analysis (TTA)
Definition and evidence assessment..
Although the use of teams is becoming more prevalent within organizations, the types of organizations such teams are a part of are quite varied. To be precise, there are countless examples of team research being conducted in contexts such as military, health care, academia, and manufacturing ( Salas, Bowers, & Cannon-Bowers, 1995 ; Stokols, Hall, Taylor, & Moser, 2008; Weaver et al., 2014 ). Certainly, there are some factors of teamwork that translate regardless of the team’s context, for example, the need for effective communication. However, what effective communication looks like will differ across contexts. As such, there are unique features of the team’s context that should be taken into account ( Johns, 2006 ) when determining what teamwork factors are most critical to a particular team. In addition, the tasks teams perform can vary and can also inform the teamwork needs of the team. Certainly, as stated by Nouri et al. (2013) , “one cannot fully understand group performance without taking into account the nature of the taskbeing performed” (p. 741).
Accordingly, the topic of task analysis has received more attention over the past decade. For clarity, TTA is defined as “the process by which the major work behaviors and associated knowledge skills, and abilities (KSAs) that are required for successful job or task performance are identified” ( Arthur, Edwards, Bell, Villado, & Bennett, 2005 : 654). TTA as an intervention influences the team context or members of a team (i.e., the inputs). It is critical to conduct a task analysis, given the task performed by a team can have impacts which can be far-reaching in that it can shape which KSAs that are needed within a team and thereby shape who should be on the team, what staffing level is needed (i.e., TCo which is discussed in the next section), and how the job should be designed ( Medsker & Campion, 1997 ). Likewise, the team’s task can impact how the team’s performance is evaluated ( Arthur et al., 2005 ) and, in turn, how other interventions such as TT, coaching, and debriefs are designed ( Arthur, Glaze, Bhupatkar, Villado, Bennett, & Rowe, 2012 ). The literature on task analysis is robust; however, the literature on TTA is sparser. Some of the literature on TTA has focused on the methodology for using certain techniques (e.g., team cognitive work analysis- Ashoori & Burns, 2013 and hierarchical task analysis- Annett et al., 2000 ) or the use of certain metrics, for example, team relatedness and team workflow to better differentiate between team tasks ( Arthur et al., 2012 ). We organize our summary into the various themes that emerged as we reviewed the TTA literature stream.
TTA Theme 1: TTA requires an assessment of individual and teamwork behaviors/factors.
The work examining team tasks is built on a long history of research that has examined individual performance on work tasks. This research has unpacked the influence of certain factors on how tasks are accomplished. Researchers have considered factors such as importance, frequency, time spent, time to proficiency, criticality of task, difficulty of performing it, and consequences of error ( Sanchez & Fraser, 1992 ) among other factors when assessing work behaviors. Accordingly, given that TTA built on the individual task analysis work, it is not surprising to see that some of the same features that were relevant for individuals will likewise be relevant for teams, namely, Bowers, Baker, and Salas’ (1994) creation of a team task inventory included dimensions such as importance to train, task criticality, task frequency, task difficulty, difficulty to train, and overall team importance. Likewise, Lantz and Brav (2007) detail a variety of task features that are also relevant to teams including demand on responsibility, cognitive demands, and learning opportunities.
That said, there are also factors that are only applicable when considering team tasks. For instance, Campion et al. (1996) provided evidence that the degree of dependency (i.e., interdependence) among team members impacts group processes. So, most of the factors that have been included within TTA focus on team member behaviors (i.e., how frequent the task is performed, how important it is, how difficult it is, and whether the team has to work on the task together). However, there is another subset of the TTA literature (i.e., cognitive task and work analysis) which has sought to pinpoint the knowledge and thought processes that may contribute to a team’s performance levels ( Schraagen, Chipman, & Shalin, 2000 ). Research that focuses on unpacking team cognition (e.g., transactive memory systems), particularly understanding how team cognition changes over time, will inform how TDIs are implemented and developed ( Kanawattanachai & Yoo, 2007 ; Lewis, 2004 ).
TTA Theme 2: the dynamic nature ofteam tasks mustbe accounted for in TTA.
As detailed earlier, researchers have started to coalesce in the way that team task features are measured in terms of the techniques used, the sources of information regarding the team’s task, and what features of the task are assessed. In our review of TDIs, we focused on one aspect, that is, the timing of when the TDIs we reviewed are typically implemented and discussed. In our review of the TTA literature, we found that such an intervention is largely discussed as a first step in terms of understanding a team, which is logical because a TTA provides an assessment of the team, the task, the context, and the team members. For example, Fowlkes, Lane, Salas, Franz, and Oser (1994) conducted a thorough examination of a training intervention with military helicopter and aircraft crews. To start, they conducted a task analysis to identify the specific actions that should be taken by aircraft personnel and then assessed the teams’ performance against such standard behaviors.
Conducting a task analysis at the beginning of the team’s life cycle is beneficial because it can allow for a more in-depth understanding of the team’s task which can be leveraged in determining what a team may need in terms of resources and/or development. Likewise, assessing the team’s task features at the beginning of the project may be in accordance with some of the seminal team effectiveness frame- works (e.g., the IPO framework) which consider task features as an input variable. However, such treatment implicitly assumes that the features of the team’s task do not change or evolve over time. This is unlikely to be the case for all teams. Specifically, the interdependence levels that may be observed at one point in time may not remain constant. In fact, based on changing environmental features or changes within the team, interdependence levels and other relevant task considerations may ebb and flow throughout the team’s life cycle. As such, we advo- cate for researchers to view TTA as a recurring pro- cess that may need to occur multiple times over the life cycle of a team.
Team Composition (TCo)
As mentioned earlier, TTA has often been discussed as the starting point for various other TDIs—training interventions in particular. However, TTA also in- forms discussions around how many individuals are needed for a particular task and what KSAs in- dividuals will need. In fact, Beersma, Hollenbeck, Humphrey, Moon, and Conlon (2003) found evidence that certain personalities within a team are better matches for certain task types. As such, TCo is a logical next TDI category to consider. TCo, the configuration of member attributes in a team ( Levine & Moreland, 1990 ), has been a central component in examinations of organizational team effectiveness for several decades ( Mann, 1959 ). However, within the current review, we examine TCo through the “lens” ofbeingaTDI andhowTCo as an intervention influences the inputs of the presented framework. As such, this provides unique insights as compared with those who have discussed TCo elsewhere ( Mathieu et al., 2008 ).
The research on TCo has focused on surface-level (overt demographic characteristics) and deep-level (underlying psychological characteristics) variables and the relationship between these variables with team processes and outcomes. More recent research in the area of team science has focused on TCo in terms of diversity in knowledge and disciplines (i.e., deep-level constructs) as this is a major concern in terms of understanding its impact on resolving complex scientific questions. A meta-analysis that examined deep-level composition variables and team performance found medium (ρ = 0.37-agree- ableness; ρ = 0.33-conscientiousness) to small effects (ρ = 0.21-emotional stability; ρ = 0.26-preference for teamwork). Although additional research is needed to understand TCo as a TDI, in particular across the life of team, we have synthesized the current research into several themes.
TCo Theme 1: changes in team membership impact both team processes and performance.
Mathieu et al. (2008) discuss how TCo has been operationalized using various features of the team’s makeup. In particular, in the TCo literature, composition can be calculated by a mean value or summary index ( Chen, Mathieu, & Bliese, 2004 ). Such an approach has been used with composition characteristics such as personality ( LePine, 2003 ) and various KSAs ( Cooke, Kiekel, Salas, & Stout, 2003 ), and these operationalizations of composition have been examined in relation to team processes and performance. Likewise, TCo researchers are also interested in the heterogeneity that may exist between team members on a multitude of features, including age ( Kilduff, Angelmar, & Mehra, 2000 ); functions within the organization ( Bunderson & Sutcliffe, 2002 ); as well as race/ethnicity, gender, tenure, personality, and education ( Jackson, Joshi, & Erhardt, 2003 ; Kirkman, Tesluk, & Rosen, 2001 ; Mohammed & Angell, 2003 ).
Although the decision regarding how to operationalize composition should be based on the team’s task (e.g., a research team may benefit most from team members who are experts in distinct nonoverlapping knowledge domains), it is interesting to note that research is limited which has considered various operationalizations simultaneously, and when they do consider various composition features, it is typically performed with either multiple heterogeneity scores or merely summary indices of various constructs ( Offermann, Bailey, Vasilopoulos, Seal, & Sass, 2004 ). Accordingly, it may be a fruitful direction for researchers to consider both summary indices and heterogeneity scores within single studies, given that Kichuk and Wiesner (1997) evidenced a multilayered story surrounding team compositional effects when considering both summary indexes and heterogeneity scores of team member personality.
TCo Theme 2: composition affects critical out- comes when it is considered at the initiation of a team.
The vast majority of studies that have considered TCo have done so with the mindset that TCo is set early in the team’s life cycle and will have downstream effects on team processes and ultimately on team performance. However, such a statement is not intended to suggest that the TCo literature is one dimensional. In fact, the TCo literature is quite diverse. For instance, work in this literature stream has looked at composition in a variety of ways including considerations of cognitive styles ( Aggarwal & Woolley, 2013 ), general mental ability ( Barrick, Stewart Neubert, & Mount, 1998 ), cultural diversity ( Gibson & Saxton, 2005 ; Kirkman & Shapiro, 2001 ), and emotional intelligence ( Jordan & Troth, 2004 ).
This diverse set of research regarding composition features has likewise been linked to a variety of team outcome variables including decision making effectiveness ( Devine, 1999 ), customer service ( Feyerherm & Rice, 2002 ), implicit coordination ( Fisher, Bell, Dierdorff, & Belohlav, 2012 ), team viability ( Resick, Dickson, Mitchelson, Allison, & Clark, 2010 ), task cohesion (van Vianen & De Dreu, 2001), and team performance ( Woolley, Gerbasi, Chabris, Kosslyn, & Hackman, 2008 ). That said, although research on TCo has been framed in terms of providing indicators that are most salient when selecting individuals to a team, more research is needed which specifically examines the methodology for picking team membership. For instance, Colarelli and Boos (1992) examined sociometric and ability-based membership decisions and found that sociometric workgroups that were able to pick their own teammates reported higher levels of communication, coordination, cohesion, and satisfaction.
Team Work Design (TWD)
TWD may not be thought of as an intervention by some, as it focuses more on the environmental attributes and conditions under which teams work ( Morgeson & Humphrey, 2008 ). However, when examining the elemental features of TDIs as previously presented, TWD can be used to address team needs in an intentional manner, it addresses the inputs of our framework, and as such provides a justification for the inclusion as a TDI in this review. Although the definition of work design broadly speaking refers to the structuring of and context in which tasks, responsibilities, and relationships are managed ( Hackman & Oldham, 1976 ; Parker, 2014 ), at the team level this refers to a “defmition and structure of a team’s tasks, goals, and member’s roles; and the creation of organizational support for the team and link to the broader organizational context” ( Morgeson & Humprhey, 2008 : 46).
Work design in teams, as it refers to the changes in team context (i.e., tasks, activities, relationships, or responsibilities), has been found to play a key role in several team processes and outcome improvements. The principles of sociotechnical systems (STSs) influenced the design of group work ( Parker, 2014 ; Parker, Morgeson, & Johns, 2017 ). In addition to the principles of STS, the job characteristics model (JCM) has also been the focus at the team level, meaning that jobs should be designed to have variety, autonomy, feedback, significance, and identity ( Hackman & Oldham, 1976 ). By designing work with these characteristics in mind, individuals experience meaning, responsibility for outcomes created, and an understanding of the results from their effort (Paker et al., 2017). The parallel development of the STS approach and the JCM led to a focus on autonomy and the development of autonomous work groups (a.k.a. self-managing teams). As we are concerned here with developing teams, our lens for this review is primarily centered on the fact that team design is focused on the team’s needs. Related to the effects of team design as an intervention, there have been significant connections between elements of task interdependence and team empower- ment as predicting team performance and outcomes ( Hollenbeck& Spitzmuller, 2012 ). More specifically, team design, through the use of autonomous work groups, has linked group autonomy with positive job attitudes, satisfaction, and commitment ( Parker & Wall, 1998 ). Scholars have explained that when teams experience structures that are compatible with their preferences for getting work done (e.g., autonomy and appropriate degree of interdependence), the team will be more likely to maintain motivation to complete the task at hand ( Hollenbeck, DeRue, & Guzzo, 2004 ). However, when teams experience design structures that do not meet their needs, they may become increasingly discouraged or may even leave the team ( Park, Spitzmuller, & DeShon, 2013 ). Therefore, we next consider some of the trends across this literature to better understand its important influences.
TWD Theme 1: TWD needs to address both team and taskwork.
For teams, the consideration of work involves not only the actual task to be performed but also the teamwork processes and states that may be pivotal for team needs. This is particularly important as teamwork and taskwork may influence one another under different circumstances. For example, in considering task interdependence, one view suggests that when teams operate in tasks designed with higher degrees of interdependence, teamwork processes become that much more important in predicting outcomes ( LePine et al., 2008 ). Alternatively, it has also been argued that teams may construct task interdependence as a function of the social interactions with other team members ( Wageman & Gordon, 2005 ). That is, instead of being an objective indication as to the degree of task interdependency, interdependence is viewed as being driven by the social experiences. A team member who has built very strong social connections may perceive greater levels of interdependence than a team member who does not have the same degree of social connections and networks ( Hollenbeck & Spitzmuller, 2012 ). Thus, from the view of considering work design as a TDI, it may be important to acknowledge that team members’ social relationships may facilitate and shape their perceptions of how their work is designed.
TWD Theme 2: TWD must address the balance of individuals and the whole team to achieve optimal effects.
Although work design research has typically focused on the impact of design on individual needs and outcomes, there has been a fair amount of attention to the team aspects as well, as we have discussed. However, the consideration of both team and individual work design is less understood but extremely important ( Park et al., 2013 ). Park et al. note this in their review of the TWD literature in relation to team motivation, highlighting the idea that what is meant by team-level work design is not merely the aggregation of member characteristics. Wageman and Gordon (2005) argued that task in- terdependence is based on the values of the team. The example they provide is one based on team members who hold egalitarian values. People who hold egalitarian values tend to prefer conducting work using more cooperative processes and would prefer reward systems where rewards are shared. This example illustrates that individuals can change their work design to maximize outcomes (e.g., increased motivation and trust, and reduced conflict).
Team Charters (TChs)
Gersick (1988) and Feldman (1984) suggest that the first meeting of a team has lasting effects on how the team functions. The initial meeting jump starts the development of group norms and processes that aid a team’s performance. Research on TChs, an intervention which focuses on the development of team processes and in turn the development of emergent states (i.e., mediators), is relatively scarce and is primarily focused on student project teams. Research has reported that when student teams establish ground rules and clarify expectations by using TChs, teams are more satisfied and perform better ( Aaron, McDowell, & Herdman, 2014 ; Byrd & Luthy, 2010 ; Mathieu & Rapp, 2009 ).
Sverdrup and Schei (2015) applied psychological contract theory to better understand the impact of TChs. Studies investigating psychological contracts have demonstrated significant effects on outcomes such as job satisfaction, organizational commitment, and organizational citizenship behavior ( Bal, DeLange, Jansen, & Van Der Velde, 2008 ; Conway & Briner, 2009; De Vos, Buyens, & Schalk, 2003 ; Deery, Iverson, & Walsh, 2006; Schalk & Roe, 2007 ; Zhao, Wayne, Glibkowski, & Bravo, 2007 ). However, this examination is primarily focused on the re- lationship between employee and employer. Sverdup and Schei (2015) on the other hand apply psychological contract theory to the relationship between team members. Although a TCh is a written document, Sverdup & Schei highlight that whether a team contract is actually a tangible product “a team charter will…influence the content and perceptions of the psychological contract in the specific team” (p. 454).
Research on psychological contracts has highlighted that contracts can be transactional or relational, with transactional contracts referring to highly specific exchanges of limited durations and relational contracts are more open ended and relationship oriented with limited specification of how the contract will relate to performance requirements (Rousseau, 1995). The effectiveness of the psychological contract is also measured in terms of its features ( Sels, Janssens, & van den Brande, 2004 ; Janssens, Sels, & Van den Brande, 2003 ). Sels et al. identified and validated six dimensions (i.e., tangibility, scope, stability, time frame, exchange symmetry, and contract level) of the psychological contract that they found to be strongly related to personal control and affective commitment. Sverdup and Schei focused their application of psychological contract theory by examining how contract breaches and fulfillment in teams may clarify what TChs should emphasize. In the following paragraphs, we highlight two themes that emerged when reviewing the TCh research.
TCh Theme 1: TChs influence processes and emergent states by establishing mutual expectations.
TChs are meant to provide a team with an opportunity to clarify expectations and obligations to the team and the team outcome(s). Sverdup and Schei (2015) highlighted the need of developing expectations and obligations that are linked to work effort and quality. Moreover, they found that these elements of a charter (in conjunction with defining how breaches and violations were to be handled within the team) allowed for healthy team development to occur throughout the team’s life cycle. Specifically, teams engage in a sensemaking process that allows for the team to handle the breach with patience instead of attaching a violation to the behavior. This finding further develops our understanding of how TChs actually function. In particular, the purpose of the TChs is to influence processes and emergent states by eliminating misunderstandings and clarifying how the team should function.
TCh Theme 2: team charter content requires critical independent and team consideration.
The content of the TChs is meant to map onto effective teamwork characteristics and behaviors (i.e., processes and emergent states; Hunsaker et al., 2011 ). Some common content addressed in TChs includes purpose/mission statements, operating guidelines, behavioral norms, and performance management processes. Mathieu and Rapp (2009) found a positive effect of using TChs which included a section that individuals prepared independently. The content of the charter affords the team the opportunity to engage independently and interdependently to develop their team-level norms and ground rules.
Team Performance Monitoring & Assessment (TPMA)
Although TDIs such as TChs influence the processes that teams engage in and TCo influences the team members of the team, teams can also benefit from intervening in the form of receiving periodic updates of their performance status. TPMA involves the capturing of both individual and team levels of processes and performance, preferably from a dynamic lens where continual monitoring is available throughout a performance episode ( Cannon-Bowers & Salas, 1997 ). As indicated within the goal-setting literature, this monitoring of team goals will aid teams in more effectively achieving their goals ( Locke & Latham, 2002 ).
The research on TPMA is not particularly sparse; however, it is heavily intertwined with the TT literature because the focus is on the measurement of performance. The literature would benefit from some distinction between performance monitoring and assessment and TT with a focus on team performance over time. An important consideration for team performance monitoring involves carefully attending to what is being monitored. As the most often facet of team, outcomes can be separated into two distinct sets: performance and affective outcomes ( Hackman & Morris 1975 ). Team performance outcomes are typically denoted by the assessment of the team’s accomplishment of assigned goals. The measurement of these outcomes can range from a simple checklist of predefined goals the team was assigned to accomplish to a supervisor’s assessment of a team’s accuracy and quality of work performed ( Rosen et al., 2008 ). We next offer a summary of some of the major themes regarding TPMA as an intervention.
TPMA Theme 1: team performance monitoring is multifaceted and multilevel.
Although providing teams with an assessment of their current team performance status is critical, it can be challenging to assess all components of team performance, especially the subjective nature of team processes ( Cannon-Bowers & Salas, 1997 ). For example, the assessment of team performance outcomes is typically related to the accomplishment of task/team goals. Conversely, and more challenging, affective outcomes target how the team feels regarding their teamwork experience. Some prominent affective outcomes include the team’s willingness to work together in the future, team satisfaction, and team member trust ( Mathieu et al., 2008 ). Although some may consider affective outcomes less important than performance outcomes, they have critical implications for teams that plan to perform together in the future.
By ensuring that teams are provided with or are able to monitor information regarding their current status both in terms of processes and performance at multiple points in time, they can continually adapt and adjust based on such feedback ( Dickinson & McIntyre, 1997 ). To address this, several different measurement approaches have been developed. This includes checklist style feedback instruments (e.g., behavioral observation scales, behaviorally anchored rating systems) that track the degree to which team members are performing both on processes and outcomes ( Salas & Cannon-Bowers, 2001 ).
TPMA Theme 2: performance monitoring and assessment can (and often should) be implemented with multiple mechanisms.
To fully capture the multilevel and multifaceted nature of performance, monitoring and assessment of teams most optimally will combine multiple mechanisms. Indeed, Dickinson and McIntyre (1997) argued that it takes a team to measure a team accurately. This argument has two implications. First, teams are constantly engaging in simultaneous dynamic processes; thus, it can be difficult for any single individual to keep track and record all the actions of a team ( Wiese, Shuffler, & Salas, 2015 ). For example, if using external raters [i.e., subject matter experts (SMEs)] to observe team interactions, having several observers available to measure a team’s processes and performance can help ensure that this wealth of information is adequately captured. Secondly, use of a single source (e.g., only team members and only supervisors) for ratings could result in biased/deficient/contaminated measurement of team variables. Therefore, it is recommended that a diversity of measurement sources is used. The number and diversity of sources one uses can be affected by a number of factors (e.g., the number of team members, complexity of the task, and the amount of interdependence required for task completion).
More recently, measures of processes that can be embedded in performance situations have become of interest to researchers and practitioners alike ( Shuffler, Salas, & Pavlas, 2012 ). For example, the scales used in the Targeted Acceptable Responses to Generated Events or Tasks (TARGETs) methodology allow even relatively novice observers to appropriately rate team behavior and provide targeted feedback ( Fowlkes et al., 1994 ). These rating scales are developed with the assistance of SMEs and target-specific observable behaviors, exhibited knowledge, and critical skills. By implementing tools such as TARGETS and other automated or simulation-based tools, it may be easier to reduce the human error element of performance management, providing more accurate and in turn more useful information back to teams (Kozlwoski et al., 2015). Indeed, this type of event-based measurement approach (e.g., TARGETS) has seen remarkable success in military teams and other domains ( Fowlkes et al., 1994 ).
Team Debriefing (TD)
Team de-briefs, or after action reviews (AARs) as termed in military contexts, are a form of TDI used for learning and improving from team outcomes, through both individual- and team-level reflection and learning. The goal of a debrief is to have individuals and teams engage in an activity of reflection by asking a series of questions for them to consider their most recent experience (i.e., simulated or real) and discuss lessons learned. In other words, the focus of a debrief is the team’s outputs and the processes/emergent states that may need attention to change future outputs. A key characteristic of debriefs is that this reflection must be conducted in a safe environment, absent fear of repercussion or retaliation, to be effective. As such, TD are defined as interventions that encourage reflection and self-discovery, target potential opportunities for improvement, and as a result improve the quality of experiential learning which thus improves team inputs, processes, and outcomes (Tannenbaum & Cerasoli, 2013).
The research on TD cuts across many disciplines (e.g., aviation, military, medicine, and education) and in its earlier forms was more atheoretical. Tannenbaum and Cerasoli (2013) delineated that debriefs are differentiated from other TDIs by the following elements: active learning, developmental intent, specificity, and multiple information sources. Active engagement of the individuals/teams involved in a performance episode ( Darling & Parry, 2001 ; Ron et al., 2002) is necessary for reflection to be considered a true debrief. Active engagement in reflection activities, such as debriefs, provides the team with an opportunity to think deeply about an event, engage in discovery (Eddy, D’Abate, Tannenbaum, Givens-Skelton, & Robinson, 2013) at the individual and team level, and plan for future performance. Debriefs must also have intentions to develop the persons involved in the work and their future performance. Another defining feature is that debriefs should be focused on specific events. The focus on specific events helps teams and in- dividuals develop future action plans and improve motivation ( Locke & Latham, 1990 , 2002 ). Multiple information sources are essential for an intervention to be considered a debrief because it provides more sources of feedback ( Kluger & DeNisi, 1996 ).
Research and implementation focused on TD have increased in the last several decades. A meta- analysis conducted by Tannenbaum and Cerasoli (2013) found that debriefs resulted in an average 25% improvement compared with control conditions (d = 0.66). Thus, although the evidence base for team debriefing is still relatively young, there is a solid foundation in terms of the impact of debriefs as a potential intervention for addressing team out-puts, so that future teamwork episodes may be more effective. Furthermore, debriefs are readily used in conjunction with TT, to gauge knowledge building after completed training exercises. Accordingly, assessing the efficacy of their integration with one another is an important consideration in relation to our framework. In our review of the literature, we identified several themes that inform our understanding of debriefs as a TDI.
TD Theme 1: there is a distinct différence between feedback and debriefs.
Ellis and Davidi’s (2005) work on debriefs has pointedly acknowledged the difference between debriefs and similar interventions such as feedback. Debriefs (and AARs) are considered learning based organizational interventions. Ellis and Davidi (2005) describe that the action of debriefing provides learners with an opportunity to engage in self-explanation and data verification and that feedback is a by-product of debriefing. More formally, feedback is information provided to an individual. From the perspective of a one-directional traditional model of feedback between a leader and subordinate, it is the influential figure, or leader, who provides feedback to the subordinate about their performance. Debriefs not only focus on the reflection of the outcome of a work period but also the processes involved with getting to that outcome.
Several studies have investigated the effectiveness of including feedback with debriefs ( Oden, 2009 ). In a study that compared the impact of debriefing only and audio-visual feedback plus debriefing, Dine, Gersh, Leary, Riegel, Bellini, and Abela (2008) found that performance outcomes on a CPR task did change, whereby there were significant improvements in performance when debriefing was combined with feedback. In a similar study, conducted by Edelson et al. (2008) , greater improvements in CPR performance resulted when feedback was coupled with a debriefing intervention.
TD Theme 2: debriefs inherently change the structural knowledge of a task.
An important stream of research on debriefs assesses the impact of the content of the debriefs. Ellis and Davidi (2009) examined the advantage of drawing lessons from failures and success during debriefs. The results indicated that when participants debriefed and examined their failures and successes, their performance on tasks that followed improved significantly. Qudrat-Ullah (2007) reported results that when individuals engaged in a debriefing activity they not only improved on task performance but also improved their structural knowledge of the task, developed heuristics to be used in the task, and were able to reduce their decision time. In a team-based study conducted by Smith-Jentsch, Cannon-Bowers, Tannenbaum, and Salas (2008) , the use of a guided debriefing activity was compared with the use of a traditional debriefing activity that was not well participated and followed the task chronologically. The study’s results indicated that the use of an expert model-guided debriefing activity developed more accurate mental models of the teamwork and im- proved teamwork processes and outcomes.
TD Theme 3. Debriefs are best used after a criticai period of team performance to encourage future team learning.
Given the nature and purpose of a debrief, they are inherently designed to occur after teams have worked together for a period of time, but they may be best used following a critical period of performance where subsequent skill development is most needed for future team effectiveness. The timing of debriefs in the literature has been primarily focused on the application of the debrief as it is embedded in a training program or post-simulated events and even in unique cases embedded within an actual organization. For example, Bethune et al. (2011) implemented a prebrief-debrief model into the surgical theater and found that briefings specifically highlighted potential problems, improved team culture, and led to organizational change. Debriefings unfortunately were not closely adhered to because it was difficult for all team members to attend, given other commitments and work load. What resulted was that the prebrief not only provided the team with an opportunity to discuss the upcoming patient case but team members also used this opportunity to integrate a debrief based on previous cases.
Robertson et al. conducted a study in which a pre-post test design was used in which a training program modeled after a crisis resource management had included a 30-minute video-based structured debrief as part of the training program. The study resulted in significant changes pre and post training to outcome variables (e.g., individual and team performance, and competence in handling obstetric emergencies). Although the research on debriefs has focused on the use of a debrief intervention at the end of a performance episode or embedded at the end of a training intervention, we believe research is needed that focuses on how the use of debriefs evolves over time.
Team Building (TB)
TB is a commonly applied intervention in organizations that focus on team processes and outcomes and can come in many forms that can range widely in terms of their reliance on scientific evidence (e.g., outdoor ropes courses and classroom-based activities; Klein et al., 2009 ). From a scientific perspective, TB originally began as a group process intervention designed to improve interpersonal relations and social interactions and has evolved to now include the achievement of results, meeting goals, and accomplishing tasks ( Klein et al., 2009 ). The typical model of a TB intervention, if grounded in theory, is one that incorporates one or more of four main foci: goal setting, interpersonal relations, role clarification, or problem-solving. Although there may be variance in how TB interventions are designed, effective TB typically follows a structured developmental process ( Salas, Priest, & DeRouin, 2005 ). This includes incorporating team members into the intervention process, ensuring that activities specifically reinforce one or more of the four foci, and providing a clear means for evaluating the activities and structure after implementation ( Dyer, 2007 ; Payne, 2001 ).
In terms of the evidence base, the quality of research ranges widely, as not all TB efforts follow this prescribed structure. However, the most recent meta-analysis ( Klein et al., 2009 ) demonstrates that when this structure is imposed, TB is effective for improving team outcomes (ρ = 0.31, omnibus test), and more specifically, the meta-analysis showed that TB was more effective for affective outcomes (ρ = 0.44) and process outcomes (ρ = 0.44); more effective when the component of focus was role clarification (ρ = 0.35) and goal setting (ρ = 0.37), and for larger teams (ρ = 0.66). Although we have data that do indicate that TB is effective, we still need to know more about this TDI, given its commonly misattributed role as a “catchall” for describing anything loosely classified as a TDI ( Shuffler et al., 2011 ). We next identify several critical themes that provide insights regarding this often-misunderstood TDI.
TB Theme 1. TB demonstrates the benefits of a multifaceted intervention approach.
Setting it apart from some of the other TDIs that are primarily focused on a single strategy or focus, TB has an inherent multifaceted approach. Although several iterations of the components of TB have developed over the years, as mentioned earlier, TB is currently viewed as a four-pronged approach, including (1) a goal-setting model, (2) an interpersonal model, (3) a role clarification model, and (4) a problem-solving model. Each of the four current components addresses a different purpose of TB.
The emphasis of the goal-setting approach is on setting objectives and developing individual and team goals. During this type of TB, team members become involved in actively planning how to identify and achieve goals ( Salas, Rozell, Mullen, & Driskell, 1999 ). TB interventions, which focus on the interpersonal relations component, emphasize increasing teamwork processes and emergent states, such as mutual supportiveness, communication, and the development of team affect ( Tannenbaum et al., 1992 ; DeMeuse & Liebowitz, 1981 ). Role clarification emphasizes increasing communication among team members in terms of their respective roles as a part of the team ( Salas et al., 1999 ). Finally, the problem-solving approach to TB is perhaps the most unique, as it subsumes aspects of all the components described by Beer (1980) . This type of intervention promotes team synergy through encouraging team members to practice setting goals, developing interpersonal relations, clarifying team roles, and working to improve organizational characteristics through participating in problem-solving tasks. Although each of these components can be beneficial to helping support teams, it is when they are combined together that they are most effective, as noted by Tannenbaum et al. (1992) in their review of the TB literature.
One reason that this approach may be especially useful is that it addresses unique yet complementary team needs and problems; for example, the incorporation of role clarification and interpersonal skill development may make it easier for team members to determine what roles they have, how these roles may fit together, and based on that role understanding, who they may need to get along with as a function of their roles. This may encourage members who have highly interdependent roles to focus on working together in developing interpersonal connections and relationships, which may be more successful than having all team members spending concerted effort on developing relationships where they may not matter. Although not always implemented together, these four complementary approaches do provide some insight as to the value of such an approach.
TB Theme 2: TB is most effective for affective-based team needs.
The meta-analytic investigation conducted by Klein et al. (2009) found that TB interventions were most effective when the targeted team outcome was affective in nature. For example, TB interventions that improved trust between team members or confidence. In addition, results of the meta-analysis also showed that TB was effective when the target of the intervention was to improve process outcomes (i.e., coordination, communication, and adaptability). However, the strongest and most consistent effects appear to be the more affectively driven states that are critical to teams, such as trust, cohesion, psychological safety, and collective efficacy ( Schwarzmann, Hease, & Tollefson, 2010 ).
It is important to note that following implementation, TB exercises are often evaluated only on the basis of affective or other subjective reactions, which may have implications in terms of why this connection exists between TB and affective outcomes ( Sims et al., 2006 ). TB is often judged on whether team members believed that the training was valuable or perceived as effective in changing team norms and processes. Therefore, at times it can be difficult to determine if TB exercises are truly effective at improving team processes and performance. However, as Klein et al. (2009) noted in their meta-analysis, there does seem to be a theoretically and empirically based value add in terms of the different aspects of TB working together to specifically address the affective needs. A critical point that Klein et al. highlight in the interpretation of their results is that a TB intervention must focus on what the team needs for effective performance. If trust is of utmost importance to the success of the team in the context in which they work, then TB intervention should focus on building trust and applying the lessons learned and skill development from the TB intervention to the context in which the team works.
Team Training (TT)
Salas and Cannon-Bowers (1998) appropriately define TT as a “set of theoretically based strategies or instructional processes, which are based on the science and practice of designing and delivering instruction to enhance and maintain team performance under different conditions” (p. 254). The purpose of TT is for team members to understand, practice, and obtain the KSAs required for effective performance while receiving feedback. Furthermore, TT provides an opportunity for teams to identify teamwork deficiencies and learn skills to address these deficiencies. Similar to individual training, TT involves identifying the optimal combination of tools (e.g., TTA), delivery methods (e.g., practice- based, information-based, and demonstration-based), and content (e.g., knowledge, skills, and attitudes; Salas & Cannon-Bowers, 1998 ).
Of all the research on TDIs, the evidence for TT is perhaps the strongest. In a meta-analysis by Salas et al. (2008) , TT was found to account for approximately 12 to 19 percent of the variance in the examined outcomes (i.e., cognitive, affective, process, and performance), with TT TDIs being more effective for team processes than for the other outcome types. Meta-analytic findings also uncovered several moderators; that is, the TT and team outcomes relationship was moderated by membership stability (ρ = 0.48 and ρ = 0.54, intact teams that underwent training improved the most on process and performance outcomes, respectively), large teams (ρ = 0.50, when team performance was the dependent variable), and small teams (ρ = 0.59, when team processes were the dependent variable). As there are several meta-analyses on TT ( Hughes et al., 2016 ; Salas et al., 2008 ), as well as numerous detailed descriptions of the different types of TT, we focus on providing a high-level summary of the extensive base of TT evidence.
TT Theme 1: TT can be structured in a multitude of ways while stili addressing the overall goal of teamwork skill development.
There are a number of strategies that have emerged in the literature of TT, including team self-correction, cross-training, and team coordination training. For example, cross-training is a TT strategy which trains each team member the duties and responsibilities of their teammates. The goal of this training strategy is to develop a shared understanding of the overall functioning of each team member’s role ( Blickensderfer, Cannon-Bowers, & Salas, 1998 ). Team coordination training targets the improvement of a team’s shared mental model framework. One specific TDI which targets the team’s ability to conduct effective after-action-reviews is guided team self-correction. Guided team self-correction is a team development strategy designed to enable teams to enhance their performance. Team self-correction involves developing the team’s ability to diagnose their behavior in terms of specific topics that should be discussed during debriefings and how they conduct the discussion of the specific topics identified ( Smith-Jentsch, Zeisig, Acton, & McPherson, 1998 ). It is expected that teams that engage in this type of team strategy are able to collectively make sense of their environment and to develop a shared vision for how they should, as a team, proceed in the future.
Research on guided team self-correction has demonstrated that it is able to improve both taskwork and teamwork factors. The theoretical underpinning of guided team self-correction is mental model theory. Mental model theory suggests that when team-mates hold similar cognitive representations of their taskwork and teamwork, they are better able to anticipate one another’s needs and actions, better able to engage in more efficient task strategies, better able to engage in sensemaking as a team, and better able to manage unexpected events during a team’s performance cycle ( Smith-Jentsch et al., 2008 ).
Given the breadth of literature in this area, we will not fully go in-depth on all of the different forms of TT here as they have been defined and described elsewhere ( Hughes et al., 2016 ; Salas et al., 2008 ). However, this further emphasizes the significant need for careful planning and selection to ensure that the most appropriate form of TT is used for a given team. In addition, much like with the multifaceted nature of TB, the multifaceted nature of TT also highlights the potential value in both the integration of multiple TDIs, as well as the need for attention to when each of these different training programs may have the strongest impact on a team’s development and growth over time.
TT Theme 2: TT is an effective multifaceted TDI, addressing numerous critical team outcomes and processes.
These training strategies have shown significant positive impacts on team cognitive, affective, process, and performance outcomes ( Salas et al., 2008 ). One of the most common types of team coordination training is that of crew resource management (CRM), which is designed to improve teamwork by teaching team members to use all available resources (e.g., information, equipment, and people) through effective team coordination and communication ( Salas, Burke, Bowers, & Wilson, 2001 ). CRM has been successfully used in many industries, especially aviation, health care, and the military.
Team self-correction focuses on teams exploring their processes and performance. When teams are able to explore their performance (i.e., affect, behavior, and cognition), they will be better able to develop a larger repertoire of knowledge (i.e., taskwork or teamwork knowledge) that they can choose from in the future. The creation of this larger repertoire of knowledge develops a more adaptable team. Therefore, if the team is faced with a future nonroutine task, teams that are more adaptable will be more capable of adjusting to these emergent situations and better able to manage, if not bypass, any role overloads. Given the complex and dynamic nature of modern work environments, adaptability is a desirable characteristic of individuals and teams ( Maynard, Kennedy, & Sommer, 2015 ; Smith, Ford, & Kozlowski, 1997 ).
Team Coaching (TCa)
Although it is clearly effective, some have suggested that TT alone is not sufficient to see behavior changes, and instead, TCa is likely to garner enhanced behavior changes ( Showers, 1987 ) as coaching is a means to sustain the results of various TDIs ( Neuman & Cunningham, 2009 ; Scott & Martinek, 2006 ). As a result of this belief, organizations have increasingly made substantial investments in means by which to develop managerial coaching (e.g., Redshaw, 2000 ). TCa as a concept was primarily introduced by Hackman and Wageman (2005) . In presenting their theory of TCa, these authors suggest (as we do here) that TCa is an intervention that is likely to be impactful at various points along the team’s life cycle (i.e., at the beginning, the mid-point, and the end of the project). As suggested by Hackman and Wageman (2005) , TCa is the “direct interaction with a team intended to help members make coordinated and task-appropriate use of their collective resources in accomplishing the team’s work” (p. 269).
In our search of the TCa literature, we found a stream of practical research that described case studies in TCa and applied examples of TCa as a training intervention. However, the science on TCa is lacking rigorous training evaluation with quantitative and qualitative methods, in addition to meta-analytic or systematic reviews of the literature. Although there are some exceptions, particularly in the health-care industry, more research is needed to understand the effect TCa has on sustaining TT results.
Coaching is an intervention that is often coupled with other forms of TDIs. In particular, some have posited that coaching best follows training interventions so that it can occur as individuals are implementing the skills learned during such training ( Scheuermann et al., 2013 ). For instance, Shunk, Dulay, Chou, Janson, and O’Brien (2014) coupled coaching with a multifaceted intervention that included TB, checklist development, and training intervention components that were collectively focused on the use of huddles within a health-care clinic setting. Specifically, health-care teams who were assigned a “huddle coach” were instructed on how to use the huddle checklist and served as observers of the team’s huddle. Similarly, Morgan et al. (2015) examined an intervention of orthopedic surgery teams that included CRM teamwork training and six weeks of on-the-job coaching, in which their joint effect demonstrated a positive impact on team nontechnical skills, as well as enhanced compliance with time-outs.
Likewise, Wilson, Dykstra, Watson, Boyd, and Crais (2012) compared interventions that included training and coaching compared with an intervention that just included training and found evidence that those that received both the training and coaching interventions had the largest positive change in their use of team planning and monitoring practices, as well as the largest amount of student goals attained. Interestingly, Sargent, Allen, Frahm, and Morris (2009) also linked training and coaching, but do so in a different way, namely, they examined the process by which teaching assistants received training on how to be able to effectively coach student teams. They conducted a quasi-experimental design comparing the performance of teams who were coached by teaching assistants that received the training versus those who did not receive the training. Their results point to the fact that coaches who were trained had teams that functioned better, had higher levels of productivity, and felt their coach was more effective as compared with teams whose coaches were untrained.
TCa Theme 1: results heavily depend on who is serving as the coach.
Based on our review of the TCa literature, one of the first big takeaways is the fact that who the coach is has a varied answer. For example, some have argued that it is important that the coach be an external resource because having an external coach work with the team may enhance team functioning. In part, this sentiment is based on the belief that an external coach can focus on how the team is actually working because in comparison to the team members and leader, an external coach is less likely to be preoccupied with team outcomes ( Reich, Ullmann, Van der Loos, & Leifer, 2009 ) and may be more objective ( King & Eaton, 1999 ). For instance, Shunket al. (2014) provide a study of the use of huddle coaches within a health-care context. In particular, these coaches were primarily physicians who received faculty development on the use of huddles and then the coaches observed subsequent team huddles and provided feedback on underlying teamwork skills. The results of this coaching intervention appeared beneficial as study participants felt that the efficiency and quality of patient care improved as a result of this TDI.
By contrast to this external view of the coach, others have approached the concept of coaching in terms of actions or behaviors that the team’s leader should provide. For instance, Rousseau, Aube, and Tremblay (2013) asked team members to evaluate their supervisors’ coaching behaviors (i.e., he/she sets expectations, encourages us to find our own solutions, and points out areas where we need to improve) and found that teams that had leaders who provided these coaching behaviors were more innovative as a result of the impact that coaching had on team goal commitment and support for innovation. Wageman (2001) also assessed the impact of internal leader coaching behaviors but categorized coaching behaviors as either positive (i.e., provides cues and informal rewards for self-managing behaviors and problem-solving consultation) or negative (identifying team problems and leader task intervention). In her study of Xerox service teams, Wageman (2001) evidenced that positive coaching behaviors exhibited by the leader was positively related to team self-management and quality of group processes, whereas negative coaching was negatively related to self-management and work satisfaction.
TCa Theme 2: a coach can serve in multiple functions to address different team needs.
In addition to who the coach is being an area of disagreement within the literature, it is also interesting to note that what the coach actually does for the team is also less than clear within the literature. In fact, Carr and Peters (2013) argued that “TCa has been loosely defined and used as an umbrella term that includes facilitation, TB, and other group process interventions” (p. 80). Specifically, some have contended that the coach can provide teams with assistance “that ranges from problem solving to moral support” ( Reich et al., 2009 : 205). In their seminal work on TCa, Hackman and Wageman (2005) outline three primary coaching intervention functions: motivational, which is focused on minimizing social loafing and increasing shared commitment; consultative, which pushes members to create work processes that are aligned to task features; and educational, designed to enhance team members’ knowledge, skills, and abilities. Clutterbuck (2007) built on the work of Hackman and Wageman (2005) and proposed that prominent coaching principles include reflection, analysis, and motivation to change. Some have suggested that coaching is a stage-driven process with specific steps around observing, acting, reflecting, and evaluating, ( Wilson et al., 2012 ).
By contrast, others have postulated that internal coaches need to exhibit behaviors such as “(1) soliciting and providing feedback, (2) empowering employees, (3) broadening employees’ perspectives, (4) transforming ownership, (5) communicating expectations, and (6) finding how employees’ work and tasks fit into the big picture” ( Hagen, 2010 : 793). However, although theoretical pieces have outlined these various ingredients of TCa, research has not adequately addressed these steps. In part, this may be due to the general tendency of TCa studies to not examine this form of TDI longitudinally. Granted, there are exceptions to this statement. In particular, Weer, DiRenzo, and Shipper (2016) examined 714 managers and their teams over a 54-month period oftime and examined two categories of coaching behaviors—facilitative vs. pressure-based coaching. They provide evidence of the positive impact that facilitative coaching has on team commitment, and in turn, team effectiveness. By contrast, pressure-based coaching negatively influenced team commitment, and thereby team effectiveness. In addition, Alken, Tan, Luursema, Fluit, and van Goor (2013) provide a roadmap for how future research could be designed to examine what team coaches actually do, namely, these authors coded the communications of instructors who were assisting (and coaching) 11 surgical teams. They outline that additional research is needed to understand how specificity of a coach’s communication may influence learning outcomes of learners.
TCa Theme 3: the target ofwho should receive the coaching can vary.
Related to what the coach does, another theme that emerged during our review is related to the target of the coaching. Specifically, much of the literature has focused on coaching interventions that are targeted to the team as a whole. This would be aligned with certain definitions of TCa which specifically state that the coach works with the entire team ( Hawkins, 2011 ). This approach is also assumed by the various studies that have not actually investigated TCa interventions but instead have examined the team member’s collective perception regarding the internal team leader’s coaching behaviors (Liu et al., 2009; Reich et al., 2009 ; Rousseau et al., 2013 ). However, several researchers ( Hawkins, 2011 ; Wageman, Nunes, Burruss, & Hackman, 2008 ) have alluded to the fact that it may be beneficial for an external team coach to focus their attention on the internal team leader to enhance the coaching capabilities that exist within the team. As such, future research may want to examine more closely coaching interventions that are primarily focused on shaping behaviors of the team leader and through the actions of this particular person, ultimately shape the entire team’s dynamics and performance. Similarly, more work could explore the impact of peer coaching within teams as the limited work in this area has demonstrated promising results ( Hackman & O’Connor, 2005 ).
Team Leadership (TL)
Définition and evidence assessment..
TL represents a key mechanism by which teams can be effective and, as such, has been broadly studied in terms of its impact ( Zaccaro, Rittman, & Marks, 2001 ). From a TDI perspective, we focus specifically on those interventions targeted at improving TL, to bound our review. Team leaders, whether one or several individuals, are responsible for defining team directions and for organizing the team to achieve progress toward their goal ( Hackman & Wageman 2005 ). The literature on TL interventions often takes the perspective that leadership is con- sidered social problem-solving and, as such, leaders must be prepared to determine when problems exist that may prohibit the team from performing their goals, create solutions to these problems, and implement solutions (Mumford et al., 2003; Zaccaro et al., 2001 ). The functional TL literature has focused on team needs and how leaders can fulfill those needs by engaging in particular behaviors ( Hackman & Wageman 2005 ; Morgeson, DeRue, & Karam, 2010 ).
The literature that addresses how to intervene and improve TL is quite extensive, with several examples of meta-analytic investigations on the topic. In a study with consulting teams, Carson et al. (2007) make an important contribution to understanding TL by highlighting that multiple team members can make contributions. Moreover, they highlight that the internal context in which teams operate are important determinants of TL. Burke, Stagl, Klein, Goodwin, Salas, and Halpin (2006) focused on identifying what behaviors may be most vital and, therefore, most likely to inform the content of TDIs for TL, finding that person-focused behaviors were related to perceived team effectiveness (ρ = 0.36), team productivity (ρ = 0.28), and team learning (ρ = 0.56). In our review of the literature, we identified several themes that connect the research base for TL interventions.
TL Theme 1: shared leadership is a particularly effective intervention for enhancing team outcomes.
As of late, the TL research has focused intensely on how sharing TL may impact team out-comes, especially what can be done to prepare team members to share leadership responsibilities as needed. Seers et al. define shared leadership as “the extent which more than one individual can effectively operate in a distinctively influential role within the same interdependent role system” (2003: 79). Wang et al. (2014) conducted a meta-analysis in which they examined the relationship between shared leadership and team effectiveness. They discovered that TL that focuses on change and development ( Contractor et al., 2012 ) is more beneficial to teams. That is, sharing in leadership functions that are oriented toward change (e.g., visionary leadership functions or innovative leadership functions) are more effective, in terms of outcomes, than sharing in traditional leadership functions among multiple team members. Wang et al. (2014) also reported meta-analyzed findings that demonstrated shared leadership are more related to attitudinal and behavioral outcomes as compared with performance measures.
Nicolaides et al. (2014) in their meta-analysis on shared leadership and team performance found that shared leadership explains unique variance in team performance more than that of vertical leadership. Specifically, shared leadership explained an additional 5.7 percent ( p < .01) of the variance in team performance beyond vertical leadership. However, much more needs to be investigated to understand how shared leadership and vertical leadership operate together ( Conger & Pearce, 2003 ) and across the team’s life cycle.
TL Theme 2: task type is an important moderator ofthe TL and team performance relationship.
Although we acknowledge the influence that leadership has on team outcomes, it is important to consider what moderators may exist in this relationship. Wang et al. (2014) examined the moderators of TL and performance and found that the task is a moderator to the relationship between shared leadership and outcomes. When teams work on tasks that are highly interdependent and knowledge based, a stronger relationship between shared leadership and outcomes was found. However, D’Innocenzo, Mathieu, and Kukenberger (2016) in a meta-analysis of the different forms of shared leadership and team performance relations found that complexity of team tasks related negatively to the magnitude of shared leadership-performance relations.
In another meta-analysis on shared leadership and team performance, Nicolaides et al. (2014) found that when task interdependence was high, a strong correlation between shared leadership and team performance was produced. Burke et al. (2006) also examined the moderating influence of task on team performance and found that their results do suggest that leadership in teams is more impactful to team performance when task interdependencies are higher; however, the authors do note that their finding was based on a small number of effect sizes and should be interpreted with caution.
TL Theme 3: team leaders must provide different forms of support over time to meet changing team needs.
Perhaps, the most critical role of team leaders as an intervening mechanism is to influence and fulfill the needs of the team, whatever they may be at any given point in time. To better organize what this might look like, Morgeson, DeRue, and Karam (2010) developed a framework which specified the behaviors in which team leaders engage to lead teams through their life cycle. Grounded in Marks et al. (2001) temporally based framework of transition and action phases, Morgeson et al. identified critical leadership functions in the transition phase of work (e.g., defining the team’s mission, establishing expectations and goals, and structuring and planning the work conducted by the team) as well as the action phases (e.g., challenging the team, performing the task, solving problems, and providing resources).
As these models demonstrate, over time team needs inevitably change, and, therefore, TL functions must change along with the dynamics of the team. Nicolaides et al. (2014) in their meta-analysis noted that team tenure interacted with the shared leadership and team performance relationship. Their results indicated that as team tenure increases, the relationship between shared leadership and team performance weakens. One explanation that Nicolaides et al. offer is that team members may not be able to sustain the sharing of leadership functions over a long period of time because of power struggles or conflict arising. Thus, in this case, the sharing of leadership may be a less effective intervention as compared with other TDIs.
SYNTHESIS AND CONCEPTUAL FRAMEWORK
Before exploring the deeper results of our thematic analyses through the presentation of our framework, we provide an initial assessment of the quality and quantity of research regarding TDIs. First, our grouping of articles by the names, categories, and types of TDIs that were systematic across the literature resulted in a set of ten major types. These 10 TDIs were identified as most commonly occurring in the literature and subsequently were agreed as giving the best representative understanding as to the state of the science. Within our review of each of the TDIs, we identified various themes that emerged; Table 1 serves to synthesize these overarching themes. Table 2 provides a summary of the TDIs, in terms of key definitions for each; furthermore, while we later provide a detailed state of the science for each, Table 2 also includes a listing of major systematic reviews, meta-analyses, and other key sources useful in further exploring each type of TDI.
Emergent Themes in the Team Development Literatures by Category
Team Development Interventions: Definitions and Exemplar Sources
Second, in examining the body of literature, there were some broader trends over time that are worth noting. Figure 1 offers a representation summarizing the sources as organized by their publication dates. For each type of TDI, we identify the total number of relevant sources as distinguished by year with the color coded layers of the bars. Overall, given the smaller numbers, we grouped articles by decade up until 2000. However, starting in 2000, we grouped sources by every 5 years, as the numbers dramatically increased, especially for TT, which had the highest number of publications. This is likely due to the increased availability of TT tools and resources, such as Team STEPPS for health care ( Hughes et al., 2016 ).

TDIs: Literature Review Results by Publication Date
TB is interesting to observe in terms of publication trends, especially in comparison to TT. Both terms are often used to describe a broader array of TDIs, yet while TT has steadily jumped in publications, TB has leveled off since the turn of the century. One reason for this may be due to the distinction of the other types of TDIs that might have previously been grouped as TB for simplicity sake. Further, the rise of more systematic and clearly defined TDIs may make it more challenging to publish TB research that is not as structured; indeed, many of the early studies were case study approaches that may now pale in comparison to the more rigorous approaches offered in evaluating other TDIs such as TT, TCo, and TL. However, by the beginning of the 21st century, most of the empirical evidence has focused on field and laboratory studies, involving pre- and post-test as well as control group designs to assess TDI efficacy. Further, the growing use of meta-analysis and systematic reviews may also help to define and distinguish different TDIs, or at least call more attention to the distinctions in the past.
A final yet important theme that was quite clear, and was discussed for each of the different TDIs individually, regards the variety in terms of the quality and quantity of the existing empirical evidence. Not surprisingly, TDIs emerging more recently, such as TChs, had lower quantity in their empirical base overall, yet seems higher in quality. TChs have, in large part, been assessed using clear quasi-experimental and experimental designs, with several being longitudinal in nature. Further, the publication rates in the past 5 years are relatively even for some of the TDIs emerging in the last decade, with team debriefing, composition, and coaching all at about the same pace of publication, and TL also demonstrating an increasingly higher number of publications. TT demonstrated the most growth in the number of publications from a pre-2000 to post-2000 perspective; indeed, the number of studies published on TT in the first decade of the 21st century was higher than the total number of the studies published on TT before 2000. Not surprisingly, these more prolific publication numbers are also associated with meta-analyses & systematic reviews for TT, TB, TCa, TL, and interestingly, team debriefing. Overall, more systematic approaches to defining TDIs seem to be emerging.
An Emergent Heuristic for Identifying and Developing Effective TDIs
In addressing the need for a definition of TDIs ( Need 1 ), our review revealed that it is at times difficult to discern at a surface level what actually is needed for an effective TDI. That is, how do we recognize and avoid actions thatmay on the surface look like a TDI but have no actual impact, and instead focus on TDIs that systematically result in changing the trajectory of a team for the better? Importantly, we wanted this distinction to rely on the empiricalliteratuře to drive clear, evidence-based guidelines. In reviewing the literatuře across TDIs, a core set of characteristics emerged that appear to guide a path toward distinguishing effective TDIs from those TDIs that do not actually change teams for the better. Overall, TDIs linked to important team outcomes such as enhanced processes and performance dem- onstrate five features: (1) the focus of the TDI is on a real, team-relevant need(s); (2) the TDI is in response to emergent team needs or is implemented in anticipation of future needs; (3) the TDI involves active engagement of team members and/or others with knowledge of the team; (4) the direct impact of the TDI on team need(s) occurs at one or more points in time during the team’s life span; and (5) the TDI is intentionally implemented via a systematic set of strategies and tools appropriate for the team needs.
Serving as a relatively simple heuristic that can aid in translation to practice, we leverage a “what,” “ why,” “who,” “when,” and “how” approach to walkthrough these different core features. This heuristic should be especially memorable as they essentially shape the key questions that can and should be asked and answered when determining the most effective TDI or combination of TDIs. Although some of these features may inherently vary more or less across TDI categories, we do not offer a specific classification of the different TDI categories. This is intentional to prevent further separation in an already disjointed field, and also because some TDI types do not consistently fall in one area or another for certain features. However, we do leverage examples from the literature to help in explaining the value in each feature as an essential part of defining effective TDIs.
“What” is the actual needfor the TDI?
The first elemental feature that can be used to distinguish effective TDIs is seemingly simple—an effective TDI must actually meet some need that is not otherwise being met by the team itself. Although this initially appears straightforward, the multifaceted nature of what is needed can quickly become muddied. The quintessential part of this need is the assumption that the need exists as part of achieving team effectiveness. As team effectiveness can consist of numerous factors (e.g., objective performance, satisfaction, viability, learning, customer satisfaction) and operate across multiple levels (i.e., individual, team, organization; Salas et al., 2007 ), team needs may be many. For example, the degree to which team processes, or how the team actually performed the tasks, are maintained, weakened, or strengthened during interaction should be assessed. Using this multidimensional view, TDIs may be targeted to impact team processes, states, performance goals, and learning, at either the individual or team levels.
As a second important layer to this elemental feature is that when we say TDIs have an “impact” on the team, this is not meant to imply that TDIs are only focused on increasing functional processes within a team ( Shuffler, Jimenez, & Kramer, 2016 ). In fact, given that there are also teamwork factors that can be dysfunctional in nature, the need that a given TDI may be addressing could be to reduce certain dys-functional teamwork factors. Thus, not all of the needs being addressed by TDIs mean that more is better—instead, the TDI should have an impact that is in the appropriate direction for that particular type of need.
“Why” is a TDInecessary?
Although the previous discussion focused on the type of outcome that is being impacted, our next key feature of effective TDIs addresses the reasoning behind the intervention in the first place. Although we may know what the need is, it is also important to consider whether this need is more emergent in nature, potentially arising un-expectedly and requiring teams to react, or if it is implemented in anticipation of future needs, setting a team up for future success or cutting off the chances of unexpected breakdowns. On one hand, some effective TDIs are inherently derived and implemented as a means to specifically and proactively: (1) reduce the likelihood of critical team problems or needs emerging in the future, or (2) encourage well-functioning teams to achieve further synergy or process gains that will advance them to a higher level of performance (Hackman, 2003). TDIs such as cross-training can provide a pre-emptive view of what a team may need to be prepared for, either to anticipate where a future coordination failure may be most likely, or to allow for enhancement of already effective coordination processes ( Blickensderfer et al., 1998 ).
Yet as we have highlighted, teams are not simply successful from the beginning. Process loss and team derailment occur when teams are unable to achieve their goals due to interpersonal conflict (Sims & Salas, 2007), inability to adapt to change ( Burke et al., 2006 ), or similar breakdowns in team competencies and skills. From this view, some TDIs may be more inherently attuned to addressing more reactive team issues, such that they are designed to fix team issues before they further escalate. This does not mean that all TDIs that are reactive in scope are frantically thrown together or addressing unanticipated needs. Indeed, TDIs that could be considered reactive, such as debriefs that occur after the loss of a patient may be designed in advance so that they can be used during a period of process loss (Tannenbaum & Cerasoli, 2013). However, they are not necessarily appropriate to implement if there is nothing yet to react to— indeed, by its nature a debrief is not possible until a team has had a chance to work together. In sum, much like a patient whose symptoms will not improve without seeing a doctor for a diagnosis and prescription, teams who are already struggling to perform can benefit with the right TDI that is designed to react to their problems. Similarly, as a healthy individual still needs a regular checkup to fine tune health habits for well-being maintenance and improvement, even well-functioning teams can benefit from proactive TDIs that preemptively address potential future needs or challenge them to move beyond the current status quo.
“Who” is involved in the TDI?
We continue the health analogy as we explore who it is that is involved in TDIs. Essentially, organizations, leaders, consultants, and teams often find themselves in the metaphorical role of the “team doctor.” They are responsible for carefully diagnosing the symptoms that are creating team dysfunction, as well as the symptoms that may promote their functioning, with some symptoms being much more obvious than others. With this holistic understanding of the symptoms, they must then select and implement the right prescription of TDIs.
But who exactly is the doctor for teams? It can vary based on the intervention, and even may vary within categories of interventions, albeit usually to a lesser degree. From one view, bringing in an outside perspective can be seen as a beneficial way to develop, implement, and evaluate TDIs as it may provide a more objective perspective, as well as allow for the incorporation of SMEs well versed in the TDIs they are implementing ( Cannon-Bowers et al., 1995 ). However, other interventions rely heavily on the team members themselves to contribute to the diagnosing and intervention design. For example, TB ( Dyer, 2007 ) requires critical input from the team with regard to its needs before any intervention design and implementation.
Other factors may also drive the “who” aspect. TDIs such as TB that are most effective when they engage a consistent set of team members in the design and implementation process may not be the most appropriate for teams with regular and rapid turnover of members. Instead, an outsider or team leader may be more beneficial for identifying individual teamwork skills that are quickly trained and can be transportable, such as in aviation’s CRM program ( Wiener, Kanki, & Helmriech, 2010 ). In this form of TT, the focus is on the individual, where transferable teamwork skills are developed that can be applied to a wide range of teamwork environments, a crucial need for aviation crews that regu- larly rotate on a daily basis. Other TDIs are more holistically focused at the team level, whereby the goal is to focus on addressing the collective needs of the team, such as with TChs that are designed to help lay out and form the structure of the team as a whole ( Mathieu & Rapp, 2009 ).
“When” is the TDI needed?
The focus of this fourth elemental feature is perhaps one of the most critical yet least explored empirically. As teams are formed to achieve some goal or higher order purpose, it is only logical that they will begin to change, grow, and develop over time as they interact to achieve this goal. To have any impact on a team, at the very basic level a TDI must be applied at least once to a team, in whatever form that application or approach may be (as will be discussed next).
However, timing and temporality are much more complex for teams. First, there is the view of team development over time, outside of any specific intervention. As we previously mentioned, several viewpoints have been published in the literature on how teams develop (i.e., linearly, or via or via punctuated shifts). Historically the use of the IPO model advanced our understanding about team functioning, but more recently Marks et al. (2001) leverage the IPO framework to note that not only may teams go through cycles, their cycles may vary in their temporal rhythms, which may even vary within teams working on different tasks. This framework is a critical recognition of the cyclical nature of team-work, presenting some initial guidance as well in terms of what processes may be enacted in these different cycles. Finally, Kozlowski et al. (1999) also leverage this cyclical approach to specifically address team development, whereby needs change for teams as they are moving forward. This framework posits that team development is actually a process of compilation. That is, teams develop as a process where skills progress relatively linearly, but this progression is punctuated by transitions as skills are mastered and the team shifts their attention to the development of more complex knowledge and skills.
As such, to be effective, it is important to consider proximal and distal views in terms of when a particular intervention may be most appropriate. From a more proximal view, the current point in a singular performance cycle may help inform TDI selection, such as using a debrief at the end of a performance cycle instead of the beginning. Further, the more distal view of time can also inform how TDIs may need to change as a function of how the team is changing. Taking such a view would allow researchers to consider how either the intervention itself must change, or how the content of the intervention may need to shift over time. For example, while teams may need more hands-on guidance to shape skill development early on, as they become more experienced, leaders may actually switch to more of a coaching role, serving to offer more limited guidance. Overall, these timing issues can become quite crucial to TDI selection and implementation, and require further attention.
“How” will the TDI be implemented?
The final elemental feature of effective TDIs taps into what is largely Need 3: how do we go about integrating and developing effective teams? In our view, TDIs are not actions that are taken by happenstance that alter the team’s performance. Instead, we consider TDIs to be intentional for the specific needs of the team. The intention behind this is to reverberate the need for TDIs to focus on the team needs with an intentional purpose. All too often it is easy for a leader or organization to want to participate in some TB or TT exercise without fully knowing why it would be useful. This lack of a clear objective matched to the TDI creates the potential for the intervention to be viewed as useless or a waste of time—as more often than not, it probably is a waste ( Payne, 2001 ; Salas et al., 2005 ).
From a simplistic viewpoint, the answer to this “how” of TDIs is essentially best determined by posing the earlier four elemental features as questions whose answers can guide the selection of the right type of TDIs for a given situation. That is, how TDIs are best implemented is essentially contingent on what the team needs (and how many different needs they may have), if those needs are more proactive or more reactive in nature (the why), who is willing and able to be involved in the intervention design, implementation, and evaluation, and when the intervention should be implemented in respect to the temporal dynamics of the team.
An Organizing Framework for Integrating TDIs
Although the heuristic described earlier offers a means for addressing Need 1 (Defining TDIs), Need 3 (Integrating TDIs) becomes all the more prevalent. Indeed, this heuristic guides us down the path toward selecting one effective TDI based on one team development need. However, in reality, teams may face many developmental needs simultaneously. As a result, multiple effective TDIs may be best for addressing these different needs, yet our review found few theoretical and empirical linkages to help explain how to integrate TDIs in any systematic way. Although each individual TDI has a role in contributing to team effectiveness, it is not clear from the existing literature how these different roles may be coordinated ( Salas et al., 2015 ).
As such, we next offer movement toward an organizing framework that conceptualizes how different TDIs can work in conjunction with one another to dynamically meet multiple developmental needs. This framework, as represented in Figure 2 , builds on our review of the TDI literature, the aforementioned “effective TDI” heuristic, connecting elements from it with three key frameworks from the team effectiveness literatuře: the structural IMOI model ( Ilgen et al., 2015 ; McGrath, 1964 ), the temporally driven perspective of team dynamics ( Marks et al., 2001 ), and the team development needs model (Kozlowski, et al., 1999). From this foundation, we offer our framework to define the key structural elements contributing to team effectiveness over time, whereby multilevel inputs, mediators, and outcomes may create a need to improve, sustain, or maximize effectiveness. We then discuss how different TDIs may be more responsive to certain developmental needs and what the resulting implications are for integrating TDIs when multiple developmental needs are present.

A Dynamic, Integrative Framework of Team Development Interventions

Overarching framework structure.
First, our framework is driven by the IPO conceptualization that team effectiveness is best considered in systems terms; that is, inputs from different levels (e.g., organizational, team, and individual) influence team processes, which lead to measurable outcomes. Advancing this systems view, we shape our structure around the updated IPO, the input-mediator-output-input (IMOI) approach proposedby Ilgen, Hollenbeck, Johnson, and Jundt (2005), which incorporates a feedback loop to recognize that outputs can change the inputs that will feed into another performance cycle for the team. From this structural perspective, TDIs can be viewed as both (1) contributing to the shaping of inputs, mediators/processes, and outcomes and also (2) serve as inputs, mediators/processes, and outcomes themselves, in turn affecting future development and advancement. Furthermore, we can also use this structure to begin to map out how different developmental needs may be associated with different inputs, processes, and outputs, and how they may change over time, especially in response to different TDIs that are applied.
Team development needs and temporality.
Next, although the nature of our figure may seem somewhat linear at first glance, team development over time is undoubtedly dynamic ( Cronin, Weingart, & Todorova 2011 ; Humphrey et al., 2011 ). Likewise, teams may pass back and forth among these phases throughout their life cycle, per the temporal patterning noted by Marks et al. (2001) and indicated by loops throughout our framework that connect the IMO components. Furthermore, not only do teams go through different temporal rhythms as they work toward team goals, the nature of temporality is such that the team inevitably will develop as a function of working together over time (Kozlowski et al., 1999). Accordingly, different team needs may arise for development, both in terms of needs specific to inputs, processes, and outcomes, but also as a function of the state of team development overall. That is, newer teams with less experience with one another will face different developmental needs than those who are well established, have been through multiple performance episodes, and are working to move to a higher level of performance (Kozlowski et al., 2006).
We highlight this in the Developmental Needs component of our framework, with exemplar developmental needs for teams as they form, as they work to sustain good performance, as they try to improve their current level of less than desirable performance, or as they look to move to a higher level of performance. Although we do not intend to describe every single team developmental need, as this is outside of the scope of this review, drawing on Kozlowski et al.’s (1999) framework of team development over time and the broader IMOI literature on teamwork, we can offer exemplars of team development needs that may be critical for consideration. For inputs, developmental needs as team form are likely to focus on getting to know one another and building relationships, whereas later improvement and sustainment developmental inputs are driven more around how the team may be changing as a response to subsequent performance quality. Similarly, for processes, team developmental needs are initially around setting the right behavioral, cognitive, and affective patterns needed to accomplish goals and understanding how team members need to work with one another in their roles (Kozlowski, et al., 2006). Later on, process needs are more focused on making adjustments to maintain functional processes and reduce dysfunctional processes ( Shuffler, Jimenez, & Kramer, 2015 ). Finally, output developmental needs essentially focus on the use of outcomes as a reflection point, with early reflections being more about recognizing individual developmental needs necessary for enhancing future performance, and later developmental needs being driven by what will help the good of the team and the individual combined.
Integration of TDIs.
One of the more inherently important and novel aspects of our framework is in linking the mapping of TDIs to inputs, processes, and outcomes. In our framework, we first present exemplar TDIs, mapped from the categories we identified in our review, to inputs, processes/mediators, and outputs. These are modeled as such based on the literature mapping these different TDIs as having the strongest impacts on the components within each of these three areas. However, as some TDIs have demonstrated more overarching effects whereby they can positively influence not just one category but several factors within three IMO components, we deem these “multifaceted” TDIs. By framing TDIs from this perspective, it begins to become more clear in terms of how different interventions may be valuable not only in isolation but also in conjunction with other TDIs.
For example, a team facing multiple develop- mental needs regarding communication could initiate a TDI focused on inputs before a performance episode, such as articulating the team’s shared norms regarding team communication via a team charter intervention. Once they are in a performance episode, a mediator-focused intervention may be pursued such as assessing and monitoring the communication approaches that are being used within the team. In addition, the team may see value in considering the team’s outcomes by performing a team-debriefing intervention to assess communication strengths and weaknesses. Finally, the team may want to use interventions that can be used to impact root causes of performance trajectories across the IMO subdimensions. For instance, a TT intervention could focus on how TL behaviors need to be altered (input variable) or on how the team could enhance team communication by more effectively handling critical conversations (mediator variable). Together, these interventions will likely achieve much more in terms of impacting performance trajectories than what they might alone.
Trajectory movement as a key outcome.
One other important temporal aspect to note that is different from other IMO frameworks is our focus on performance movement as our overarching outcome of interest. As our review revealed the focus of TDIs to primarily be on changing team performance trajectories, it is most appropriate to incorporate this as the outcome of interest in our framework. We use this performance trajectory terminology to more accurately represent the dynamic nature of performance in teams in relation to team development, as a single performance episode is not necessarily the end goal ( Marks et al., 2001 ). Instead, teams may go through multiple performance episodes, where they start from a baseline level of performance that can then be (1) sustained to maintain a steady performance state; (2) improving an upward trajectory, in terms of achieving higher levels of performance than in the past; or (3) declining in a downward trajectory, with performance decreasing because of process loss or other failures of the team. Over time, identifying these upward, downward, or sustaining patterns of performance play a key role in understanding when TDIs may be needed.
EVOLVING OUR TDIs: DIRECTIONS FOR future RESEARCH and practice
Enhancing processes and performance in teams is no simple feat and we do not expect that a shift in how we research and implement TDIs will happen overnight. However, it is critical for the good of the field and the benefit of organizations to better understand how to use TDIs effectively. Although research suggests that the aforementioned types of TDIs are effective, we have highlighted major needs in our prior ways of thinking about TDIs. However, we have also provided guidance as to how these needs can be addressed to evolve our theoretical and empirical capacities to better match the dynamic and complex reality of teamwork today. As we move forward, the study of TDIs may best be conceptualized as an action science, whereby the research produced can generate knowledge that is actually implementable and meaningful ( Argyris, 1996 ; Argyris & Schon, 1996 ). Given the potentially enormous value for organizations, teams and individuals, such a focus will enable clarity and encourage parsimony in a rather disparate body of work.
Throughout this review, we have outlined numerous recommendations for future research and practice. Indeed, our themes, heuristic, and integrative framework all summarize critical areas for future research and practice alike. Thus, we do not intend to rehash all of those points within this section. Instead, assuming that researchers and practitioners will embrace this dynamic, integrative take on TDIs, we next provide a few final thoughts regarding aspects for consideration and potential methodological approaches that may advance research, as well as some final recommendations for practitioners in encouraging the use of a more integrative, scientific approach to TDIs.
The Role of Context in Future TDI Research
First, as global expansion and technological advances continue, teams are changing in terms of distribution, incorporation of virtual tools, and diversity in composition ( Connaughton & Shuffler, 2007 ; Kirkman & Mathieu, 2005 ). Moreover, technology has complicated the role of the individuals and teams in most complex work systems. Teams are responsible for accomplishing more cognitively complex tasks, which require them to plan, decide, remember, make decisions, solve problems, and generally think as an integrated unit ( Cooke, Gorman, & Rowe, 2008 ). It is unclear how these contextual issues impact our view of team development and the application of team interventions. Therefore, it is important that future research attend to these differences in terms of understanding their implications for TDIs. Although current team practices may work for promoting gains in team process and performance, it is very possible that the incorporation of these factors add a new level of complexity that must be accounted for in design and delivery of interventions. For example, although most TB interventions occur in face- to-face settings ( Tannenbaum et al., 1992 ), when team members are a part of a multinational organization that is spread across the globe, such a face-to-face interaction may not be possible. Furthermore, the affective and cognitive needs of these types of teams may vary from traditional teams. Therefore, considering the implications of globalization, technology is necessary for future TDI research and determining its impact on team effectiveness.
Methodological Considerations for Future TDI Research
Another perspective for consideration in future research is leveraging advances in methodologies to meet the call for more integrative research. One area that future research can choose to develop is examining teams from a profile perspective. That is, profiles can be considered as subgroups within a population that share a similar pattern across a set of multiple variables (Bauer & Shanahan, 2007). Prior research has used profiles in studies of individuals, and more recently, studies of teams, as a means for identifying how the integration of multiple constructs contribute to overall effectiveness ( Marsh et al., 2009 ; O’Neill et al., 2015). Thus, profiles can be generated at any level of analysis, ranging from the person-centric to much higher levels (e.g., team, multiteam system, and organization). The profile approach may provide a unique advantage to teamwork in particular, over simply considering the effects of different constructs in isolation, by permitting examinations of the interplay among complex teamwork phenomena.
This use of profiles may be particularly beneficial as we move toward more integrative approaches to better address real-world organizational needs and, most importantly, provide better interventions for teamwork. Specifically, teams that have similar patterns across multiple indicators can be grouped together as a descriptive category representing sub-groups that display a particular set of integrated factors (e.g., high trust, high cohesion, low conflict vs. low trust, low cohesion, and high conflict). Furthermore, these profiles can be dynamic in nature, adjusting as the team’s interactions further develop over time (e.g., moving from a profile of high trust, high cohesion, and low conflict to a profile of low trust, low cohesion, and high conflict during a poor performance episode). In turn, being able to track how and when a team may start to spiral either into a more effective or less effective (e.g., upward or downward) team based on their profile shifts may be critical and even necessary for accurately assessing team needs from a developmental perspective. For example, if we understand the role of trust as part of team profiles, identifying decreases in trust may simultaneously predict when other variables may also decrease in relation to this lowered trust. That is, profiles may allow for a more concise view of team-work dynamics that will enable organizations to better determine when interventions may need to be applied, perhaps even before the team itself recog- nizes its own needs.
There are additional methodological considerations to be addressed with future research. For example, using the experience sampling method will incorporate a methodology which asks participants to stop at certain times during their work and make notes of their experience in real time, this will allow us to understand how teams, individuals, and con- text change over time and how challenges can be resolved by TDIs. Last, one method that should be highlighted in the name of our call to understand the dynamic processes that teams experience is growth modeling. In the context of TDIs, the focus of growth modeling would be to understand the pattern of change in teams over time ( Collins & Parker, 2010 ). To be more specific, as detailed in Figure 3 , numerous research questions can be considered when viewing TDIs over the duration of the team’s life cycle. Specifically, does Team 1 in Figure 3 require fewer TDIs as a result of implementing a TDI early on in their life cycle? Similarly, is the timing of actually implementing a TDI pertinent? Consideration of such a research question would allow researchers to more fully examine whether a team can do irreparable harm by waiting too long to implement a TDI and whether TDIs can be implemented too soon or too often within a team. This later research question can be visually appreciated with Team 2 in Figure 3 which is being exposed to multiple TDIs. Within such a team, it would be necessary to examine if the length of time or span between TDIs has an impact; it also begs the question of the sustainability of effects for TDIs.

Temporal Considerations for Team Development Interventions
Growth modeling and similar time-focused analysis, such as latent transition analysis for detecting profile changes over time ( Muthen & Muthen, 2000 ), can serve to better address two major aspects of temporality as discussed in our review. First, using growth modeling, we can develop a better understanding of how teams change over time in general, which may provide a clearer picture as to the different needs that should be addressed in teams, leading to a more straightforward selection of TDIs. Second, such growth modeling and transition analyses can also map the trajectories of how teams respond after the implementation of one or more TDIs, supporting from a research perspective the potential to more cleanly explore how TDIs can be implemented at multiple points over a team’s life cycle rather than just at one particular point. Overall, the leveraging of such more advanced methodological approaches can serve to meet our call for an evolution in the TDI literature.
Final Thoughts on Directions for Practice
From a practical perspective, a dynamic, integrative evolution of TDIs as represented herein should help to determine when different approaches may be most beneficial across the life cycle of a team. Furthermore, the themes identified within each of the different TDI categories serve to guide practitioners as to an initial starting point for exploring the areas where some integration of TDIs has already occurred (e.g., TB and TCa), as well as to begin to better understand when and how different interventions may be most useful (e.g., TB for affective needs, TWD for motivational needs, and TT for process needs). Given that not all teams are able to fully incorporate every possible type of intervention in their development, these themes and framework should aid in providing clarity in terms of which specific interventions may be most relevant at given points in a team’s life cycle.
The “effective TDI” heuristic and organizing framework may assist practitioners in focusing on the importance of identifying specific needs of different teams and to work toward finding the right balance of addressing needs with time and resources available. Certainly, teams may be very different based on factors, such as their composition, size, task type, and structure, and therefore may have different needs from a developmental standpoint, as these different factors can influence process and performance ( Bell, 2007 ). Because of this, there is not necessarily a “one size fits all” approach to successful team development; indeed, we do not believe that this framework provides a single answer to successful team performance. We also do notbelieve that it is practical for every single team to be diagnosed at a fine-grained level, as most organizations do not have the resources or time for this. Instead, using scientifically based guides, frameworks and summaries of TDI evidence that is offered here, practitioners should be empowered to move toward a more systematic, scientifically based approach that readily promotes the selection and implementation of TDIs that will best meet specific needs of their teams.
In conducting this review, it became apparent that a lack of clear direction regarding how to best use TDIs makes it easy for organizations to slip into a “more is better” approach. That is, organizations may apply as many TDIs as individuals and teams can take, in hopes that something will end up being helpful to the team. At a basic level, this “shotgun approach’ to team development can address some development of transferrable teamwork skills; yet more often than not, individuals and teams may be getting only a small piece of what is useful for their particular needs while wasting time and resources on irrelevant content.
In response, we hope that integrating disparate TDI literature streams will start a conversation around how these different TDIs can be integrated in a more scientific and systematic way—a topic that is sorely lacking. In particular, we have highlighted here that while individual types of TDIs each have their own scientific evidence regarding their actual or potential benefits for addressing different types of team developmental needs, too many or too few TDIs can be negated—especially if they are offered at the wrong time and/or for the wrong reasons ( Shuffler et al., 2011 ). As presented, this more systematic approach to TDIs highlights the value in critically considering when each type of TDI is likely to have a pronounced impact in shaping team performance trajectories. As a result, the results of our review open an array of research opportunities with this approach. Furthermore, our “effective TDI” heuristic should serve as a starting point for practitioners to venture down a more systematic path for TDIs, offering a straightforward guide that may help in selecting, designing, implementing, and evaluating TDIs. As a result, we look forward to an evolution of TDIs that will result in resource maximization yet optimal levels of team effectiveness, now and in the future.
Acknowledgments
This work was partially supported by funding from the Greenville Health System and grants NNX16AP96G and NNX16AB08G from the National Aeronautics and Space Administration (NASA) to Rice University and grant NNX17AB55G to John Hopkins University in partnership with Rice University; UL1TR000058 from the National Institutes of Health’s National Center for Advancing Translational Science; and National Science Foundation CAREER grant 1654054. The views expressed in this work are those of the authors and do not necessarily reflect the organizations with which they are affiliated or their sponsoring institutions or agencies.
Marissa L. Shuffler ( ude.nosmelc@lffuhsm ) is an assistant professor in the Psychology Department at Clemson University. She received her Ph.D. from the University of Central Florida. Her research utilizes a mixed methods approach to understanding the efficacy of development interventions aimed at improving leadership, teamwork, and multiteam systems in complex environments such as healthcare, spaceflight, and the military.
Deborah DiazGranados ( ude.ucv@sodanargzaid ) is an assistant professor in the school of medicine at Virginia Commonwealth University. She received her Ph.D. from the University of Central Florida. In her research she fo- cuses on team dynamics in the healthcare context, shared leadership in healthcare and in knowledge work teams (i.e., science teams), and the effectiveness of team development interventions.
M. Travis Maynard ( [email protected] . edu) is an associate professor in the management department of the College of Business at Colorado State University. He received his PhD in organizational behavior from the University of Connecticut. In his research he focuses on the role that team contextual variables have on team processes and the development of team psychological states.
Eduardo Salas ( [email protected] ) is the Allyn R. & Gladys M. Cline Chair professor and Chair of the Department of Psychology at Rice University. His research interests are fostering teamwork in organizations and developing evidence-based interventions to improve team functioning.
Contributor Information
MARISSA L. SHUFFLER, Clemson University.
DEBORAH DIAZGRANADOS, Virginia Commonwealth University.
M. TRAVIS MAYNARD, Colorado State University.
EDUARDO SALAS, Rice University.
- Aaron J, McDowell W, & Herdman A 2014. The effects of a team charter on student behavior . Journal of Education for Business , 89 ( 2 ): 90–97. [ Google Scholar ]
- Abrams C, & Berge Z 2010. Workforce cross-training, a reemerging trend in tough times . Journal of Work-place Learning , 22 ( 8 ): 522–529. [ Google Scholar ]
- Adelman L, Christian M, Gualtieri J, & Bresnick TA 1998. Examining the effects of communication training and team composition on the decision making of patriot air defense teams . IEEE Transactions on Systems, Man, and Cybernetics—Part A: Systems and Humans , 28 : 729–741. [ Google Scholar ]
- Adler A, Bliese P, McGurk D, & Hoge C 2009. Battle-mind debriefing and battlemind training as early interventions with soldiers returning from Iraq: Randomization by platoon . Journal of Consulting and Clinical Psychology , 77 ( 5 ): 928–940. [ PubMed ] [ Google Scholar ]
- Aggarwal I, & Woolley A 2013. Do you see what I see? The effect of members’ cognitive styles on team processes and errors in task execution . Organizational Behavior and Human Decision Processes , 122 : 92–99. [ Google Scholar ]
- Ancona DG, & Caldwell DF 1998. Rethinking team composition from the outside in In Neale M, Mannix E & Gruenfeld D (Eds.), Research on managing groups and teams: Composition , vol. 1 : 21–38. Stamford, CT: JAI Press. [ Google Scholar ]
- Anderson JM, Murphy AA,Boyle KB, Yaeger KA, & Halamek LP 2006. Simulating extracorporeal membrane oxygenation emergencies to improve human performance: Part II. Assessment of technical and behavioral skills . Simulation in Healthcare , 1 : 228–232. [ PubMed ] [ Google Scholar ]
- Andreatta P, Saxton E, Thompson M, & Annich G 2011. Simulation-based mock codes significantly correlate with improved pediatric patient cardiopulmonary arrest sur- vival rates . Pediatric Critical Care Medicine , 12 : 33–38. [ PubMed ] [ Google Scholar ]
- Annett J, Cunningham D, & Mathias-Jones P 2000. A method for measuring team skills . Ergonomics , 43 ( 8 ): 1076–1094. [ PubMed ] [ Google Scholar ]
- Anseel F, Lievens F, & Schollaert E 2009. Reflection as a strategy to enhance task performance after feedback . Organizational Behavior and Human Decision Processes , 110 : 23–35. [ Google Scholar ]
- Argyris C 1996. Actionable knowledge: Design causality in the service of consequential theory . Journal of Applied Behavioral Science , 32 ( 4 ): 390–406. [ Google Scholar ]
- Argyris C, & Schon DA 1996. Organizationallearning II: Theory, method, and practice . Reading, MA: Addison-Wesley. [ Google Scholar ]
- Arthur W Jr., Bennett W Jr., Edens PS, & Bell ST 2003. Effectiveness of training in organizations: A meta-analysis of design and evaluation features . Journal of Applied Psychology , 88 : 234–245. [ PubMed ] [ Google Scholar ]
- Arthur W, Edwards BD, Bell ST, Villado AJ, & Bennett W 2005. Team task analysis: Identifying tasks and jobs that are team based . Human Factors: The Journal of the Human Factors and Ergonomics Society , 47 ( 3 ): 654–669. [ PubMed ] [ Google Scholar ]
- Arthur W, Glaze RM, Bhupatkar A, Villado AJ, Bennett W, & Rowe LJ 2012. Team task analysis: Differentiat- ing between tasks using team relatedness and team workflow as metrics of team task interdependence . Human Factors: The Journal of the Human Factors and Ergonomics Society , 54 ( 2 ): 277–295. [ PubMed ] [ Google Scholar ]
- Ashoori M, & Burns C 2013. Team cognitive work analysis: Structure and control tasks . Journal of Cognitive Engineering and Decision Making , 7 ( 2 ): 123–140. [ Google Scholar ]
- Bal PM, De Lange AH, Jansen PG, & Van Der Velde ME 2008. Psychological contract breach and job attitudes: A meta-analysis of age as a moderator . Journal of VocationalBehavior , 72 ( 1 ): 143–158. [ Google Scholar ]
- Barrick MR, Stewart GL, Neubert JM, & Mount MK 1998. Relating member ability and personality to work-team processes and team effectiveness . Journal of Applied Psychology , 83 ( 3 ): 377–391. [ Google Scholar ]
- Beer M 1980. Organization change and development: A systems view . Santa Monica, CA: Goodyear. [ Google Scholar ]
- Beersma B, Hollenbeck JR, Humphrey SE, Moon H, & Conlon DE 2003. Cooperation, competition, and team performance: Toward a contingency approach . Academy of Management Journal , 46 ( 5 ): 572–590. [ Google Scholar ]
- Bell ST 2007. Deep-level composition variables as predictors ofteam performance: A meta-analysis . Journal of Applied Psychology , 92 : 595–615. [ PubMed ] [ Google Scholar ]
- Bethune R, Govindarajulu S, Sahu A, Cawthorn S, & Pullyblank A 2011. Use of briefings and debriefings as a tool in improving team work, efficiency, and communication in the operating theatre . Postgraduate Medicine Journal , 87 : 331–334. [ PubMed ] [ Google Scholar ]
- Blickensderfer E, Cannon-Bowers JA, & Salas E 1998. Cross-training and team performance In Cannon-Bowers JA & Salas E (Eds.), Making decisions under stress: Implications for individuai and team training :299–311. Washington, DC: American Psychological Association. [ Google Scholar ]
- Bowers CA, Baker DP, & Salas E 1994. Measuring the importance of teamwork: The reliability and validity of job/task analysis indices for team-training design . Military Psychology , 6 ( 4 ): 205. [ Google Scholar ]
- Brannick MT, Salas E, & Prince CW (Eds.). 1997. Team performance assessment and measurement: Theory, methods, and applications . Mahwah, NJ: Psychology Press. [ Google Scholar ]
- Bruner M, & Spink K 2011. Team building andperceived effort in an exercise setting: Gender effects . Journal of Science and Medicine in Sport , 14 ( 2 ): 159–161. [ PubMed ] [ Google Scholar ]
- Buller PF, & Bell CH Jr. 1986. Effects of team building and goal setting on productivity: A field experiment . Academy of Management Journal , 29 : 305–328. [ Google Scholar ]
- Bunderson JS, & Sutcliffe KA 2002. Comparing alternate conceptualizations of functional diversity in management teams: Process and performance . Acad- emy of Management Journal , 45 : 875–893. [ Google Scholar ]
- Burke CS, Stagl KC, Klein C, Goodwin GF, Salas E, & Halpin SM 2006. What type of leadership behav- iors are functional in teams? A meta-analysis . The Leadership Quarterly , 17 ( 3 ): 288–307. [ Google Scholar ]
- Byrd JT, & Luthy MR 2010. Improving group dynamics: Creating a team charter . Academy of Educational Leadership Journal , 14 ( 1 ): 1–17. [ Google Scholar ]
- Cannon-Bowers JA, & Bowers C 2010. Team development and functioning In Zedeck S (Ed.), APA handbook of industrial and organizational psychology , vol. 1 :597–650. Washington, DC: American Psychological Association. [ Google Scholar ]
- Cannon-Bowers JA, & Salas E 1997. A framework for developing team performance measures in training In Brannick MT, Salas E, & Prince CW (Eds.), Team performance assessment and measurement: The- ory, methods, and applications , 45–62. Mahwah, NJ: Lawrence Erlbaum. [ Google Scholar ]
- Cannon-Bowers JA, Tannenbaum SI, Salas E, & Volpe CE 1995. Defining competencies and estab- lishing team training requirements . Team Effectiveness and Decision Making in Organizations , 333 : 380. [ Google Scholar ]
- Carr C, & Peters J 2013. The experience of team coaching: A dual case study . International Coaching Psychology Review , 8 ( 1 ): 80–98. [ Google Scholar ]
- Carson JB, Tesluk PE, & Marrone JA 2007. Shared leadership in teams: An investigation of antecedent conditions and performance . Academy of management Journal , 50 ( 5 ): 1217–1234. [ Google Scholar ]
- Chen G, Mathieu JE, & Bliese PD 2004. Aframeworkfor conducting multilevel construct validation In Yammarino FJ & Dansereau F (Eds.), Research in multilevel issues: Multilevel issues in organizational behavior and processes , vol. 3 : 273–303. Oxford, UK: Elsevier. [ Google Scholar ]
- Choi H-S, & Thompson L 2005. Old wine in a new bottle: Impact of membership change on group creativity . Organizational Behavior and Human Decision Processes , 98 : 121–132. [ Google Scholar ]
- Chung SP, Cho J, Park YS, Kang HG, Kim CW, Song KJ, Lim H, & Cho GC 2010. Effects of script- based role play in cardiopulmonary resuscitation team training . Emergency Medicine Journal , 28 : 690–694. [ PubMed ] [ Google Scholar ]
- Clutterbuck D 2007. An international perspective on mentoring In Ragins BR & Kram KE (Eds.) The handbook of mentoring at work: Theory, research, and practice , 633–656. Thousand Oaks, CA: Sage. [ Google Scholar ]
- Cohen SG, & Bailey DE 1997. What makes teams work: Group effectiveness research from the shop floor to the executive suite . Journalof Management , 23 ( 3 ): 239–290. [ Google Scholar ]
- Colarelli SM, &Boos AL 1992. Sociometric andability- based assignment to work groups: Some implications for personnel selection . Journal of Organizational Behavior , 13 ( 2 ): 187–196. [ Google Scholar ]
- Collins CG, & Parker SK 2010. Team capability beliefs over time: Distinguishing between team potency, team outcome efficacy, and team process efficacy . Journal of Occupational and Organizational Psychology , 83 ( 4 ): 1003–1023. [ Google Scholar ]
- Conger JA, & Pearce CL 2003. Shared leadership: Reframing the hows and whys of leadership . Thousand Oaks, CA: Sage Publications. [ Google Scholar ]
- Connaughton SL, & Shuffler M 2007. Multinational multicultural distributed teams: A review and future agenda . Small Group Research , 38 : 387–412. [ Google Scholar ]
- Contractor NS, DeChurch LA, Carson J, Carter DR, & Keegan B 2012. The topology of collective leadership . The Leadership Quarterly , 23 ( 6 ): 994–1011. [ Google Scholar ]
- Cooke NJ, Gorman JC, & Rowe LJ 2008. An ecological perspective on team cognition In Salas E, Goodwin GF & Burke CS (Eds.), Team effectiveness in complex organizations: Cross-disciplinary perspectives and approaches , 157–182. New York: Routledge/Taylor & Francis Group. [ Google Scholar ]
- Cooke NJ, Kiekel PA, Salas E, Stout R, Bowers C, & Cannon-Bowers J 2003. Measuring team knowledge: A window to the cognitive underpinnings of team performance . Group Dynamics: Theory, Research, and Practice , 7 : 179–199. [ Google Scholar ]
- Cox PL, College C, & Bobrowski PE 2000. The team charter assignment: Improving effectiveness of class-room teams . Journal of Behavioral and Applied Management , 1 : 92–103. [ Google Scholar ]
- Crawford ER, & Lepine JA 2013. A configural theory of team processes: Accounting for the structure of taskwork and teamwork . Academy of Management Review , 38 ( 1 ): 32–48. [ Google Scholar ]
- Cronin MA, Weingart LR, & Todorova G 2011. Dynamics in groups: Are we there yet? Academy of Management Annals , 5 ( 1 ): 571–612. [ Google Scholar ]
- Cummings JN, & Haas MR 2012. So many teams, so little time: Time allocation matters in geographically dispersed teams . Journal of Organizational Behavior , 33 ( 3 ): 316–341. [ Google Scholar ]
- D’Innocenzo L, Mathieu JE, & Kukenberger MR 2016. A meta-analysis of different forms of shared leadership-team performance relations . Journal of Management , 42 ( 7 ): 1964–1991. [ Google Scholar ]
- Darling MJ, & Parry CS 2001. After-action reviews: Linking reflection and planning in a learning practice . Reflections: The SoL Journal , 3 ( 2 ): 64–72. [ Google Scholar ]
- Day DV, Gronn P, & Salas E 2004. Leadership capacity in teams . The Leadership Quarterly , 15 : 857–880. [ Google Scholar ]
- Dekker SWA 2002. The field guid to human error investigations . London, UK: Ashgate. [ Google Scholar ]
- DeMeuse KP, & Liebowitz SJ 1981. An empirical analysis of team-building research . Group & Organization Studies , 6 ( 3 ): 357–378. [ Google Scholar ]
- DeRue DS, Hollenbeck JR, Johnson MD, Ilgen DR, & Jundt DK 2008. How different team downsizing approaches influence team-level adaptation and performance . Academy of Management Journal , 51 ( 1 ): 182–196. [ Google Scholar ]
- Devine DJ 1999. Effects of cognitive ability, task knowledge, information sharing, and conflict on group decision-making effectiveness . Small Group Research , 30 ( 5 ): 608–634. [ Google Scholar ]
- De Vos A, Buyens D, & Schalk R 2003. Psychological contract development during organizational sociali- zation: Adaptation to reality and the role of reciprocity . Journal of organizational behavior , 24 ( 5 ): 537–559. [ Google Scholar ]
- Dine CJ, Gersh RE, Leary M, Riegel BJ, Bellini LM, & Abella BS 2008. Improving cardiopulmo- nary resuscitation quality and resuscitation training by combining audiovisual feedback and debriefing . Critical Care Medicine , 36 ( 10 ): 2817–2822. [ PubMed ] [ Google Scholar ]
- Dow AW, DiazGranados D, Mazmanian PE, & Retchin SM 2013. Applying organizational science to health care: A framework for collaborative practice . Academic Medicine , 88 ( 7 ): 952. [ PMC free article ] [ PubMed ] [ Google Scholar ]
- Drury CG 1990. Methods for direct observation of performance In Wilson JR & Corlett NJ (Eds.), Evaluation of human work . London, UK: Taylor and Francis. [ Google Scholar ]
- Duncan PC, Rouse WB, Johnston JH, Cannon-Bowers JA, Salas E, & Burns JJ 1996. Training teams working in complex systems: A mental model-based approach In Rouse WB (Ed.), Human/ technology interaction in complex systems , vol. 8 : 173–231. Greenwich, CT: JAI Press. [ Google Scholar ]
- Dyer WG 1977. Team building: Issues and alternatives . Reading, MA: Addison-Wesley. [ Google Scholar ]
- Dyer WG 2007. Team building: Proven strategies for improving team performance . San Francisco, CA: John Wiley & Sons. [ Google Scholar ]
- Earley CP, & Mosakowski E 2000. Creating hybrid team cultures: An empirical test of transnational team func- tioning . Academy ofManagement Journal , 43 ( 1 ): 26–49. [ Google Scholar ]
- Eby LT, & Dobbins GH 1997. Collectivistic orientation in teams: An individual and group-level analysis . Journal of Organizational Behavior , 18 : 275–295. [ Google Scholar ]
- Eddy E,Tannenbaum S, & Mathieu J 2013. Helping teams to help themselves: Comparing two team-led debriefing methods . Personnel Psychology , 66 ( 4 ): 975–1008. [ Google Scholar ]
- Edelson DP, Litzinger B, Aroroa V, Walsh D, Kim S, Lauderdale DS, VandenHoeck TL, Becker LB, & Abella BS 2008. Improving in-hospital cardiac arrest process and outcomes with performance debriefing . Archive of Internal Medicine , 168 :1063–1069. [ PubMed ] [ Google Scholar ]
- Eden D 1986. Team development: Quasi-experimental confirmation among combat companies . Group and Organization Studies , 11 :133–146. [ Google Scholar ]
- Edmondson A 1999. Psychological safety and learning behavior in work teams . Administrative Science Quarterly , 44 ( 2 ): 350–383. [ Google Scholar ]
- Ellis APJ, Bell BS, Ployhart RE, Hollenbeck JR, & Ilgen DR 2005. An evaluation of generic teamwork skills training with action teams: Effects on cognitive and skill-based outcomes . Personnel Psychology , 58 : 641–672. [ Google Scholar ]
- Ellis S, & Davidi I 2005. After-event reviews: Drawing lessons from successful and failed experience . Journal of Applied Psychology , 90 : 857–871. [ PubMed ] [ Google Scholar ]
- Entin EB, Entin EE, MacMillan J, & Serfaty D 1993. Structuring and training high-reliability teams (AD No. ADA302385) . Burlington, MA: Alphatech. [ Google Scholar ]
- Feldman DC 1984. The development and enforcement of group norms . Academy of Management Review , 9 ( 1 ): 47–53. [ Google Scholar ]
- Feyerherm AE, & Rice CL 2002. Emotional intelligence and team performance: The good, the bad and the ugly . International Journal of Organizational Analysis , 10 ( 4 ): 343–362. [ Google Scholar ]
- Fisher DM, Bell ST, Dierdorff EC, & Belohlav JA 2012. Facet personality and surface-level diversity as team mental model antecedents: implications for im- plicit coordination . Journal of Applied Psychology , 97 ( 4 ): 825–841. [ PubMed ] [ Google Scholar ]
- Fowlkes JE, Lane NE, Salas E, Franz T, & Oser R 1994. Improving the measurement of team performance: The TARGETs methodology . Military Psychology , 6 ( 1 ): 47. [ Google Scholar ]
- Friedlander F 1967. The impact of organizational training laboratories upon effectiveness of ongoing work groups . Personnel Psychology , 20 : 289–307. [ Google Scholar ]
- Geis GL, Pio B, Pendergrass TL, Moyer MR, & Patterson MD 2011. Simulation to assess the safety of new healthcare teams and new facilities . Simulation in Healthcare , 6 :125–133. [ PubMed ] [ Google Scholar ]
- Gersick CJG 1988. Time and transition in work teams: Toward a new model of group development . Academy of Management Journal , 31 ( 1 ): 9–41. [ Google Scholar ]
- Gibson CB, & Saxton T 2005. Thinking outside theblack box: Outcomes of team decisions with third-party intervention . Small Group Research , 36 ( 2 ): 208–236. [ Google Scholar ]
- Gully SM, Incalcaterra KA, Joshi A, & Beaubien JM 2002. A meta-analysis of team-efficacy, potency, and performance: Interdependence andlevel of analysis as moderatore of observed relationships . Journal of Applied Psychology , 87 ( 5 ): 819. [ PubMed ] [ Google Scholar ]
- Hackman JR 1987. The design of work teams In Lorsch J (Ed.), Handbook of organizational behavior . Englewood Cliffs, NJ: Prentice-Hall. [ Google Scholar ]
- Hackman JR 2011. Collaborative intelligence: Using teams to solve hard problems . San Francisco, CA: Berrett-Koehler. [ Google Scholar ]
- Hackman JR, & Morris CG 1975. Group tasks, group interaction process, and group performance effectiveness: A review and proposed integration In Berkowitz L (Ed.) Advances in experimental social psychology , vol. 8 :45–99. New York: Academic Press. [ Google Scholar ]
- Hackman JR, & O’Connor M 2005. What makes for a great analytic team? Individual vs. team approaches to intelligence analysis . Washington, DC: Intelligence Science Board, Office of the Director of Central Intelligence. [ Google Scholar ]
- Hackman JR, & Oldham GR 1976. Motivation through the design of work: Test of a theory . Organizational behavior and human performance , 16 ( 2 ): 250–279. [ Google Scholar ]
- Hackman JR, & Wageman R 2005. A theory of team coaching . Academyof Management Review , 30 : 269–287. [ Google Scholar ]
- Hagen M 2010. The wisdom of the coach: A review of managerial coaching in the Six Sigma context . Total Quality Management and Business Excellence , 21 ( 8 ): 791–798. [ Google Scholar ]
- Harris K, Treanor C, & Salisbury M 2006. Improving patient safety with team coordination: Challenges and strategies of implementation . JOGNN , 35 ( 4 ): 557–566. [ PubMed ] [ Google Scholar ]
- Hawkins P 2011. Leadership team coaching: Developing collective transformational leadership . Philadelphia, PA: Kogan Page Publishers. [ Google Scholar ]
- Hollenbeck JR, & Spitzmuller M 2012. Team structure: Tight versus loose coupling in task-oriented groups In Kozlowski SWJ (Ed.) The Oxford handbook of organizational psychology , vol. 2 :733–766. New York: Oxford United Press. [ Google Scholar ]
- Hollenbeck JR, DeRue D, & Guzzo R 2004. Bridgingthe gap between I/O research and HR practice: Improving team composition, team training, and team task design . Human Resource Management , 43 ( 4 ): 353–366. [ Google Scholar ]
- Huang WW, Wei KK, Watson RT, & Tan BCY 2002. Supporting virtual team building with a GSS: An empirical investigation . Decision Support Systems , 34 ( 4 ): 359–367. [ Google Scholar ]
- Hughes AM, Gregory ME, Joseph DL, Sonesh SC, Marlow SL, Lacerenza CN, & Salas E 2016. Saving lives: A meta-analysis of team training in healthcare . Journal of Applied Psychology , 101 ( 9 ): 1266–1304. [ PubMed ] [ Google Scholar ]
- Hughes RL, Rosenbach WE, & Clover WH 1983. Team development in an intact, ongoing work group: A quasi-field experiment . Group and Organization Studies , 8 : 161–186. [ Google Scholar ]
- Humphrey SE, & Aime F 2014. Team microdynamics: Toward an organizing approach to teamwork . Academy of Management Annals , 8 ( 1 ): 443–503. [ Google Scholar ]
- Humphrey SE, Hollenbeck JR, Meyer CJ, & Ilgen DR 2011. Personality configurations in self-managed teams: A natural experiment on the effects of maxi- mizing and minimizing variance in traits . Journal of Applied Social Psychology , 41 ( 7 ): 1701–1732. [ Google Scholar ]
- Humphrey SE, Morgeson FP, & Mannor MJ 2009. Developing a theory of the strategic core of teams: A role composition model ofteam performance . Journal of Applied Psychology , 94 ( 1 ): 48–61. [ PubMed ] [ Google Scholar ]
- Hunsaker P, Pavett C, & Hunsaker J 2011. Increasing student-learning team effectiveness with team charters . Journal of Education for Business , 86 ( 3 ): 127–139. [ Google Scholar ]
- Ilgen JS, Ma IW, Hatala R, & Cook DA 2015. A systematic review of validity evidence for checklists versus global rating scales in simulation-based assessment . Medical Education , 49 ( 2 ): 161–173. [ PubMed ] [ Google Scholar ]
- Ikomi PA, Boehm-Davis DA, Holt RW, & Incalcaterra KA 1999. Jump seat observations of advance crew resource management (ACRM) effectiveness . In Jensen RS, Cox B, Callister JD & Lavis R (Eds.), Proceedings of the 10th International Symposium on Aviation Psychology: 292–297. Columbus, OH: Ohio State University. [ Google Scholar ]
- Jackson SE, Joshi A, & Erhardt NL 2003. Recent research on team and organizational diversity: SWOT analysis and implications . Journal of Management , 29 : 801–830. [ Google Scholar ]
- Janssens M, Sels L, & Van den Brande I 2003. Multiple types of psychological contracts: A six-cluster solution . Human Relations , 56 ( 11 ): 1349–1378. [ Google Scholar ]
- Jarvenpaa SL, Knoll K, & Leidner DE 1998. Is anybody out there? Antecedents of trust in global virtual teams . Journal of Management Information Systems , 14 ( 4 ): 29–64. [ Google Scholar ]
- Johns G 2006. The essential impact of context on organizationalbehavior . Academyof Management Review , 31 ( 2 ): 386–408. [ Google Scholar ]
- Jordan PJ, & Troth AC 2004. Managing emotions during team problem solving: Emotional intelligence and conflict resolution . Human Performance , 17 ( 2 ): 195–218. [ Google Scholar ]
- Kanawattanachai P, & Yoo Y 2007. The impact of knowledge coordination on virtual team performance over time . MIS Quarterly , 31 ( 4 ): 783–808. [ Google Scholar ]
- Kichuk SL, & Wiesner WH 1997. The big five personality factos and team performance: Implications for selecting successful product design teams . Journal of Engineering and Technology Management , 14 ( 3 ): 195–221. [ Google Scholar ]
- Kiggundu MN 1983. Task interdependence and job design: Test of a theory . Organizational Behavior and Human Performance , 31 : 145–172. [ PubMed ] [ Google Scholar ]
- Kilduff M, Angelmar R, & Mehra A 2000. Top management-team diversity and firm performance: Examining the role of cognitions . Organization Science , 11 : 21–34. [ Google Scholar ]
- Kimberley JR, & Nielsen WR 1975. Organization development and change in organizational performance . Administrative Science Quarterly , 20 : 191–206. [ Google Scholar ]
- King P, & Eaton J 1999. Coaching for results . Industrial and Commercial Training , 31 ( 4 ): 145–148. [ Google Scholar ]
- Kirkman BL, & Mathieu JE 2005. The dimensions and antecedents of team virtuality . Journal of Management , 31 ( 5 ): 700–718. [ Google Scholar ]
- Kirkman BL, & Rosen B 1999. Beyond self-management: Antecedents and consequences of team empowerment . Academy of Management Journal , 42 ( 1 ): 58–74. [ Google Scholar ]
- Kirkman BL, & Shapiro DL 2001. The impact of cultural values on job satisfaction and organizational commitment in self-managing work teams: The me- diating role of employee resistance . Academy of Management Journal , 44 ( 3 ): 557–569. [ Google Scholar ]
- Kirkman BL, Tesluk PE, & Rosen B 2001. Alternative methods of assessing team-level variables: Comparing the predictive power of aggregation and consensus methods . Personnel Psychology , 54 : 645–667. [ Google Scholar ]
- Klein C, DiazGranados D, Salas E, Le H, Burke CS, Lyons R, & Goodwin GF 2009. Does team building work? Small Group Research , 40 :181–222. [ Google Scholar ]
- Klein KJ, Ziegert JC, Knight AP, & Xiao Y 2006. Dynamic delegation: Shared, hierarchical, and dein- dividualized leadership in extreme action teams . Administrative Science Quarterly , 51 : 590–621. [ Google Scholar ]
- Kluger AN, & DeNisi A 1996. The effects of feedback interventions on performance: A historical review, a meta-analysis, and a preliminary feedback intervention theory . Psychological Bulletin , 119 ( 2 ): 254–284. [ Google Scholar ]
- Kozlowski SWJ, Gully SM, McHugh PP, Salas E, & Cannon-Bowers JA 1996. A dynamic theory of leadership and team effectiveness: Developmental and task contingent leader roles . Research in Personnel and Human Resources Management , 14 : 253–305. [ Google Scholar ]
- Kozlowski SWJ, & Ilgen DR 2006. Enhancing the effectiveness of work groups and teams . Psychological Science in the Public Interest , 7 ( 3 ): 77–124. [ PubMed ] [ Google Scholar ]
- Kozlowski SWJ, Watola DJ, Jensen JM, Kim BH, & Botero IC 2009. Developing adaptive teams: A theory of dynamic team leadership In Salas E, Goodwin GF & Burke CS (Eds.), Team effectiveness in complex organizations: Cross-disciplinary perspectives and approaches : 113–156. Mahwah, NJ: LEA. [ Google Scholar ]
- Lacerenza CN, Marlow SL, Tannenbaum SI, & Salas E 2018. Team development interventions: Evidence-based approaches for improving teamwork . American Psychobgist , 73 ( 4 ): 517–531. [ PubMed ] [ Google Scholar ]
- Lantz A, & Brav A 2007. Job design for learning in work groups . Journal of Workplace Learning , 19 ( 5 ): 269–285. [ Google Scholar ]
- Lassiter DL, Vaughn JS, Smaltz VE, Morgan BB Jr., & Salas E 1990. A comparison of two types of training interventions on team communication performance . In Proceedings of the Human Factors Society 34th Annual Meeting: 1372–1376. Santa Monica, CA: Human Factors and Ergonomics Society. [ Google Scholar ]
- Le Blanc PM, Hox JJ, Schaufeli WB, Taris TW, & Peeters MCW 2007. Take care! The evaluation of a team-based burnout intervention program for oncology care providers . Journal of Applied Psychology , 92 : 213–227. [ PubMed ] [ Google Scholar ]
- Leedom DK, & Simon R 1995. Improving team coordination: A case for behavior based training . Military Psychology , 7 ( 2 ): 109–122. [ Google Scholar ]
- LePine JA 2003. Team adaptation and post-change performance: Effects of team composition in terms of members’ cognitive ability and personality . Journal of Applied Psychology , 88 : 27–39. [ PubMed ] [ Google Scholar ]
- LePine JA, Piccolo RF, Jackson CL, Mathieu JE, & Saul JR 2008. A meta-analysis of teamwork processes: Tests of a multidimensional model and re- lationships with team effectiveness criteria . Personnel Psychology , 61 ( 2 ): 273–307. [ Google Scholar ]
- Levine JM, & Moreland RL 1990. Progress in small group research . AnnualReview of Psychology , 41 ( 1 ): 585–634. [ Google Scholar ]
- Lewis K 2004. Knowledge and performance in knowledge-worker teams: A longitudinal study of transactive memory systems . Management Science , 50 ( 11 ): 1519–1533. [ Google Scholar ]
- Locke EA, & Latham GP 1990. A theory of goalsetting & taskperformance . Englewood Cliffs, NJ: Prentice-Hall. [ Google Scholar ]
- Locke EA, & Latham GP 2002. Building a practically useful theory of goal setting and task motivation . American Psychologist , 57 : 705–717. [ PubMed ] [ Google Scholar ]
- Lynn GS, & Reilly RR 2000. Measuring team performance . Research-Technology Management , 43 ( 2 ): 48–56. [ Google Scholar ]
- Mann RD 1959. A review of the relationships between personality and performance in small groups . PsychologicalBulletin , 56 : 242–270. [ Google Scholar ]
- Marks MA, Mathieu JE, & Zaccaro SJ 2001. A temporally based framework and taxonomy of team processes . Academy of Management Review , 26 ( 3 ): 356–376. [ Google Scholar ]
- Marks MA, Sabella MJ, Burke SC, & Zaccaro SJ 2002. The impact of cross-training on team effectiveness . Journal of Applied Psychology , 87 ( 1 ): 3–13. [ PubMed ] [ Google Scholar ]
- Marks MA, Zaccaro SJ, & Mathieu JE 2000. Performance implications of leader briefings and team-interaction training for team adaptation to novel environments . Journal of Applied Psychology , 85 : 971–986. [ PubMed ] [ Google Scholar ]
- Marsh HW, Ludtke O, Trautwein U, & Morin AJ 2009. Classical latent profile analysis of academic self-concept dimensions: Synergy of person-and variable-centered approaches to theoretical models of self-concept . Structural Equation Modeling , 16 ( 2 ): 191–225. [ Google Scholar ]
- Mathieu JE, Maynard MT, Rapp TL, & Gilson L 2008. Team effectiveness 1997–2007: A review of recent advancements and a glimpse into the future . Journal of Management , 34 ( 3 ): 410–476. [ Google Scholar ]
- Mathieu JE, &Rapp TL 2009. Laying the foundationfor successful team performance trajectories: The roles of team charters and performance strategies . Journal of Applied Psychology , 94 : 90–103. [ PubMed ] [ Google Scholar ]
- Mathieu JE, Tannenbaum SI, Donsbach JS, & Alliger GM 2014. A review and integration of team composition models: Moving toward a dynamic and temporal framework . Journal of Management , 40 ( 1 ): 130–160. [ Google Scholar ]
- Maynard MT, Gilson LL, & Mathieu JE 2012. Empowerment—fad or fab? A multilevel review of the past two decades of research . Journal of Management , 38 ( 4 ): 1231–1281. [ Google Scholar ]
- Maynard MT, Kennedy DM, & Sommer SA 2015. Team adaptability: A synthesis and framework for how this literature needs to “adapt” going forward . European Journal of Work & Organizational Psychology , 24 : 652–677. [ Google Scholar ]
- McGrath JE 1964. Social psychology: A brief introduction . New York: Holt, Rinehart and Winston. [ Google Scholar ]
- McIntyre RM, & Dickinson TL 1997. A conceptual framework for teamwork measurement In Brannick MT, Salas E, & Prince C (Eds.) Team performance assessment and measurement , 31–56. Mahwah, NJ: Lawrence Erlbaum Associates Publishers. [ Google Scholar ]
- Medsker GJ, & Campion MA 1997. Job and team design In Salvendy G (Ed.) Handbook of industrial engineering: technology and operations management , 3rd ed., 868–898. Danvers, MA: John Wiley-Interscience. [ Google Scholar ]
- Mohammed S, & Angell LC 2003. Personality hetero- geneity in teams: Which differences make a difference for team performance? Small Group Research , 34 ( 6 ): 651–677. [ Google Scholar ]
- Morgan L, Hadi M, Pickering S, Robertson E, Griffin D, Collins G, & New S 2015. The effect of teamwork training on team performance and clinical outcome in elective orthopaedic surgery: A controlled interrupted time series study . BMJ Open , 5 ( 4 ): e006216. [ PMC free article ] [ PubMed ] [ Google Scholar ]
- Morgeson FP, DeRue DS, & Karam EP 2010. Leadership in teams: A functional approach to understanding leadership structures and processes . Journal of Management , 36 ( 1 ): 5–39. [ Google Scholar ]
- Morgeson FP, & Humphrey SE 2008. Job and team design: Toward a more integrative conceptualization of work design In Martocchio JJ (Ed.) Research in personnel and human resources management , 39–91. Bingley, UK: Emerald Group Publishing Limited. [ Google Scholar ]
- Morrison P, & Sturges J 1980. Evaluation of organization development in a large state government organization . Group and Organization Studies , 5 : 48–64. [ Google Scholar ]
- Munro A, & Clark RE 2013. Cognitive task analysis-based design and authoring software for simulation training . Military Medicine , 178 : 7–14. [ PubMed ] [ Google Scholar ]
- Muthen B, & Muthen LK 2000. Integrating person- centered and variable-centered analyses: Growth mixture modeling with latent trajectory classes . Al- coholism: Clinical and Experimental Research , 24 ( 6 ): 882–891. [ PubMed ] [ Google Scholar ]
- Naylor JC, & Briggs GE 1965. Team-training effectiveness under various conditions . Journal ofApplied Psychology , 49 : 223–229. [ PubMed ] [ Google Scholar ]
- Neuman SB, & Cunningham L 2009. The impact of professional development and coaching on early language and literacy instructional practices . American Educational Research Journal , 46 ( 2 ): 532–566. [ Google Scholar ]
- Nicolaides VC, LaPort KA, Chen TR, Tomassetti AJ, Weis EJ, Zaccaro SJ, & Cortina JM 2014. The shared leadership of teams: A meta-analysis of proximal, distal, and moderating relationships . Leadership Quarterly , 25 ( 5 ): 923–942. [ Google Scholar ]
- Norton WI, & Sussman L 2009. Team charters: Theoretical foundations and practical implications for quality and performance . The Quality Management Journal , 16 ( 1 ): 7–17. [ Google Scholar ]
- Nouri R, Erez M, Rockstuhl T, Ang S, Leshem-Calif L, & Rafaeli A 2013. Taking the bite out of culture: The impact of task structure and task type on overcoming impediments to cross-cultural team performance . Journal of OrganizationalBehavior , 34 : 739–763. [ Google Scholar ]
- Oden KB 2009. Distributed team training: Effective team feedback . Dissertation Abstracts International: Section B: The Sciences and Engineering , 70 ( 1-B ): 721. [ Google Scholar ]
- Offermann LR, Bailey JR, Vasilopoulos NL, Seal C, & Sass M 2004. The relative contribution of emotional competence and cognitive ability to individual and team performance . Human Performance , 17 ( 2 ): 219–243. [ Google Scholar ]
- Park G, Spitzmuller M, &DeShon RP 2013. Advancing our understanding of team motivation: Integrating conceptual approaches and content areas . Journal of Management , 39 ( 5 ): 1339–1379. [ Google Scholar ]
- Parker SK 2014. Beyond motivation: Job and work design for development, health, ambidexterity, and more . Annual Review of Psychology , 65 : 661–691. [ PubMed ] [ Google Scholar ]
- Parker SK, Morgeson FP, & Johns G 2017. One hundred years of work design research: Looking back and looking forward . Journal of Applied Psychology , 102 ( 3 ): 403. [ PubMed ] [ Google Scholar ]
- Parker SK, & Wall TD 1998. Job and work design: Organizing work to promote well-being and effectiveness , vol. 4 Thousand Oaks, CA: SAGE Publications. [ Google Scholar ]
- Payne V 2001. The team-building workshop: a trainer’s guide . Chicago, IL: Amacom Books. [ Google Scholar ]
- Pentland A 2012. The new science of building great teams . Harvard Business Review , 90 ( 4 ): 60–69. [ Google Scholar ]
- Peters J, & Carr C 2013. Team effectiveness and team coaching literature review . Coaching: An International Journal of Theory, Research and Practice , 6 ( 2 ): 116–136. [ Google Scholar ]
- Pisano GP, & Verganti R 2008. Which kind of collaboration is right for you . Harvard Business Review , 86 ( 12 ): 78–86. [ Google Scholar ]
- Prichard JS, & Ashleigh MJ 2007. The effects of team- skills training on transactive memory and performance . Small Group Research , 38 : 696–726. [ Google Scholar ]
- Qudrat-Ullah H 2007. Debriefing can reduce mis-perceptions offeedback: The case ofrenewable resource management . Simulation & Gaming , 38 ( 3 ): 382–97. [ Google Scholar ]
- Ramdass D, &Zimmerman B 2008. Effects of self-correction strategy training on middle school students’ self-efficacy, self-evaluation, and mathematics division learning . Journal of Advanced Academics , 20 ( 2 ): 18–41. [ Google Scholar ]
- Rapp TL, & Mathieu JE 2007. Evaluating an in- dividually self-administered generic teamwork skills training program across time and levels . Small Group Research , 38 : 532–555. [ Google Scholar ]
- Redshaw B 2000. Do we really understand coaching? How can we make it work better? Industrial and Commercial Training , 32 ( 3 ): 106–108. [ Google Scholar ]
- Reich Y, Ullmann G, Van der Loos M, & Leifer L 2009. Coaching product development teams: A conceptual foundation for empirical studies . Research in Engineering Design , 19 ( 4 ): 205–222. [ Google Scholar ]
- Reid N, Oxley H, Dowdall F, & Brennan AL 2015. Learning from patient deaths in CF: An audit of team debrief sessions at a UK adult CF center . Journal of Cystic Fibrosis , 14 ( 1 ): 19–20. [ Google Scholar ]
- Resick CJ, Dickson MW, Mitchelson JK, Allison LK, & Clark MA 2010. Team composition, cognition, and effectiveness: Examining mental model similarity and accuracy . Group Dynamics: Theory, Research, and Practice , 14 ( 2 ): 174. [ Google Scholar ]
- Rosen MA, Salas E, Wilson KA, King HB, Salisbury M, Augenstein JS, & Birnbach DJ 2008. Measuring team performance in simulation-based training: adopting best practices for healthcare . Simulation in Healthcare , 3 ( 1 ): 33–41. [ PubMed ] [ Google Scholar ]
- Roth EM 2008. Uncovering the requirements of cognitive work . Human Factors: The Journal of the Human Factors andErgonomics Society , 50 ( 3 ): 475–480. [ PubMed ] [ Google Scholar ]
- Roth EM, & Patterson ES 2005. Using observational study as a tool for discovery: Uncovering cognitive and collaborative demands and adaptive strategies In Montgomery H, Lipshitz R & Brehmer B (Eds.), How professionals make decisions . Mahwah, NJ, Erlbaum: 379–393. [ Google Scholar ]
- Rousseau V, Aube C, & Tremblay S 2011. Team coaching and innovation in work teams: An examination of the motivational and behavioral intervening mechanisms . Leadership & Organization Development Journal , 34 ( 4 ): 344–364. [ Google Scholar ]
- Rousseau V, Aubé C, & Tremblay S 2013. Team coaching and innovation in work teams: An examination of the motivational and behavioral intervening mechanisms . Leadership & Organization Development Journal , 34 ( 4 ): 344–364. [ Google Scholar ]
- Salas E, Bowers CA, & Cannon-Bowers JA 1995. Military team research: 10 years of progress . Military Psychology , 7 ( 2 ): 55–75. [ Google Scholar ]
- Salas E, Burke CS, Bowers CA, & Wilson KA 2001. Team training in the skies: Does crew resource management (CRM) training work? Human Factors , 43 :671–674. [ PubMed ] [ Google Scholar ]
- Salas E, & Cannon-Bowers J 1998. Team performance and training in complex environments: Recent findings from applied research . Current Directions in Psychological Science , 7 ( 3 ): 83–87. [ Google Scholar ]
- Salas E, & Cannon-Bowers JA 2001. The science of training: A decade of progress . Annual Reviews of Psychology , 52 ( 4 ): 471–499. [ PubMed ] [ Google Scholar ]
- Salas E, Cooke NJ, & Rosen MA 2008a. On teams, teamwork, and team performance: Discoveries and developments . Human Factors , 50 ( 3 ): 540–547. [ PubMed ] [ Google Scholar ]
- Salas E, DiazGranados D, Klein C, Burke CS, Stagl KC, Goodwin GF, & Halpin SM 2008b. Does team training improve team performance? A meta- analysis . Human Factors , 50 : 903–933. [ PubMed ] [ Google Scholar ]
- Salas E, Dickinson TL, Converse SA, & Tannenbaum SI 1992. Toward an understanding of team performance and training In Swezey RW & Salas E (Eds.), Teams: Their training and performance , 3–29. Westport, CT: Ablex Publishing. [ Google Scholar ]
- Salas E, Priest HA, & DeRouin RE 2005. Team building In Stanton N, Hendrick H, Konz S, Parsons K & Salas E (Eds.), Handbook of human factors and ergonomicsmethods : 48–1–48–5. London, UK: Taylor & Francis. [ Google Scholar ]
- Salas E, Rozell D, Mullen B, & Driskell JE 1999. The effect on team building on performance: An integration . Small Group Research , 30 : 309–329. [ Google Scholar ]
- Salas E, Stagl KC, Burke CS, & Goodwin GF 2007. Fostering team effectiveness in organizations: Toward an integrative theoretical framework In Stuart B, Spaulding W & Poland J (Eds.) Nebraska symposium on motivation , vol. 52 :185–243. Lincoln, NE: University of Nebraska Press. [ PubMed ] [ Google Scholar ]
- Salas E, Tannenbaum SI, Kozlowski SW, Miller CA, Mathieu JE, & Vessey WB 2015. Teams in space exploration a new frontier for the science of team effectiveness . Current Directions in Psychological Science , 24 ( 3 ): 200–207. [ Google Scholar ]
- Sanchez JI, & Fraser SL 1992. On the choice of scales for task analysis . Journal of Applied Psychology , 77 ( 4 ): 545–553. [ Google Scholar ]
- Sargent LD, Allen BC, Frahm JA, & Morris G 2009. Enhancing the experience of student teams in large classes: Training teaching assistants to be coaches . Journal of Management Education , 33 ( 5 ): 526–552. [ Google Scholar ]
- Schalk R, & Roe RE 2007. Towards a dynamic model of the psychological contract . Journal for the Theory of SocialBehaviour , 37 ( 2 ): 167–182. [ Google Scholar ]
- Scheuermann BK, Duchaine EL, Bruntmyer DT, Wang EW, Nelson CM, & Lopez A 2013. An exploratory survey of the perceived value of coaching activities to support PBIS implementation in secure juvenile education settings . Education and Treatment of Children , 36 ( 3 ): 147–160. [ Google Scholar ]
- Schraagen JM, Chipman SF, & Shalin VL (Eds.). 2000. Cognitive task analysis . Hove, UK: Psychology Press. [ Google Scholar ]
- Schwarzmann M, Mease M, & Tollefson J 2010. Innovations in communication: Team building on a labor and delivery unit increases RN satisfaction . JOGNN , 39 ( 1 ), 75–76. [ Google Scholar ]
- Scott TM, & Martinek G 2006. Coaching positive behavior support in school settings: Tactics and databased decision making . Journal of Positive Behavior Interventions , 8 ( 3 ): 165–173. [ Google Scholar ]
- Sels L, Janssens M, & Van Den Brande I 2004. Assessing the nature of psychological contracts: A validation of six dimensions . Journal of OrganizationalBehavior , 25 ( 4 ): 461–488. [ Google Scholar ]
- Serfaty D, Entin EE, & Johnston JH 1998. Team coordination training In Cannon-Bowers JA & Salas E (Eds.), Making decisions under stress: Implications for individual and team training : 221–245. Washington, DC: American Psychological Association. [ Google Scholar ]
- Showers B 1987. Synthesis of research on staff development: A framework for future study and a state-of the- art analysis . Educational Leadership , 45 ( 3 ): 77–87. [ Google Scholar ]
- Shuffler ML, DiazGranados D, & Salas E 2011. There’s a science for that: Team development interventions in organizations . Current Directions in Psychological Science , 20 : 365–372. [ Google Scholar ]
- Shuffler ML, Jimenez-Rodriguez M, & Kramer WS 2015. The science of multiteam systems: A review and future research agenda . Small Group Research , 46 ( 6 ): 659–699. [ Google Scholar ]
- Shuffler ML, Kramer WS, & Burke CS 2016. #TeamLeadership: Leadership for today’s multicultural, virtual, and distributed teams In Wildman J & Griffith R (Eds.), Critical issues in cross-cultural management , 1–14. New York: Springer. [ Google Scholar ]
- Shuffler ML, Pavlas D, & Salas E 2012. Teams in the military: A review and emerging challenges In Laurence J & Matthews M (Eds.), Oxford handbook of military psychology , 282–310. New York: Oxford University Press. [ Google Scholar ]
- Shunk R, Dulay M, Chou CL, Janson S, & O’Brien BC 2014. Huddle-coaching: A dynamic intervention for trainees and staff to support team-based care . Academie Medicine , 89 ( 2 ): 244–250. [ PubMed ] [ Google Scholar ]
- Sims DE, Klein C, & Salas E 2006. Team-building . International Encyclopedia of Ergonomics and Human Factors , 2 : 2375–2397. [ Google Scholar ]
- Smith-Jentsch K, Cannon-Bowers J, Tannenbaum S, & Salas E 2008. Guided team self-correction: Impacts on team mental models, processes, and effectiveness . Small Group Research , 39 ( 3 ): 303–327. [ Google Scholar ]
- Smith-Jentsch KA, Zeisig RL, Acton B, & McPherson JA 1998. Team dimensional training: A strategy for guided team self-correction In Cannon-Bowers JA & Salas E (Eds.), Making decisions under stress: Implications for individual and team training , 271–297. Washington, DC: American Psychological Association. [ Google Scholar ]
- Smith EM, Ford JK, & Kozlowski SWJ 1997. Building adaptive expertise: Implications for training design strategies In Quiñones MA & Ehrenstein A (Eds.), Training for a rapidly changing work-place: Applications of psychological research , 89–118. Washington, DC: American Psychological Association. [ Google Scholar ]
- Steiner ID 1972. Group process andproductivity . New York: Academic Press. [ Google Scholar ]
- Stewart GL, & Barrick MR 2000. Team structure and performance: Assessing the mediating role of intra-team process and the moderating role of task type . Academy of Management Journal , 43 ( 2 ): 135–148. [ Google Scholar ]
- Stout RJ, Salas E, & Carson R 1994. Individua! task pro- ficiency and team process behavior: What’s important for team functioning? . Military Psychology , 6 ( 3 ): 177–192. [ Google Scholar ]
- Sundstrom E 1999. Supporting work team effectiveness: Best management practices for fostering high performance . San Francisco, CA, Jossey-Bass. [ Google Scholar ]
- Sverdrup TE, & Schei V 2015. “Cut Me Some Slack:” The psychological contracts as a foundation for understanding team charters . Journal of Applied Behavioral Science , 51 ( 4 ): 451–478. [ Google Scholar ]
- Swezey RW, Owens JM, Bergondy ML, & Salas E 1998. Task and training requirements analysis methodology (TTRAM): An analytic methodology for identifying potential training uses of simulator networks in teamwork-intensive task environments . Ergonomics , 41 ( 11 ): 1678–1697. [ PubMed ] [ Google Scholar ]
- Tannenbaum SI, Beard RL, & Salas E 1992. Team building and its influence on team effectiveness: An examination of conceptual and empirical devel- opments . Advances in Psychology , 82 :117–153. [ Google Scholar ]
- Tannenbaum SI, & Cerasoli CP 2012. Do team and individual debriefs enhance performance? A meta- analysis . Human Factors , 55 ( 1 ): 231–245. [ PubMed ] [ Google Scholar ]
- Tannenbaum SI, Mathieu JE, Salas E, & Cohen D 2012. On teams: Unifying themes and the way ahead . Industrial and Organizational Psychology , 5 ( 1 ): 5661. [ Google Scholar ]
- Tuckman BW 1965. Developmental sequence in small groups . PsychologicalBulletin , 63 ( 6 ): 384–399. [ PubMed ] [ Google Scholar ]
- Villado A 2009. The after-action review training approach: An integrative framework and empirical investigation . Dissertation Abstracts International: Section B: The Sciences and Engineering , 69 : 64–63. [ Google Scholar ]
- Volpe C, Cannon-Bowers J, Salas E, & Spector P 1996. The impact of cross-training on team functioning: An empirical investigation . Human Factors , 38 : 87–100. [ PubMed ] [ Google Scholar ]
- Wageman R 2001. How leaders foster self-managing team effectiveness: Design choices versus hands-on coaching . Organization Science , 12 ( 5 ): 559–577. [ Google Scholar ]
- Wageman R, Gardner H, & Mortensen M 2012. The changing ecology of teams: New directions for teams research . Journal ofOrganizational Behavior , 33 ( 3 ): 301–315. [ Google Scholar ]
- Wageman R, & Gordon FM 2005. As the twig is bent: How group values shape emergent task inter-dependence in groups . Organization Science , 16 ( 6 ): 687–700. [ Google Scholar ]
- Wageman R, Nunes DA, Burruss JA, &Hackman JR 2008. Senior leadership teams: What it takes to make them great . Boston, MA: Harvard Business School. [ Google Scholar ]
- Wang D, Waldman DA, & Zhang Z 2014. A meta-analysis of shared leadership and team effectiveness . Journal of Applied Psychology , 99 ( 2 ): 181–198. [ PubMed ] [ Google Scholar ]
- Weaver SJ,Dy SM, & Rosen MA 2014. Team-training in healthcare: A narrative synthesis of the literature . BMJ Quality & Safety , 23 : 359–372. [ PMC free article ] [ PubMed ] [ Google Scholar ]
- Weer CH, DiRenzo MS, &Shipper FM 2016. Aholistic view of employee coaching: Longitudinal investigation of the impact of facilitative and pressure-based coaching on team effectiveness . Journal of Applied Behavioral Science , 52 ( 2 ): 187–214. [ Google Scholar ]
- West P, Sculli G, Fore A, Okam N, Dunlap C, Neily J, & Mills P 2012. Improving patient safety and optimizing nursing teamwork using crew resource management techniques . Journal of Nursing Administration , 42 ( 2 ): 15–20. [ PubMed ] [ Google Scholar ]
- Wexler KJ 1990. Team building: A multidimensional analysis . Unpublished doctoral dissertation, Hofstra University, Hempstead. [ Google Scholar ]
- Wiener EL, Kanki BG, & Helmreich RL (Eds.). 2010. Crew resource management . New York: Academic Press. [ Google Scholar ]
- Wiese CW, Shuffler ML, & Salas E 2015. Teamwork and team performance measurement In Wright J (Ed.), International encyclopedia of the social & behavioral sciences , pp. 96–103. Oxford, UK: Pergamon. [ Google Scholar ]
- Wilkinson NL, & Moran JW 1998. Team charter . TQM Magazine , 10 : 355–361. [ Google Scholar ]
- Wilson KP, Dykstra JR, Watson LR, Boyd BA, & Crais ER 2012. Coaching in early education class-rooms serving children with autism: A pilot study . Early ChildhoodEducation Journal , 40 : 97–105. [ Google Scholar ]
- Woolley AW, Gerbasi ME, Chabris CF, Kosslyn SM, & Hackman JR 2008. Bringing in the experts: How team composition and collaborative planning jointly shape analytic effectiveness . Small Group Research , 39 ( 3 ): 352–371. [ Google Scholar ]
- Zaccaro SJ, Rittman AL, & Marks MA 2001. Team leadership . The Leadership Quarterly , 12 : 451–483. [ Google Scholar ]
- Zhao HAO, Wayne SJ, Glibkowski BC, & Bravo J 2007. The impact of psychological contract breach on work-related outcomes: A meta-analysis . Personnel Psychology , 60 ( 3 ): 647–680. [ Google Scholar ]
SYSTEMATIC REVIEW article
Analyzing the impact of team-building interventions on team cohesion in sports teams: a meta-analysis study.

- Department of Physical Education, Yonsei University, Seoul, Republic of Korea
Introduction: Participation in team sports requires collaboration among multiple individuals over an extended period. Success in the game relies on more than just individual excellence; it necessitates effective teamwork. Team-building interventions have been shown to enhance team functioning, particularly in fostering cohesion among sports teams. This study aims to identify crucial factors in team-building interventions that contribute to improved team cohesion in sports teams.
Methods: A comprehensive meta-analysis of 15 articles was conducted to identify the crucial factors in team-building interventions that contribute to improved team cohesion in sports teams. The analysis focused on the age of participants, level of performance, and duration of interventions.
Results: The results of the analysis revealed that the positive impact of team-building was found to be most pronounced when the participants were between 15 and 20 years old, performed at collegiate teams, and engaged in interventions lasting more than 2 weeks. Among the four types of cohesion in sports teams, individual attraction to the group task (ATG-T) emerged as the aspect most influenced by team-building interventions.
Discussion: These findings provide valuable insights into the factors influencing the success of team-building interventions in enhancing team cohesion within sports teams.
1 Introduction
Psychological interventions in sports have proven effective in enhancing athletes’ skill development, team cohesion, and team performance. Among these interventions, team-building has emerged as a prominent strategy for promoting effective collaboration among team members, thereby strengthening cohesion and team performance in sports teams. This approach has been employed to optimize the functionality of sports teams, resulting in improved team performance.
This study aims to explore the impact of team-building interventions on cohesion within sports teams. While numerous investigations have reported favorable effects of team-building on team cohesion ( Cogan and Petrie, 1995 ; Prapavessis et al., 1996 ; Stevens and Bloom, 2003 ; Senécal et al., 2008 ; Kim and Kim, 2012 ; Durdubas and Koruc, 2023 ; Tassi et al., 2023 ), it remains challenging to assert that team-building interventions yield effective results. Some studies, such as those by Bloom and Stevens (2002) , Kilty (2000) , Kwon (2022) , Prapavessis et al. (1996) , and Rainey and Schweickert (1988) , did not report positive developments in group cohesion.
Moreover, improvements in cohesion achieved through team-building interventions were sometimes transient, with studies indicating that cohesion levels were not sustained throughout the season ( Cogan and Petrie, 1995 ; Stevens and Bloom, 2003 ). Drawing definitive findings about the effectiveness of team-building in sports is complicated by the diversity of methods and designs employed in these interventions, which yield unexpected results and necessitate an integrated examination of previous studies.
In the meta-analysis conducted by Carron et al. (2002) , the impact of team-building on four subgroups of cohesion – GI-T (group integration–task), GI-S (group integration–social), ATG-T (individual attractions to the group-task), and ATG-S (individual attractions to the group-social) – was examined, with reported effect sizes of 0.471, 0.349, 0.676, and 0.463. Martin et al. (2009) conducted a meta-analysis on team-building interventions within sports teams, reporting an effect size of 0.427. Their analysis revealed that team-building interventions had the most substantial impact on cognitions ( g = 0.799), with goal setting as the exclusive method coming in second ( g = 0.714). The effect sizes of task and social cohesion were 0.263 and 0.214.
While team-building is known to have a positive effect on team cohesion, in actual application, its implementation time is limited. Therefore, to ensure that the cohesion effect is evident in sports teams, understanding the factors that should be considered in team-building interventions is crucial. This study seeks to determine which moderator variables such as gender, age, athletes’ level, group size, and intervention duration, enhance the effect and which factors do not need to be considered.
2 Methodology
This methodology conforms to the relevant guidelines of the Preferred Reporting Items of Systematic Reviews and Meta-Analyses (PRISMA) Statement and ensures that the necessary scientific information is provided in the field ( Page et al., 2021 ).
2.1 Study selection and inclusion criteria
For this meta-analysis, literature selection focused on research studies examining the effectiveness of team-building interventions in interactive sport teams. The selection process followed rigorous and systematic procedures, incorporating keyword searches in computerized databases and employing a snowball sampling approach.
The computer-based search covered various databases, including PsychINFO, PsycARTICLES, SPORT Discus, and Google Scholar. This comprehensive search strategy involved using a range of keywords, such as “team-building in sport,” “team-building intervention in sport,” “team-building and cohesion,” and various combinations.
Two independent reviewers extracted the following data from each article: study design, total number of participants, gender, age, intervention duration, and athletes’ skill level. The accuracy of the extracted or calculated data was verified by comparing the data collection forms of the two investigators.
2.2 Dependent variables: cohesion
Team-building in sports teams can yield various outcomes, including enhanced cohesion. Carron and Spink (1993) developed a conceptual framework for team-building interventions in sports teams, designating group cohesiveness as the primary result of this process. Within this framework, four subgroups of cohesion, specifically GI-T, GI-S, ATG-T, and ATG-S, serve as dependent variables when assessing the impact of team-building interventions ( Eys and Kim, 2017 ).
2.3 Moderating factors
2.3.1 gender.
Within the studies under review, two distinct demographic cohorts were examined. Specifically, 5 studies with 38 cases focused on male participants, while 10 studies with 14 cases centered around female participants.
2.3.2 Age of participants
The participants’ ages were divided into three groups: under the age of 15, 15–20 years old, and over 20. Specifically, two studies with eight cases focused on participants under 15, while nine studies with 29 cases targeted the 15–20 age group, and four studies with 15 cases focused on participants over the age of 20.
2.3.3 Sample size
The sample size was categorized into three groups: under 20 participants, 20–30 participants, and over 30 participants. More specifically, five studies with 17 cases were centered on under 20 participants, while another five studies with 18 cases were aimed at the 20–30 participants group. Additionally, five studies with 17 cases were focused on participants comprising over 30 participants.
2.3.4 Skill level
The analysis covered a range of team proficiency levels. High school and collegiate teams were each represented in five studies with 16 effect sizes, whereas professional club teams were featured in five studies with 20 effect sizes.
2.3.5 Length of intervention
This study also investigated the duration of a team-building intervention as a potential moderator for their effectiveness. The intervention durations were classified into three groups: less than 2 weeks, 2 to 20 weeks, and 20 weeks or more. There were 8 studies with 32 cases that fell within the 2 to 20 weeks category, while 6 studies with 18 cases had intervention lasting over 20 weeks. Additionally, one study with two cases had an intervention duration of less than 2 weeks.
2.4 Coding methodology
Following established norms for meta-analytic research, we meticulously designed our coding procedure to thoughtfully capture and quantify crucial study characteristics and outcomes. Our comprehensive coding approach involved systematically extracting 11 essential pieces of information from each study. This included details such as authorship, year of publication, study setting, study design type, sport type, duration of intervention, athletes’ skill level, gender of participants, number of participants in experimental and control groups, means and standard deviations of intervention effectiveness at pretest and posttest, as well as effect size or measures of effectiveness.
2.5 Effect size calculations
The computation of effect sizes was conducted using R-4.3.2 for Windows. 1 This program provides various options for calculating effect sizes, and we chose Hedges g ( Hedges and Olkin, 2014 ), an effect size adjusted to consider differences in sample size and sample variance. In interpreting the magnitude of effect sizes, we followed Cohen’s (1988) guidelines. Specifically, a Hedges g of 0.80 was considered a large effect size, 0.50 signified a medium effect size, and 0.20 indicated a small effect size.
3.1 Study selection
Following a database search, a total of 1,928 documents were initially identified, with 35 documents found through snowballing methods. After removing duplicates, 1,752 articles remained. Subsequently, 525 articles were excluded based on title screening. Application of the inclusion criteria led to the exclusion of an additional 664 articles. This left us with 121 articles that underwent full-text screening, focusing on articles potentially relevant to the impact of team-building interventions on cohesion in sports teams. To ensure methodological rigor, studies lacking the necessary statistical information for calculating effect sizes were excluded from the meta-analysis. Following these criteria, a total of 15 studies, comprising 52 cases, were considered eligible for inclusion in the meta-analysis (refer to Figure 1 for details).
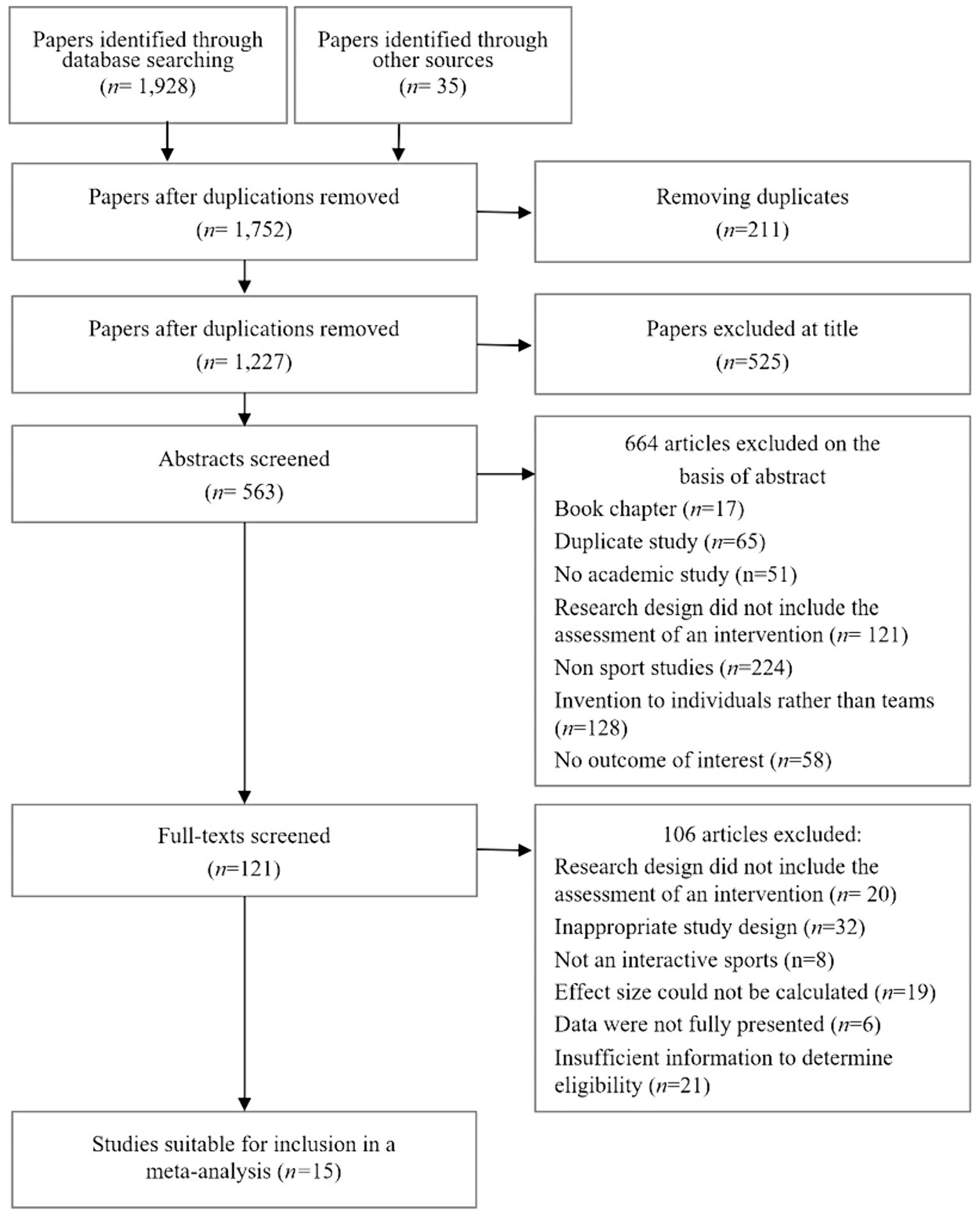
Figure 1 . Flowchart of the systematic review process according to the PRISMA protocol declarations.
3.2 Assessment of risk of bias
To assess the risk of bias in the included articles, we used the Cochrane Risk of Bias Tool ( Higgins and Altman, 2008 ). This tool assesses each article based on a checklist comprising five items: randomization process, deviation from the intended intervention, missing outcome data, measurement of the outcome, and selection of the reported result. We then categorized each article’s overall bias risk as low risk (indicating low risk across all items), some concerns, and high risk (indicating high risk of bias in at least one domain). Low risk indicates better methodological quality, while high risk suggests a high risk of bias.
Figure 2 provides a visual representation of risk of bias evaluations for each domain of the Cochrane Risk of Bias tool. Out of all included articles, 1 article (6.7%) had a low overall risk of bias, while 14 articles (93.3%) exhibited a high overall risk of bias. However, except for the randomization process domain, the other four checklist items showed low risk across all 15 articles.
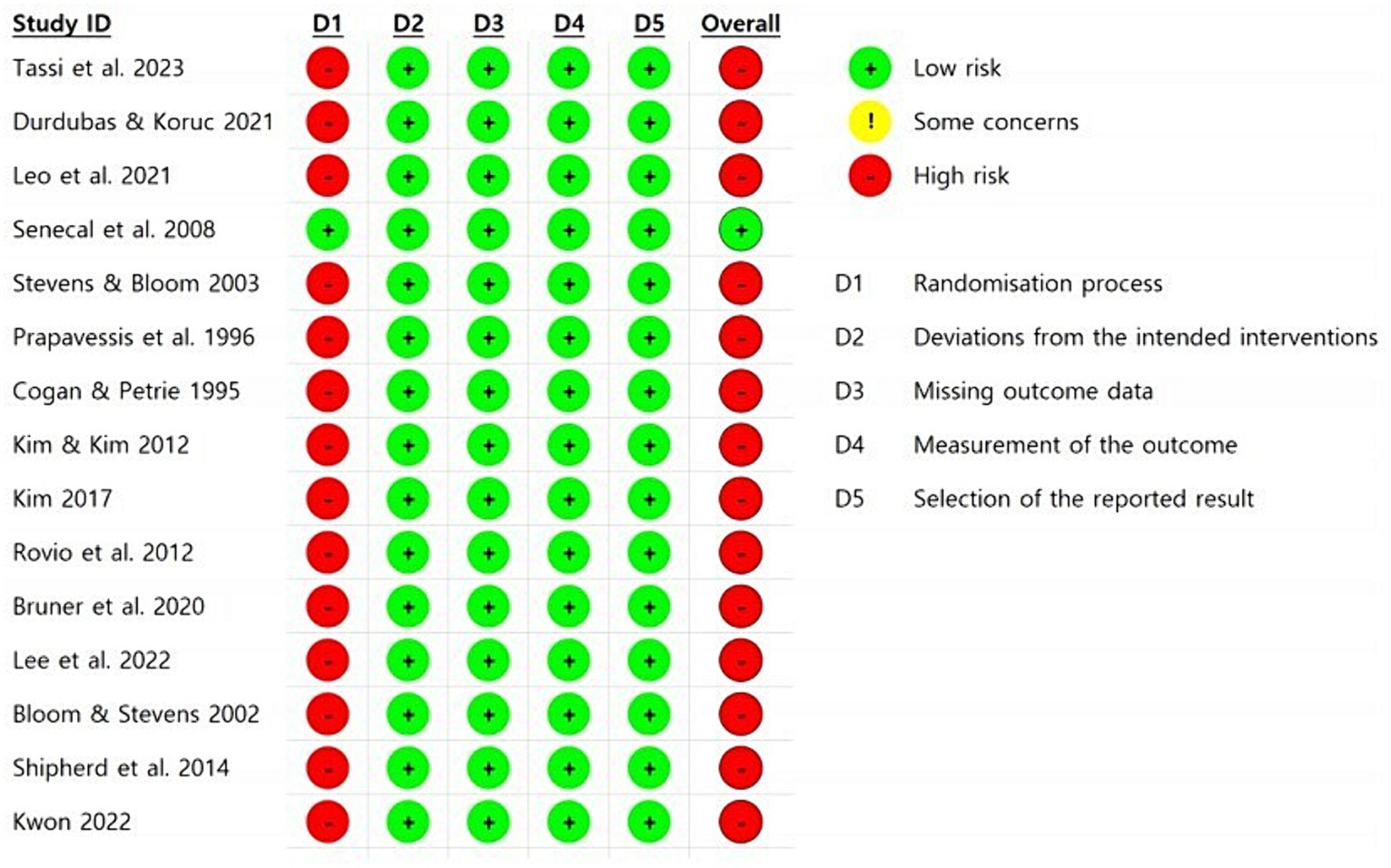
Figure 2 . Assessment of risk of bias in the included studies.
The high prevalence of ‘high’ risk is attributed to the inherent challenges in randomly selecting teams, particularly in studies involving interactive sports teams. This difficulty arises from the complexities associated with randomly assigning teams in research focused on sports team dynamics.
3.3 Overall analysis
3.3.1 overall effect size.
The meta-analysis results, drawn from 52 individual cases extracted from 15 papers, are presented in Table 1 . The table covers both the overall analysis and outcomes related to five moderating variables influencing cohesion. Additionally, Figure 3 illustrates a forest plot depicting effect sizes for the 52 individual cases. The overall analysis of these cases showed a significant moderate effect size (ES = 0.65, 95% CI = [0.40; 0.91]) of team-building intervention on cohesion. Additionally, the I 2 heterogeneity statistic indicated a significant level of heterogeneity at 96.9%.
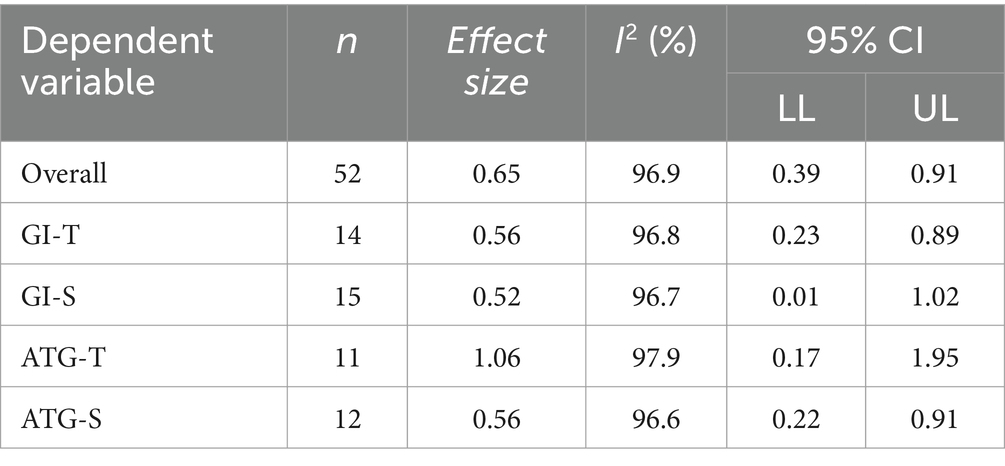
Table 1 . Effect sizes of dependent variables.
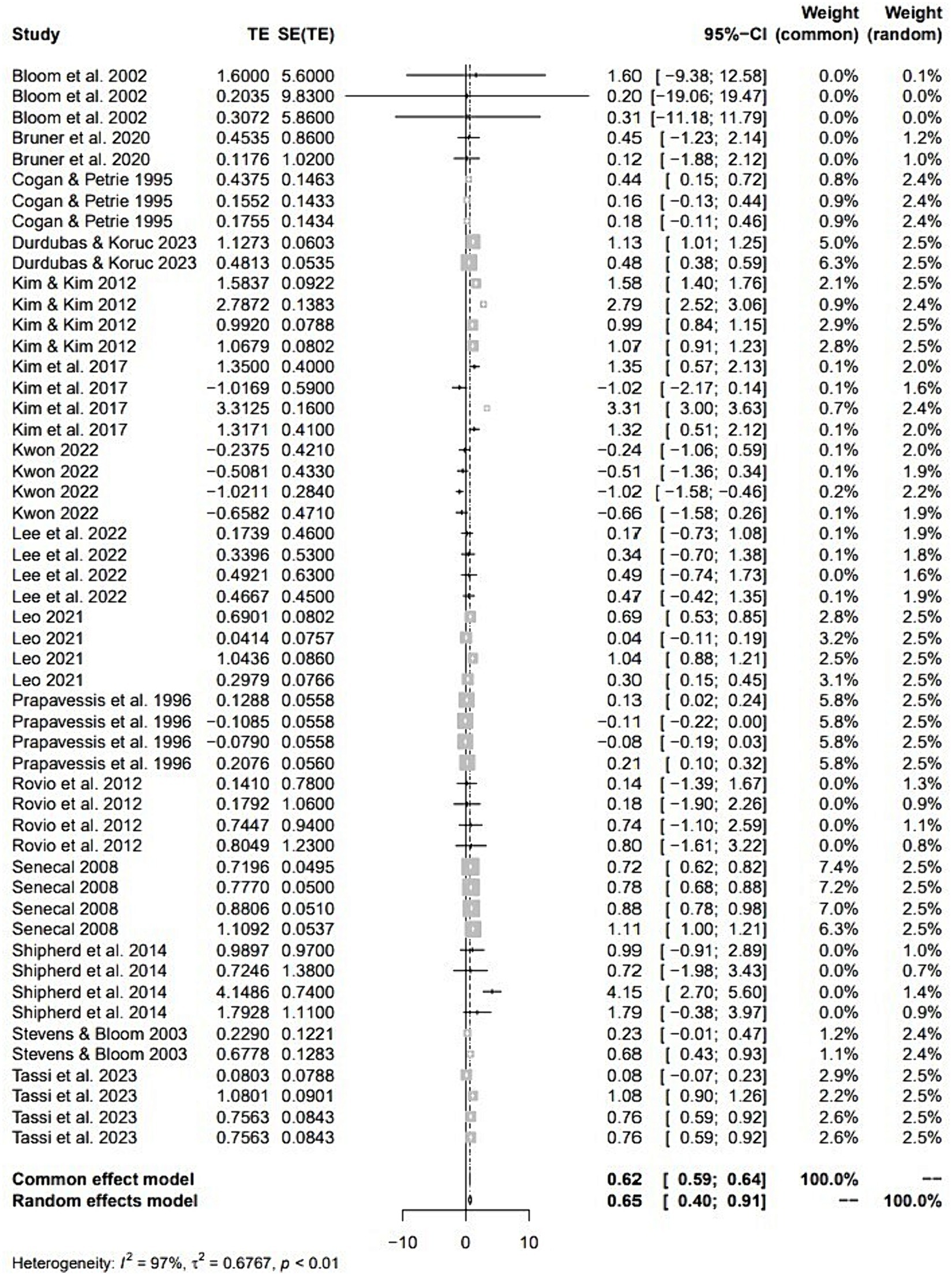
Figure 3 . Forest plot of meta-analysis for team building intervention on cohesion in sports teams. The individual effect sizes are identified as Hedges g with lower and upper limits of 95% CIs.
3.3.2 Publication bias
To assess the potential presence of publication bias in our meta-analysis of team-building intervention on cohesion, we utilized a funnel plot for visual examination, as illustrated in Figure 4 . In an ideal scenario without publication bias, data points (depicted as solid circles) from individual case studies would exhibit a symmetrical distribution. Any deviation from this symmetry suggests the potential presence of publication bias. As seen in Figure 4 , the distribution of effect sizes is slightly left–skewed.
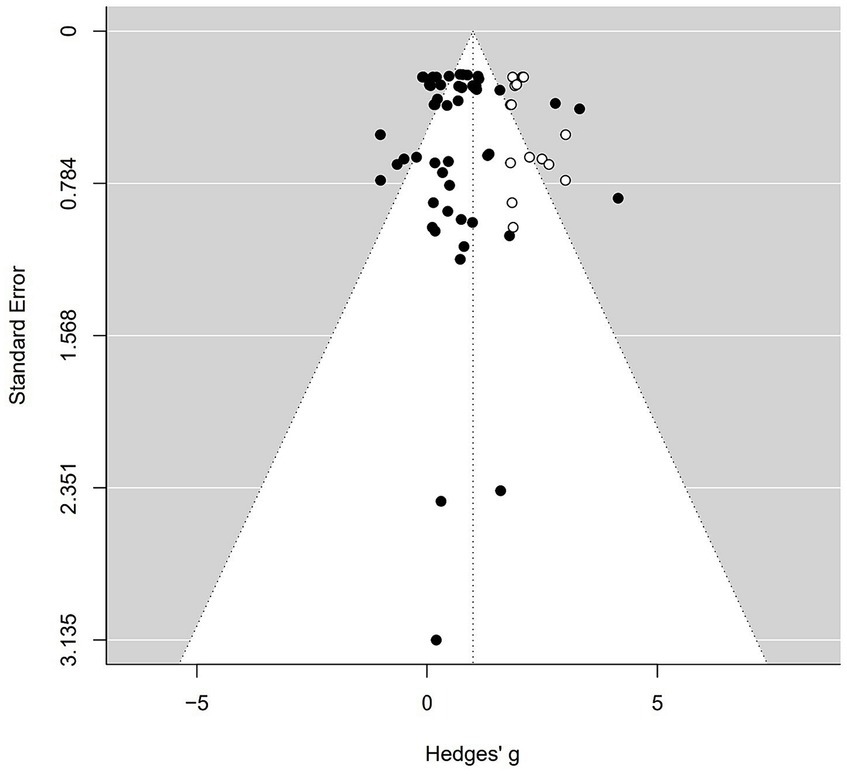
Figure 4 . Funnel plot of standard error by Hedges g.
Applying the trim-and-fill method by Duval and Tweedie (2000) reveals that 15 missing studies on the right side are required to achieve symmetry in the funnel plot. The required 15 additional cases are shown on the right as hollow circles in Figure 4 .
We also assessed publication bias using Rosenthal’s (1979) fail-safe N (N fs ) concept. When N fs exceeds 5 k + 10, where k represents the number of included case studies, it is unlikely to substantially impact the average effect size. In our specific study, with k equal to 52, the meta-analysis results remain stable as long as the N fs exceeds 270. Our N fs value is 2,570, well above the 270 threshold, emphasizing the robustness of the meta-analysis. In simpler terms, even if more than 2,570 studies with zero effect size were introduced, the overall results would remain largely unaltered.
According to the trim-and-fill method by Duval and Tweedie (2000) , an adjusted effect size of 1.00 (95% CI = [0.75; 1.25]), larger than the calculated effect size of 0.65, is presented.
3.4 Type of cohesion measure
Table 1 presents 52 effect sizes calculated for four cohesion types (GI-T, GI-S, ATG-T, and ATG-S). Notably, task cohesion exhibited a larger effect size than social cohesion. ATG-T showed a significant large effect size (ES = 1.06, 95% CI = [0.17; 1.95]). The other three cohesion types, GI-T (ES = 0.56, 95% CI = [0.23; 0.89]), ATG-S (ES = 0.56, 95% CI = [0.22; 0.91]), and GI-S (ES = 0.52, 95% CI = [0.01; 1.02]), showed a moderate effect size. According to meta-ANOVA, the differences between the four cohesion types were not statistically significant ( F (3, 48) = 1.312, p > 0.05).
3.5 Moderator variables
This study examined the effectiveness of team-building concerning five different moderators. These moderators encompassed the effectiveness of team-building on cohesion across gender, age, sample size, intervention duration, and athletes’ skill level. Notably, the only significant moderator identified was athletes’ skill level. No statistically significant differences were observed within the other four moderators (refer to Table 2 for details).
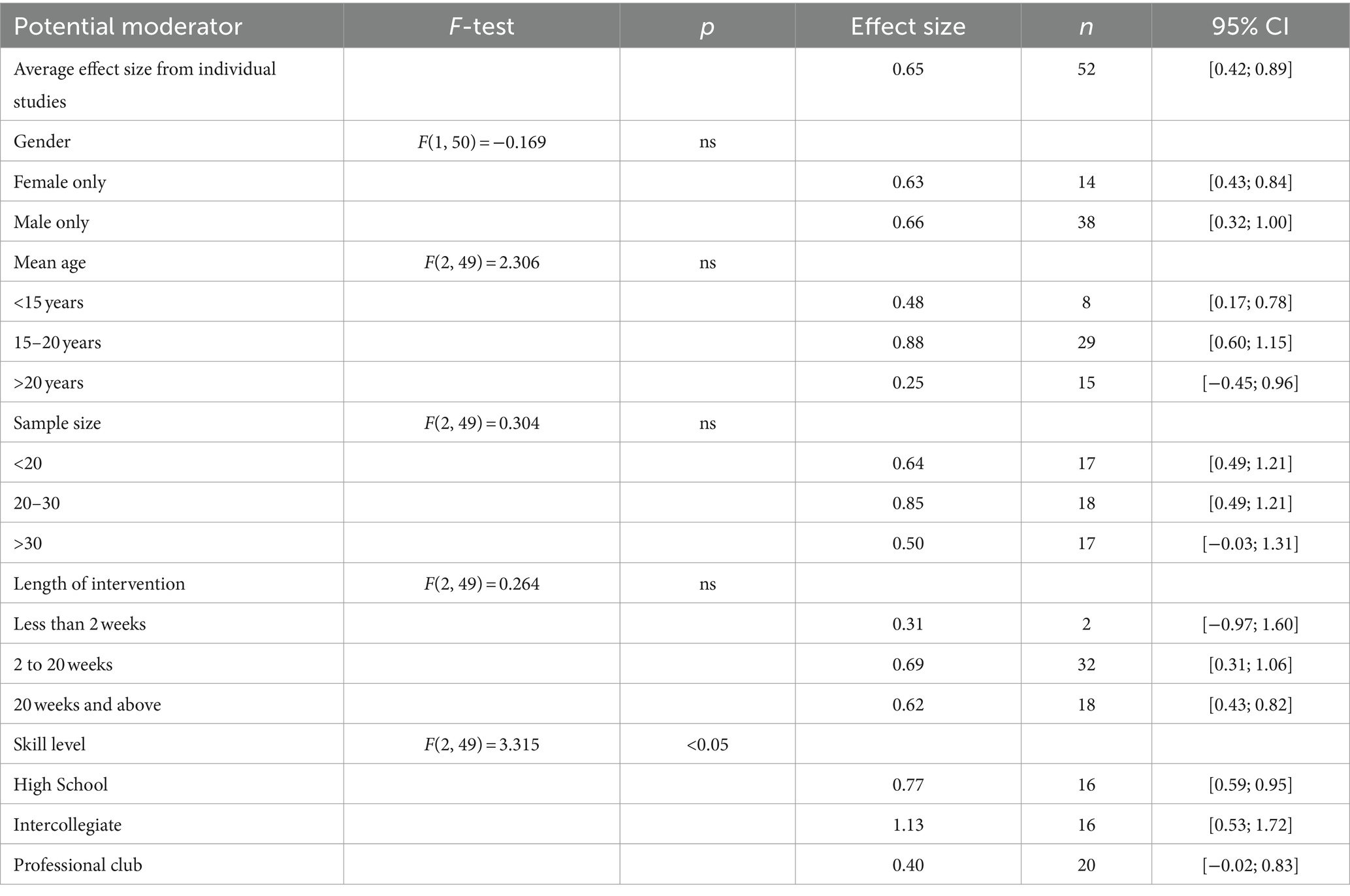
Table 2 . Moderator effects.
3.5.1 Gender
As indicated in Table 2 , there is a slightly larger effect size for male athlete teams (ES = 0.66, 95% CI = [0.32; 1.00]) compared to female athlete teams (ES = 0.63, 95% CI = [0.43; 0.84]). However, the difference is not statistically significant ( p > 0.05).
We categorized the ages of the participants into three groups. In the 15–20 years old category, we observed a significant large effect size (ES = 0.88, 95% CI = [0.60; 1.15]), while those under the age of 15 showed a significant moderate effect size (ES = 0.48, 95% CI = [0.17; 0.78]). However, the effect size (ES = 0.25, 95% CI = [−0.45; 0.96]) for those over the age of 20 was not statistically significant. The meta-ANOVA analysis indicated that the difference between these three categories was not statistically significant ( p > 0.05). Consequently, age was not identified as a significant moderator in this study.
3.5.3 Sample size
The sample size was divided into three groups. In the category with 20–30 participants, we observed a significant large effect size (ES = 0.85, 95% CI = [0.49; 1.21]). Additionally, the category with under 20 participants showed a significant moderate effect size (ES = 0.64, 95% CI = [0.49; 1.21]). However, the effect size (ES = 0.50, 95% CI = [−0.03; 1.31]) for those over 30 participants was not statistically significant. The meta-ANOVA analysis indicated that the difference between these three categories was not statistically significant ( p > 0.05). Consequently, the sample size was not identified as a significant moderator in this study.
3.5.4 Length of intervention
The team-building interventions in our study varied in duration, ranging from 1 day to the entire sports season. As shown in Table 2 , a significant moderate effect size (ES = 0.69, 95% CI = [0.31; 1.06]) was observed for interventions lasting between 2 and 20 weeks. Additionally, a significant moderate effect size was evident for interventions extending for 20 weeks or longer (ES = 0.62, 95% CI = [0.43; 0.82]). However, the effect size (ES = 0.31, 95% CI = [−0.97; 1.60]) for intervention durations less than 2 weeks was not statistically significant. The meta-ANOVA analysis indicated that the difference between these three categories was not statistically significant ( p > 0.05). Consequently, the length of intervention was not identified as a significant moderator in this study.
3.5.5 Skill level of the athletes
As outlined in Table 2 , we observed a significant large effect size (ES = 1.13, 95% CI = [0.53; 1.72]) in the category of collegiate teams, while we identified a significant moderate effect size (ES = 0.77, 95% CI = [0.59; 0.95]) in the category of high school teams. However, the effect size (ES = 0.40, 95% CI = [−0.02; 0.83]) was not statistically significant for professional teams.
According to the meta ANOVA and post-hoc test results, significant differences ( p < 0.05) in the effectiveness of team-building on cohesion were found between collegiate teams and professional teams. Consequently, athletes’ skill level can act as a moderator in the effectiveness of team-building intervention on cohesion.
3.6 Meta-regression analysis
We conducted meta-regression analyses to explore the association between three independent variables (age, sample size, and duration in weeks) and the effect size. The results of meta-regression analysis showed that the effect size tend to decrease with mean age, although this association did not reach statistical significance ( p > 0.05) (refer to Figure 5 and Table 3 ). Furthermore, the relationships between sample size and effect sizes, as well as the relationship between duration in weeks and effect sizes, did not show statistical significance ( p > 0.05) (refer to Table 3 ).
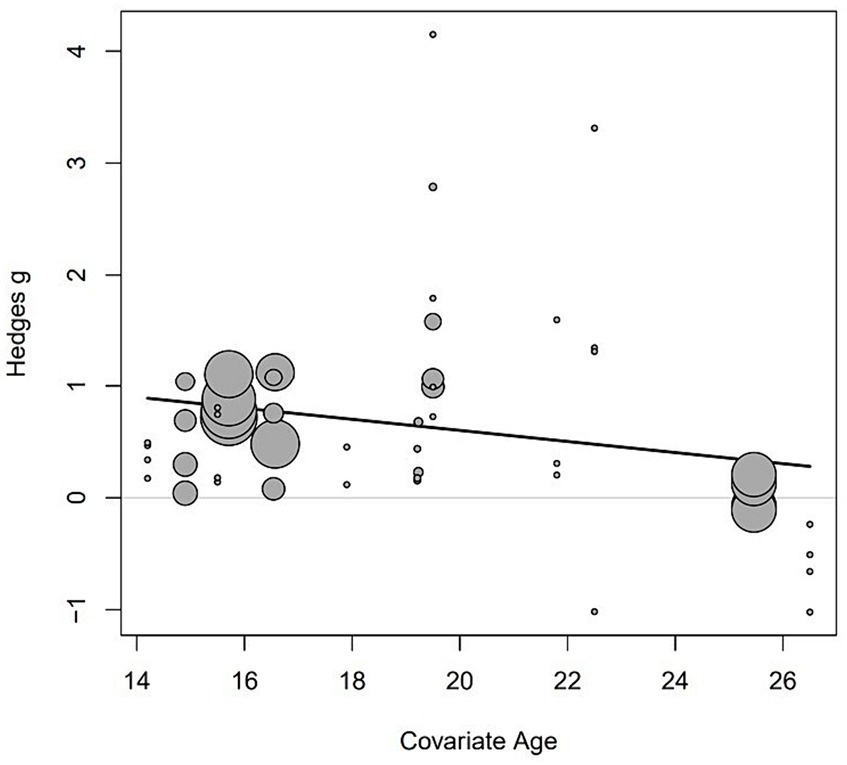
Figure 5 . Meta-regression analysis of the relationship between Hedges’ g and the mean age of participants.
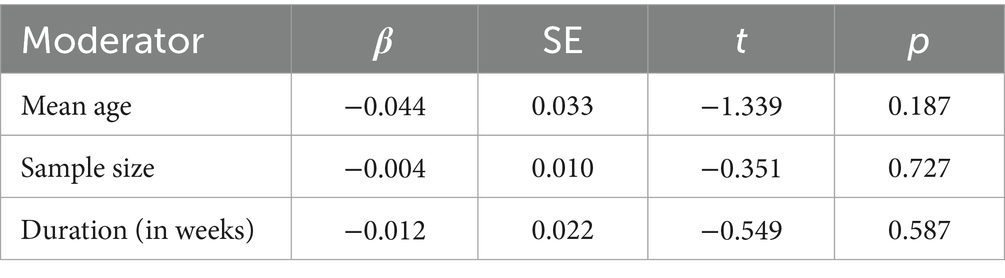
Table 3 . Univariate meta-regression analysis.
4 Discussion
The main goal of this meta-analysis is to assess the impact of team-building interventions on cohesion, a critical element in sports teams that plays a pivotal role in task execution and fostering social interactions ( Carron and Spink, 1993 ; Carron et al., 1997 ). If team-building interventions focused on fostering cohesion can establish a sense of unity among team members, they have the potential to serve as catalysts for enhancing overall team performance.
Our study’s key finding is that team-building activities indeed improve cohesion in sports teams. Among various measures of cohesion, we found that team-building interventions were most successful in enhancing ATG-T, followed by GI-T, GI-S, and ATG-S. Some team-building activities focus on social aspects, like team camping trips ( Cogan and Petrie, 1995 ), ropes and challenge courses (e.g., Meyer, 2000 ), and informal social gatherings (e.g., Yukelson, 1997 ). These activities are likely to enhance social cohesion within the team. On the other hand, other team-building activities concentrated on team goals and tasks, such as team goal-setting (e.g., Senécal et al., 2008 ; Kim et al., 2017 ; Durdubas and Koruc, 2023 ), tasks relevant to team performance (e.g., Leo et al., 2021 ), clarifying roles (e.g., Tassi et al., 2023 ), and adhering to team norms (e.g., Prapavessis et al., 1996 ). These activities are expected to primarily improve task cohesion within the team. Notably, our analysis revealed a stronger impact of team-building activities on task cohesion compared to social cohesion due to the predominant focus on tasks and objectives rather than social interactions in the studies examined.
Another aim of our study is to explore how various moderator variables affect the improvement of cohesion through team-building intervention. Several findings are associated with the influence of moderators. To begin with, we explored gender as a potential moderator. The findings indicate that team-building interventions are equally effective for teams composed solely of females as well as those with only males. In our meta-analysis, using gender served as a potential moderator, the results of the meta t -test showed no significant difference ( p > 0.05) in the effectiveness of team-building interventions applied to both men’s and women’s teams. This aligns with the results reported by Martin et al. (2009) .
In this study, the second potential modulator under scrutiny was the age of participants. We categorized subjects of individual study into three age groups, and then the effect size was calculated with age as a moderate variable. We found that the age category of 15–20 exhibited a large effect size, while the category under 15 years old showed a significant moderate effect size. However, there was no significant effect size observed for the category of those aged over 20 years. Consequently, we can conclude that team-building is most effective for sports teams with members between 15 and 20 years old, while it does not show effectiveness for sports teams with members aged over 20.
In our analysis, the third potential modulator we explored was sample size. We classified the sample size of each study into three groups, and then the effect size was calculated with sample size as a moderate variable. In the group with 20–30 participants, a significant large effect size was observed, while the category with under 20 participants showed a significant moderate effect size. However, there was no significant effect size observed for the category of those with over 30 participants. As a result, we can conclude that team-building is most effective for sports teams ranging from 20 to 30 members, while it does not show effectiveness for sports groups with over 30 members.
In our analysis, the fourth potential modulator we explored was athletes’ skill level, which turned out to be the only significant moderator in this study. Team-building interventions were most effective for collegiate teams, followed by high school teams, while the effectiveness in professional teams did not reach statistical significance ( p > 0.05). This discrepancy may be explained by a potential ceiling effect, given that professional athletes typically possess a strong understanding of cohesion. Consequently, while professional teams do benefit from team-building interventions, the extent of improvement may be comparatively modest due to their already robust cohesion and training. The meta-ANOVA indicated that the differences between the three groups were statistically significant ( p < 0.05), and the post-hoc test revealed that the effect size of the collegiate team was larger than that of the professional club team. Thus, it can be concluded that team-building is most effective for collegiate sports teams, while it does not show effectiveness for professional club teams.
Moving on to the fifth potential modulator, we explored intervention duration. The articles in this meta-analysis encompassed team-building interventions with durations ranging from a single day to an entire sports season. Notably, interventions lasting less than 2 weeks did not yield noticeable improvements in cohesion and were not statistically significant, aligning with the findings of Martin et al. (2009) . Conversely, Shipherd et al. (2014) conducted a single-day team-building intervention with a collegiate rugby team and observed a significant increase in team cohesion. These disparities in intervention duration underscore the need for meta-analytic investigations to gain a comprehensive understanding of the optimal duration required for team-building interventions to enhance cohesion in future studies.
Although numerous studies have demonstrated the positive effects of team-building interventions on cohesion, there are instances, as seen in some studies ( Prapavessis et al., 1996 ; Kwon, 2022 ), where significant improvements were not observed. The intervention period might have impacted why there wasn’t a significant change in group cohesion after the team-building program was implemented. Kwon (2022) and Prapavessis et al. (1996) conducted a team-building intervention over 8 weeks but did not find a clear improvement in group cohesion. This suggests that the intervention duration might have been too short to see significant differences in these studies. Group cohesion improves gradually through changing members’ perceptions and resolving conflicts that arise during interactions. Therefore, steady progress over a long enough time is important. However, conducting long-term team-building interventions can be challenging due to various environmental factors.
5 Conclusion
In conclusion, this study provides several key insights into the impact of team-building intervention on cohesion within sports teams. Firstly, team-building activities predominantly enhance task cohesion rather than social cohesion within sports teams. Different approaches to team-building, focusing on either social interactions or team goals and tasks, result in corresponding improvements in cohesion. Thus, social cohesion benefits from team-building activities emphasizing social interaction, while task cohesion improves when activities concentrate on team objectives.
Secondly, team-building interventions are most effective for individuals aged 15–20 and within collegiate sports teams. Conversely, the expected positive effects may not be noticeable when subjects are over 20 years old and belong to professional league teams.
Thirdly, interventions lasting longer than 2 weeks are crucial for enhancing team cohesion. Conversely, the expected positive effects may not be noticeable if the intervention period is less than 2 weeks. Based on our findings, an intervention period of at least 2 weeks is necessary to see the effects of a team-building intervention on group cohesion in sports teams. However, it is not necessarily the case that a longer intervention period will result in a greater intervention effect. Additionally, the time delay of the intervention was not investigated in this study. Therefore, the association between the team-building intervention period and group cohesion remains unclear. Further research is needed to determine the optimal intervention period that significantly affects group cohesion. It is also important to consider the time delay of intervention. Furthermore, there is possibility that a group cohesion may be influenced by multiple processes rather than just team-building alone. Therefore, claiming that team-building alone enhances group cohesion may not be reasonable. Therefore, decision-makers in sports teams should carefully consider the duration and realistic expectations of team-building interventions. In any case, to have an effective team-building intervention, it is necessary to implement the intervention for a long enough period. To address this, leaders should ensure interventions are implemented over a sufficient period to yield meaningful results.
In summary, team-building interventions can significantly enhance cohesion within sports teams, particularly when tailored to specific team dynamics and implemented over a sufficient duration.
Nevertheless, it’s important to note the limitations of this meta-analysis. First and foremost, the study focused exclusively on interactive sports, suggesting the need for future research to explore and compare the effectiveness of team-building interventions in both interactive and coactive sports settings. Secondly, the review concentrated solely on immediate post-intervention effects, emphasizing the necessity for longitudinal studies to gain a more profound understanding of the lasting benefits of team-building interventions for sports teams over an extended period.
Data availability statement
The raw data supporting the conclusions of this article will be made available by the author, without undue reservation.
Author contributions
SK: Data curation, Formal analysis, Investigation, Methodology, Validation, Visualization, Writing – original draft, Writing – review & editing.
The author(s) declare that no financial support was received for the research, authorship, and/or publication of this article.
Conflict of interest
The author declares that the research was conducted in the absence of any commercial or financial relationships that could be construed as a potential conflict of interest.
Publisher’s note
All claims expressed in this article are solely those of the authors and do not necessarily represent those of their affiliated organizations, or those of the publisher, the editors and the reviewers. Any product that may be evaluated in this article, or claim that may be made by its manufacturer, is not guaranteed or endorsed by the publisher.
1. ^ r-project.org
Note: References highlighted by an asterisk (*) were included in the meta-analysis.
Google Scholar
*Bloom, G. A., and Stevens, D. E. (2002). Case study: a team-building mental skills training program with an intercollegiate equestrian team. Athletic Insight J. Sport Psychol. 4, 1–16.
Carron, A. V., Colman, M. M., Wheeler, J., and Stevens, D. (2002). Cohesion and performance in sport: a meta-analysis. J. Sport Exerc. Psychol. 24, 168–188. doi: 10.1123/jsep.24.2.168
Crossref Full Text | Google Scholar
Carron, A. V., and Spink, K. S. (1993). Team building in an exercise setting. Sport Psychol. 7, 8–18. doi: 10.1123/tsp.7.1.8
Carron, A. V., Spink, K. S., and Prapavessis, H. (1997). Team building and cohesiveness in the sport and exercise setting: use of indirect interventions. J. Appl. Sport Psychol. 9, 61–72. doi: 10.1080/10413209708415384
*Cogan, K. D., and Petrie, T. A. (1995). Sport consultation: an evaluation of a season-long intervention with female collegiate gymnasts. Sport Psychol. 9, 282–296, doi: 10.1123/tsp.9.3.282
Cohen, J. (1988). Statistical power analysis for the behavioral sciences (2nd ed.). Hillsdale, NJ: Erlbaum.
*Durdubas, D., and Koruc, Z. (2023). Effects of a multifaceted team goal-setting intervention for youth volleyball teams. J. Appl. Sport Psychol. 35, 224–243, doi: 10.1080/10413200.2021.2021564
Duval, S., and Tweedie, R. (2000). Trim and fill: a simple funnel-plot–based method of testing and adjusting for publication bias in meta-analysis. Biometrics 56, 455–463. doi: 10.1111/j.0006-341X.2000.00455.x
PubMed Abstract | Crossref Full Text | Google Scholar
Eys, M., and Kim, J. (2017). Team building and group cohesion in the context of sport and performance psychology . Oxford Research Encyclopedia of Psychology. Oxford.
Hedges, L. V., and Olkin, I. (2014). Statistical methods for meta-analysis . San Diego, CA, USA: Academic Press.
Higgins, J. P., and Altman, D. G. (2008). Assessing risk of bias in included studies. In: Higgins, JPT , S Green , eds. Cochrane handbook for systematic reviews of interventions . Chichester, UK: Wiley, 187–241.
Kilty, K.M. (2000). A study of cohesion in women’s sports teams using adventure programming . Unpublished doctoral dissertation. Boston University, Boston, United States.
*Kim, Y. S., and Kim, B. J. (2012). The change of team cohesion in a university baseball team by applying team-building intervention. Korean J. Sports Sci. , 23, 334–342.
*Kim, Y., Park, S., and Kim, T. (2017). The development of a team building program for Korean curling team. Int. J. Appl. Sports Sci. 29, 155–168, doi: 10.24985/ijass.2017.29.2.155
*Kwon, S. H. (2022). A team building intervention case study of a male handball team. J. Coach. Dev. 24, 103–112, doi: 10.47684/jcd.2022.03.24.1.103
*Leo, F. M., Gonzalez-Ponce, I., Lopez-Gajardo, M. A., Pulido, J. J., and Garcia-Calvo, T. (2021). Team building intervention program and its relationship with group processes in young athletes. Int. J. Sport Psychol. 52, 120–136.
Martin, L. J., Carron, A. V., and Burke, S. M. (2009). Team building interventions in sport: a meta-analysis. Sport Exerc. Psychol. Rev. 5, 3–18. doi: 10.53841/bpssepr.2009.5.2.3
Meyer, B. B. (2000). The ropes and challenges course: a quasi-experimental examination. Percept. Mot. Skills 90, 1249–1257. doi: 10.2466/pms.2000.90.3c.1249
Page, M. J., McKenzie, J. E., Bossuyt, P. M., Boutron, I., Hoffmann, T. C., Mulrow, C. D., et al. (2021). The PRISMA 2020 statement: an updated guideline for reporting systematic reviews. Int. J. Surg. 88:105906. doi: 10.1016/j.ijsu.2021.105906
*Prapavessis, H., Carron, A. A., and Spink, K. S. (1996). Team building in sport. Int. J. Sport Psychol. , 27, 269–285.
Rainey, D. W., and Schweickert, G. J. (1988). An exploratory study of team cohesion before and after a spring trip. Sport Psychol. 2, 314–317. doi: 10.1123/tsp.2.4.314
Rosenthal, R. (1979). The file drawer problem and tolerance for null results. Psychol. Bull. 86, 638–641. doi: 10.1037/0033-2909.86.3.638
*Senécal, J., Loughead, T. M., and Bloom, G. A. (2008). A season-long team-building intervention: examining the effect of team goal setting on cohesion. J. Sport Exerc. Psychol. , 30, 186–199, doi: 10.1123/jsep.30.2.186
*Shipherd, A. M., Basevitch, I., Renner, K. B., and Siwatu, K. O. (2014). Development and evaluation of a team building intervention with a US collegiate Rugby team: a mixed methods approach. J. Multidiscip. Res. 6, 31–48.
*Stevens, D., and Bloom, G. (2003). The effect of team building on cohesion. Avante Ontario 9, 43–54.
*Tassi, J. M., López-Gajardo, M. A., Leo, F. M., Díaz-García, J., and García-Calvo, T. (2023). An intervention program based on team building during tactical training tasks to improve team functioning. Front. Psychol. , 14,:1065323, doi: 10.3389/fpsyg.2023.1065323
Yukelson, D. (1997). Principles of effective team building interventions in sport: a direct services approach at Penn State University. J. Appl. Sport Psychol. 9, 73–96. doi: 10.1080/10413209708415385
Keywords: group cohesion, group-based intervention, interactive sports, meta-analysis, teambuilding
Citation: Kwon SH (2024) Analyzing the impact of team-building interventions on team cohesion in sports teams: a meta-analysis study. Front. Psychol . 15:1353944. doi: 10.3389/fpsyg.2024.1353944
Received: 11 December 2023; Accepted: 04 March 2024; Published: 15 March 2024.
Reviewed by:
Copyright © 2024 Kwon. This is an open-access article distributed under the terms of the Creative Commons Attribution License (CC BY) . The use, distribution or reproduction in other forums is permitted, provided the original author(s) and the copyright owner(s) are credited and that the original publication in this journal is cited, in accordance with accepted academic practice. No use, distribution or reproduction is permitted which does not comply with these terms.
*Correspondence: Sang Hyun Kwon, [email protected]
Disclaimer: All claims expressed in this article are solely those of the authors and do not necessarily represent those of their affiliated organizations, or those of the publisher, the editors and the reviewers. Any product that may be evaluated in this article or claim that may be made by its manufacturer is not guaranteed or endorsed by the publisher.

Enhancing the Effectiveness of Team Science (2015)
Chapter: summary.
Over the past six decades, as scientific and social challenges have become more complex and scientific knowledge and methods have advanced, scientists have increasingly joined with colleagues in collaborative research referred to as team science (see Box S-1 ). Today 90 percent of all science and engineering publications are authored by two or more individuals. The size of authoring teams has expanded as individual scientists, funders, and universities have sought to investigate multifaceted problems by engaging more individuals. Most articles are now written by 6 to 10 individuals from more than one institution.
Team science has led to scientific breakthroughs that would not otherwise have been possible, such as the discovery of the transistor effect, the development of antiretroviral medications to control AIDS, and confirmation of the existence of dark matter. At the same time, conducting research collaboratively can introduce challenges; for example, while the increasing size of team-based research projects brings greater scientific expertise and more advanced instrumentation to a research question, it also increases the time required for communication and coordination of work. If these challenges are not recognized and addressed, then projects may fail to achieve their scientific goals. To provide guidance in addressing these challenges, the National Science Foundation (NSF) requested that the National Research Council (NRC) appoint a committee of experts to conduct a consensus study that would “recommend opportunities to enhance the effectiveness of collaborative research in science teams, research centers, and institutes.” Elsevier also provided funding for the study. The full charge to the Committee on the Science of Team Science is shown in Box S-2 .
BOX S-1 Definitions
- Team science – Scientific collaboration, i.e., research conducted by more than one individual in an interdependent fashion, including research conducted by small teams and larger groups.
- Science teams – Most team science is conducted by 2 to 10 individuals, and we refer to entities of this size as science teams.
- Larger groups – We refer to more than 10 individuals who conduct team science as larger groups. * These larger groups are often composed of many smaller science teams, and a few of them include hundreds or even thousands of scientists. Such very large groups typically possess a differentiated division of labor and an integrated structure to coordinate the smaller science teams; entities of this type are referred to as organizations in the social sciences.
- Team effectiveness (also referred to as team performance ) – A team’s capacity to achieve its goals and objectives. This capacity to achieve goals and objectives leads to improved outcomes for the team members (e.g., team member satisfaction and willingness to remain together), as well as outcomes produced or influenced by the team. In a science team or larger group, the outcomes include new research findings or methods and may also include translational applications of the research.
____________
* Larger groups of scientists sometimes refer to themselves as “science teams.”
To create a framework for this study, the committee first defined the activity of team science and the groups that carry it out. The committee’s definitions reflect prior research that has defined a “team” as two or more individuals with different roles and responsibilities, who interact socially and interdependently within an organizational system to perform tasks and accomplish common goals. Because this prior research has focused on small teams typically including 10 or fewer members, similar in size to most science teams, we refer to a group of 10 or fewer scientists as a “science team.” Recognizing that what is important for successful collaboration changes dramatically as the number of participants grows, we refer to groups of more than 10 scientists as “larger groups of scientists” or simply “larger groups.”
Although team science is growing rapidly, individual scientists continue to make critical contributions and important discoveries, as exemplified by Stephen Hawking’s stream of new insights into the nature of the universe. Public and private funders with finite budgets must make decisions about whether to develop individual investigator or team approaches, and, if a
team approach is selected, the scale and scope of the project. Similarly, individual scientists must make decisions about whether to invest time and energy in collaborative projects or to focus on individual investigations. It is important for scientists and other stakeholders to strategically consider the particular research question, subject matter, and intended scientific and/ or policy goals when determining whether a team science approach is appropriate, and if so, the suitable size, duration, and structure of the project or projects.
BOX S-2 Charge to the Committee on the Science of Team Science
An ad hoc committee will conduct a consensus study on the science of team science to recommend opportunities to enhance the effectiveness of collaborative research in science teams, research centers, and institutes. The Science of Team Science is a new interdisciplinary field that empirically examines the processes by which large and small scientific teams, research centers, and institutes organize, communicate, and conduct research. It is concerned with understanding and managing circumstances that facilitate or hinder the effectiveness of collaborative research, including translational research. This includes understanding how teams connect and collaborate to achieve scientific breakthroughs that would not be attainable by either individual or simply additive efforts.
The committee will consider factors such as team dynamics, team management, and institutional structures and policies that affect large and small science teams. Among the questions the committee will explore are
- How do individual factors (e.g., openness to divergent ideas) influence team dynamics (e.g., cohesion), and how, in turn, do both individual factors and team dynamics influence the effectiveness and productivity of science teams?
- What factors at the team, center, or institute level (e.g., team size, team membership, geographic dispersion) influence the effectiveness of science teams?
- How do different management approaches and leadership styles influence the effectiveness of science teams?
- How do current tenure and promotion policies acknowledge and provide incentives to academic researchers who engage in team science?
- What factors influence the productivity and effectiveness of research organizations that conduct and support team and collaborative science, such as research centers and institutes? How do such organizational factors as human resource policies and practices and cyber infrastructure affect team and collaborative science?
- What types of organizational structures, policies, practices, and resources are needed to promote effective team science in academic institutions, research centers, industry, and other settings?
In order to address these questions, the committee identified, assembled, and reviewed many sources of relevant scientific research. When examining how individual- and team-level factors are related to effectiveness, the committee drew for the most part on two scientific fields that have contributed diverse methodological and conceptual approaches. Together, these fields provide cumulative empirical knowledge to assist scientists, administrators, funding agencies, and policy makers in improving the effectiveness of team science. The first is what has become known as “the science of team science,” an emerging, interdisciplinary field focusing specifically on team science. The second is the large and robust body of social science research on groups and teams in contexts outside of science, such as military teams, industrial research and development teams, production and sales teams, and professional sports teams.
In reviewing the research on teams outside of science, the committee found that teams in these other contexts increasingly incorporate key features that create challenges for team science, as discussed below. This research has identified approaches to enhance team effectiveness that have been translated and extended across contexts (e.g., from aviation teams to health care teams). Therefore, based on the similarities in challenges and processes between teams in science and in other contexts and the history of generalization of team research across contexts, the committee assumes that research on teams in other contexts provides a rich foundation of knowledge that can inform strategies for improving the effectiveness of team science. The research on teams in other contexts has frequently focused on small teams, typically including 10 or fewer individuals, making it more applicable to science teams than to larger groups. However, larger groups of scientists (e.g., participants in a research center) typically are composed of multiple teams, and the research on teams in other contexts is also applicable to these teams.
When examining how organizational- and institutional-level factors are related to team effectiveness, the committee reviewed case studies of geographically distributed teams and larger groups of scientists and other professionals; the business management and leadership literatures; sociology; economics; university case studies; and science policy studies. The committee also drew on the emerging evidence from the science of team science, which focuses on not only the team level, but also the organizational, institutional, and policy levels.
Funding agencies, policy makers, scientists, and leaders of teams and larger groups all need information on how to effectively manage these projects. The first step toward increased effectiveness is to gain understanding of the factors that facilitate or hinder team science and how these factors can be leveraged to improve the management, administration, and funding of team science. Although research is emerging from the science of team sci-
ence, from the research on teams, and from many other fields, this research is fragmented. Team science practitioners may have difficulty assembling, understanding, and applying the insights scattered across different research fields. This report integrates and translates the relevant research to support 13 conclusions and 9 recommendations and to identify areas requiring further research, as discussed below. Table S-1 , at the end of this Summary, repeats the recommendations, specifying the individuals or organizations (e.g., team science leaders, universities) who should take action, the actions, and the desired outcomes.
KEY FEATURES THAT CREATE CHALLENGES FOR TEAM SCIENCE
Based on its review of the research evidence, information from team science practitioners, and its own expert judgment, the committee identified seven features that can create challenges for team science. Each feature represents one end of a continuous dimension. For example, large size is one end of the team or group size dimension. Science teams and larger groups often need to incorporate one or more of these features to address their particular research goals, but the features also pose challenges that are important to carefully manage. The committee returns to these seven features throughout this report in interpreting the implications of the research.
- High diversity of membership. Addressing complex scientific problems can require contributions from different disciplines, communities, or professions. Science teams or larger groups sometimes include community or industry stakeholders to facilitate translation of the research into practical applications (e.g., doctors or product development specialists). In addition, reflecting the changing demographics of the U.S. population and the globalization of the scientific workforce, team or group members may be diverse in age, gender, culture, religion, or ethnicity. Diverse team members may lack a common vocabulary, posing a challenge to effectively communicating about the research goals and deciding how to work together to accomplish scientific tasks.
- Deep knowledge integration. All science teams and larger groups integrate information to some extent as the members apply their unique knowledge and skills to the shared research problem. This challenge increases in interdisciplinary or transdisciplinary teams. Interdisciplinary research integrates the data, tools, perspectives, and theories of two or more disciplines to advance understanding or solve problems. Transdisciplinary research aims to deeply integrate and also transcend disciplinary approaches to generate
fundamentally new conceptual frameworks, theories, models, and applications. It can be difficult for the members of such teams or larger groups to share and build on each other’s knowledge across the boundaries of their respective disciplines.
- Large size. Science and engineering teams and larger groups, as reflected in publications, have consistently expanded in size over the past 60 years. Larger size can enhance productivity by distributing the work across more individuals, but it also magnifies the burden of communicating and coordinating tasks among a larger number of individuals. Scientists participating in larger groups have fewer opportunities than those working in smaller teams to meet and work with other group members face-to-face in ways that build trust and shared understanding of project goals and the roles of other group members.
- Goal misalignment with other teams. Large groups of scientists, such as research centers and institutes, typically include multiple science teams engaged in research projects relevant to the higher-level research or translational goals of the center or institute. Each individual team brings valuable insights, methods, and perspectives and may have its own distinct goals. If the goals of these teams are not aligned, then this can generate conflict, requiring careful management
- Permeable boundaries. The boundaries of science teams and larger groups are often permeable, reflecting changes in the project goals over time. The membership of a group or team may change as the project moves from one phase, requiring a certain type of expertise, to another that may require different expertise. Although these changes have the benefit of matching expertise to scientific or translational problems as they arise, they can also create challenges for effective team or group interaction.
- Geographic dispersion. Most science teams and larger groups are geographically dispersed, with members located across multiple universities or research institutions. Although crossing institutional boundaries can bring needed expertise, scientific instrumentation, datasets, or other valuable resources to a science team or larger group, it also requires greater reliance on electronic modes of communication, with attendant challenges. In addition, the team or larger group may find it difficult to coordinate work across institutions with varying work styles, time zones, and cultural expectations about scientific work.
- High task interdependence. One of the defining features of a team is that the members are dependent on each other to accomplish a
shared task. All team science projects aim to tap the benefits of interdependent, collaborative research, yet designing and conducting interdependent tasks that draw on and integrate the unique talents of the individual team or larger group members to accomplish shared goals can be challenging. Greater task interdependence among team or group members can lead to more opportunities for conflict, and when geographically dispersed members must perform highly interdependent tasks, greater coordination and communication efforts may be required.
Each science team or larger group is unique in the extent to which it is characterized by one or more of these features. As a given team or group incorporates more of these key features—for instance, high diversity of membership and geographic dispersion—so do the accompanying challenges and the attendant need to understand and carefully manage them. As noted above, it is important to strategically consider the particular research question, subject matter, and intended goals when determining the approach, suitable size, and other features of a research project.
IMPROVING TEAM AND GROUP EFFECTIVENESS
Research on teams in non-science contexts has identified strategies for improving effectiveness that can be translated and applied to help science teams and larger groups navigate the challenges involved in team science.
C ONCLUSION . A strong body of research conducted over several decades has demonstrated that team processes (e.g., shared understanding of team goals and member roles, conflict) are related to team effectiveness. Actions and interventions that foster positive team processes offer the most promising route to enhance team effectiveness; they target three aspects of a team: team composition (assembling the right individuals), team professional development, and team leadership.
Team Composition
Assembling and composing the team provides the raw building material for an effective team and therefore is a critical step requiring careful management, but it is only the first step.
C ONCLUSION . Research to date in non-science contexts has found that team composition influences team effectiveness, and this relationship
depends on the complexity of the task, the degree of interdependence among team members, and how long the team is together. Task-relevant diversity is critical and has a positive influence on team effectiveness.
C ONCLUSION . Task analytic methods developed in non-science contexts and research networking tools developed in science contexts allow practitioners to consider team composition systematically.
R ECOMMENDATION 1: Team science leaders and others involved in assembling science teams and larger groups should consider making use of task analytic methods (e.g., task analysis, cognitive modeling, job analysis, cognitive work analysis) and tools that help identify the knowledge, skills, and attitudes required for effective performance of the project so that task-related diversity among team or group members can best match project needs. They should also consider applying tools such as research networking systems designed to facilitate assembly of science teams and partner with researchers to evaluate and refine these tools and task analytic methods.
Team Professional Development
Once a science team or larger group has been assembled, it faces the challenge of integrating the members’ knowledge to achieve its scientific goals. Knowledge integration, along with shared understanding of research goals and member roles, can be facilitated by formal professional development programs (referred to in the research literature as training programs).
C ONCLUSION . Research in contexts outside of science has demonstrated that several types of team professional development interventions (e.g., knowledge development training to increase sharing of individual knowledge and improve problem solving) improve team processes and outcomes.
R ECOMMENDATION 2: Team-training researchers, universities, and science team leaders should partner to translate, extend, and evaluate the promising training strategies, shown to improve the effectiveness of teams in other contexts, to create professional development opportunities for science teams.
Although research has demonstrated that training for current team members can increase team effectiveness, educational programs designed to prepare students for future team science have only recently emerged and have not yet been systematically evaluated.
C ONCLUSION . Colleges and universities are developing cross-disciplinary programs designed to prepare students for team science, but little empirical research is available on the extent to which participants in such programs develop the competencies they target. Research to date has not shown whether the acquisition of the targeted competencies contributes to team science effectiveness.
Leadership for Team Science
Currently, most leaders of science teams and larger groups are appointed to their positions based solely on scientific expertise and lack formal leadership training. At the same time, an extensive body of research on organizational and team leadership has illuminated leadership styles and behaviors that foster positive interpersonal processes, thereby enhancing effectiveness in teams and larger groups. These effective leadership styles and behaviors can be acquired.
C ONCLUSION . Fifty years of research on team and organizational leadership in contexts other than science provide a robust foundation of evidence to guide professional development for leaders of science teams and larger groups.
R ECOMMENDATION 3: Leadership researchers, universities, and leaders of team science projects should partner to translate and extend the leadership literature to create and evaluate science leadership development opportunities for team science leaders and funding agency program officers.
Supporting Virtual Collaboration
As science attempts to answer bigger and bigger questions, it is increasingly likely that the people participating in research projects reside in different locations, institutions, and even countries. This geographic dispersion can lead to challenges, particularly with communication and coordination. Addressing the special challenges such groups and teams encounter requires effective leadership and technology.
C ONCLUSION . Research on geographically dispersed teams and larger groups of scientists and other professionals has found that communicating progress, obstacles, and open issues and developing trust are more challenging relative to face-to-face teams and larger groups. These
limitations of virtual collaboration may not be obvious to members and leaders of the team or group.
R ECOMMENDATION 4: Leaders of geographically dispersed science teams and larger groups should provide activities shown by research to help all participants develop shared knowledge (e.g., a common vocabulary and work style). These activities should include team professional development opportunities that promote knowledge sharing (see Recommendation #2 above). Leaders should also consider the feasibility of assigning some tasks to semi-independent units at each location to reduce the burden of constant electronic communication.
C ONCLUSION . Technology for virtual collaboration often is designed without a true understanding of users’ needs and limitations and even when a suite of appropriate technologies is available, users often do not recognize and use its full capabilities. These related problems may thus impede such collaboration.
R ECOMMENDATION 5: When selecting technologies to support virtual science teams or larger groups, leaders should carefully evaluate the needs of the project, and the ability of the individual participants to embrace new technologies. Organizations should promote human-centered collaboration technologies, provide technical staff, and encourage use of the technologies by providing ongoing training and technology support.
Organizational Supports for Team Science
Science teams and larger groups are often housed within universities. In these complex organizations, faculty members’ decisions about whether and when to participate in team science are influenced by various contexts and cultures including the department, the college, the institution as a whole, and external groups, such as disciplinary societies. Formal rewards and incentive structures, reflecting these various cultures, currently tend to focus on individual research contributions. Some universities have recently sought to promote interdisciplinary team science by, for example, merging disciplinary departments to create interdisciplinary research centers or schools, providing seed grants, and forging partnerships with industry. However, little is known about the impact of these efforts, while the lack of recognition and rewards for team science can deter faculty members from joining science teams or larger groups.
C ONCLUSION . Various research universities have undertaken new efforts to promote interdisciplinary team science, such as merging disciplinary departments to create interdisciplinary research centers or schools. However, the impact of these initiatives on the amount and quality of team science research remains to be systematically evaluated.
C ONCLUSION . University policies for promotion and tenure review typically do not provide comprehensive, clearly articulated criteria for evaluating individual contributions to team-based research. The extent to which researchers are rewarded for team-based research varies widely across and within universities. Where team-based research is not rewarded, young faculty may be discouraged from joining those projects.
In a few isolated cases, universities have developed new policies for assessing individual contributions to team science. At the same time, research has begun to characterize the various types of individual contributions and develop software systems that would identify each individual’s role during the process of submitting and publishing an article. This work can inform new efforts by universities and disciplinary associations.
R ECOMMENDATION 6: Universities and disciplinary associations should proactively develop and evaluate broad principles and more specific criteria for allocating credit for team-based work to assist promotion and tenure committees in reviewing candidates.
Funding for Team Science
C ONCLUSION . Public and private funders are in the position to foster a culture within the scientific community that supports those who want to undertake team science, not only through funding, but also through white papers, training workshops, and other approaches.
R ECOMMENDATION 7: Funders should work with the scientific community to encourage the development and implementation of new collaborative models, such as research networks and consortia; new team science incentives, such as academic rewards for team-based research (see Recommendation #6); and resources (e.g., online repositories of information on improving the effectiveness of team science and training modules).
C ONCLUSION . Funding agencies are inconsistent in balancing their focus on scientific merit with their consideration of how teams and larger groups are going to execute the work (collaborative merit). The
Funding Opportunity Announcements they use to solicit team science proposals often include vague language about the type of collaboration and the level of knowledge integration they seek in proposed research.
Currently, proposals for team science research grants do not address how the participating scientists will collaborate. Research has shown that engaging team members in explicit discussions of how to coordinate and integrate their work enhances effectiveness, as does the development of team charters that outline team directions, roles, and processes. In addition, research has found that large, multi-institutional groups of scientists often benefit from establishing formal contracts outlining roles and assignments. Collaboration plans build on both team charter and contract concepts, promising to enhance the effectiveness of team science.
R ECOMMENDATION 8: Funders should require proposals for team-based research to present collaboration plans and provide guidance to scientists for the inclusion of these plans in their proposals, as well as guidance and criteria for reviewers’ evaluation of these plans. Funders should also require authors of proposals for interdisciplinary or transdisciplinary research projects to specify how they will integrate disciplinary perspectives and methods throughout the life of the research project.
ADVANCING RESEARCH ON THE EFFECTIVENESS OF TEAM SCIENCE
The committee’s review of the research related to the study charge identified several areas in which further research is needed to enhance understanding of team science and improve its effectiveness.
Continued research and evaluation will be needed to refine and enhance the actions, interventions, and policies recommended in this report. At the same time, research is needed to enhance basic understanding of team science processes as the foundation for developing new interventions. Funders of scientific research, policy makers, and the scientific community need appropriate criteria for evaluating the potential (ex-ante) and achieved (ex-post) outcomes of team science. In addition, funders and policy makers would benefit from more rigorous evaluations incorporating experimental or quasi-experimental methods to generate stronger evidence that team-based research approaches increase research productivity beyond what would have been accomplished by the individual scientists working alone or as members of a different team or group. An essential first step toward meeting these goals is to increase researchers’ access to practicing scientists to study their interactions and innovations. In sum, advancing the research
on the effectiveness of science teams and larger groups will require funding, as well as the dedication of research organizations, team science leaders, and the scientific community as a whole.
C ONCLUSION . Targeted research is needed to evaluate and refine the tools, interventions, and policies recommended above, along with more basic research, to guide continued improvement in the effectiveness of team science. However, few if any funding programs support research on the effectiveness of science teams and larger groups.
R ECOMMENDATION 9: Public and private funders should support research on team science effectiveness through funding. As critical first steps, they should support ongoing evaluation and refinement of the interventions and policies recommended above and research on the role of scientific organizations (e.g., research centers, networks) in supporting science teams and larger groups. They should also collaborate with universities and the scientific community to facilitate researchers’ access to key team science personnel and datasets.
Promising new research methods and approaches can be applied to implement this recommendation. Complex adaptive systems theory offers a route to understand how behaviors, actions, and reactions at one level of a team science system (e.g., the individual level) affect actions at other system levels (e.g., the team level) and the emergent behavior of the system as a whole. To study team and group dynamics, members can be equipped with small electronic sensor badges that record data on their interactions. Similarly, electronic communication data, such as emails and texts, can be recorded and analyzed. These new forms of data can be creatively combined with publication data to examine the relationship between team or group processes and outcomes. Such approaches will facilitate further research to deepen understanding of team science and enhance its effectiveness.
TABLE S-1 Recommended Actions and Desired Outcomes
The past half-century has witnessed a dramatic increase in the scale and complexity of scientific research. The growing scale of science has been accompanied by a shift toward collaborative research, referred to as "team science." Scientific research is increasingly conducted by small teams and larger groups rather than individual investigators, but the challenges of collaboration can slow these teams' progress in achieving their scientific goals. How does a team-based approach work, and how can universities and research institutions support teams?
Enhancing the Effectiveness of Team Science synthesizes and integrates the available research to provide guidance on assembling the science team; leadership, education and professional development for science teams and groups. It also examines institutional and organizational structures and policies to support science teams and identifies areas where further research is needed to help science teams and groups achieve their scientific and translational goals. This report offers major public policy recommendations for science research agencies and policymakers, as well as recommendations for individual scientists, disciplinary associations, and research universities. Enhancing the Effectiveness of Team Science will be of interest to university research administrators, team science leaders, science faculty, and graduate and postdoctoral students.
Welcome to OpenBook!
You're looking at OpenBook, NAP.edu's online reading room since 1999. Based on feedback from you, our users, we've made some improvements that make it easier than ever to read thousands of publications on our website.
Do you want to take a quick tour of the OpenBook's features?
Show this book's table of contents , where you can jump to any chapter by name.
...or use these buttons to go back to the previous chapter or skip to the next one.
Jump up to the previous page or down to the next one. Also, you can type in a page number and press Enter to go directly to that page in the book.
Switch between the Original Pages , where you can read the report as it appeared in print, and Text Pages for the web version, where you can highlight and search the text.
To search the entire text of this book, type in your search term here and press Enter .
Share a link to this book page on your preferred social network or via email.
View our suggested citation for this chapter.
Ready to take your reading offline? Click here to buy this book in print or download it as a free PDF, if available.
Get Email Updates
Do you enjoy reading reports from the Academies online for free ? Sign up for email notifications and we'll let you know about new publications in your areas of interest when they're released.
To read this content please select one of the options below:
Please note you do not have access to teaching notes, how do we measure the effectiveness of team building is it good enough team management systems ‐ a case study.
Journal of Management Development
ISSN : 0262-1711
Article publication date: 1 March 1997
Looks at the use of the Team Management Index (TMI) as a team building intervention in a programme of organizational development (OD). Attempts to assess the instrument’s effectiveness using a variety of measures (including the taxonomy of De Meuse and Liebowitz, 1981). In so doing, raises wider methodological and epistemological issues as to the whole nature of data collection, validity and proof in measuring the effectiveness of OD interventions. Discovers that, according to the measurement criteria, set out by De Meuse and Liebowitz, the TMI can be considered to be an effective OD instrument. However, finds that these measurement techniques are “blunt” and, by their very nature, lacking in academic rigour. Argues, therefore, that all levels of data collection and evidence gathering can never constitute 100 per cent proof of a causal link between OD interventions and resultant changes in the organization. Concludes that what will be deemed to count as adequate evidence or proof of an intervention’s effectiveness ultimately will be a personal choice; that in concentrating on comparing before and after measures of a team’s effectiveness theorists have ignored the change process which is taking place as a team begins to become effective, and have treated teams at the end of a team building intervention as if they were finished products; and finally that research time should be devoted to studying the process of change which a team undergoes during its development (of which team building is just the beginning) in order to highlight the ways in which an organization could nurture, support and facilitate this process to ensure the effective development of its work teams.
- Effectiveness
- Organizational change
- Organizational development
- Team building
Rushmer, R.K. (1997), "How do we measure the effectiveness of team building? Is it good enough? Team Management Systems ‐ a case study", Journal of Management Development , Vol. 16 No. 2, pp. 93-110. https://doi.org/10.1108/02621719710164274
Copyright © 1997, MCB UP Limited
Related articles
We’re listening — tell us what you think, something didn’t work….
Report bugs here
All feedback is valuable
Please share your general feedback
Join us on our journey
Platform update page.
Visit emeraldpublishing.com/platformupdate to discover the latest news and updates
Questions & More Information
Answers to the most commonly asked questions here
- SUGGESTED TOPICS
- The Magazine
- Newsletters
- Managing Yourself
- Managing Teams
- Work-life Balance
- The Big Idea
- Data & Visuals
- Reading Lists
- Case Selections
- HBR Learning
- Topic Feeds
- Account Settings
- Email Preferences
Stop Wasting Money on Team Building
- Carlos Valdes-Dapena

There are better ways to learn collaboration.
Many companies, when they decide to invest in team building, decide to do offsite events like bowling nights or ropes courses. Some spend thousands on special events, hoping to improve collaboration. These efforts often fail, so Mars Inc. took a different approach. HR leaders decided to interview and survey 125 teams. They used this data to develop a team-building approach that focused on the work itself. In an intensive two-day workshop, they asked a pilot group to discuss two questions: Why is their collaboration essential to achieving their business results? And second: What work, which specific tasks, would require collaboration to deliver those results? The results from these discussions were so good that Mars rolled out this approach to the whole company.
Most corporate team building is a waste of time and money. I say this based on my 25+ years of research and practice in the field of team effectiveness. Seventeen of those years were with Mars Inc., a family-owned $35 billion global business with a commitment to collaboration.
- CV Carlos Valdes-Dapena is the CEO of Corporate Collaboration Resources and the author of Lessons from Mars: How One Global Company Cracked the Code on High Performance Collaboration and Teamwork .
Partner Center

VIDEO
COMMENTS
This research reports the results of a comprehensive investigation into the effectiveness of team building. The article serves to update and extend Salas, Rozell, Mullen, and Driskell's (1999) team-building meta-analysis by assessing a larger database and examining a broader set of outcomes.
The chapter provides an explanation of "teams" and "team building", and input-throughput-output model of team effectiveness to provide a context for examining team building interventions. Three previous reviews are presented, which examined team building research through 1980. The chapter also reviews the empirical research on team building ...
TEAM BUILDING RESEARCH SINCE 1980 We conducted a literature search of the team building research published in the 1980s. A computer search was performed using the Psychologicul Abstracts, ERIC, ABI-Inform and NTIS databases. ... * In general, team building interventions were fairly effective. Team building appears to have a positive effect on ...
More than half a century of research on team effectiveness (Kozlowski and Ilgen, 2006) provides a foundation for identifying team process factors that contribute to team effectiveness, as well as actions and interventions that can be used to shape the quality of those processes. As noted in Chapter 1, this evidence base consists primarily of studies focusing on teams in contexts outside of ...
This research reports the results of a comprehensive investigation into the effectiveness of team building. The article serves to update and extend Salas, Rozell, Mullen, and Driskell's (1999 ...
This involves 'developing' or 'building' the team; otherwise known as team building. Team building has been described as "a method of helping the group to (a) increase effectiveness, (b) satisfy the needs of its members, or (c) improve work conditions" [ 3, p. 13-14 ]. Based upon the work of Carron and co-workers [ 4•, 5 ], team ...
examines team building and its influence on team effectiveness / provide an explanation of what we mean by "teams" and "team building" / describe an input-throughput-output model of team effectiveness to provide a context for examining team building interventions / highlight three previous reviews that examined team building research through 1980 / review the empirical research on team ...
An empirical analysis of team-building research. Group & Organization Studies, 6 (3): 357-378. [Google Scholar] DeRue DS, Hollenbeck JR, Johnson MD, Ilgen DR, & Jundt DK 2008. How different team downsizing approaches influence team-level adaptation and performance. Academy of Management Journal, 51 (1): 182-196. [Google Scholar] Devine DJ 1999.
According to Castka et al. (2001), organizational influence, Literature provides that the effectiveness of team building is inconsistent, however, in most cases, it creates positive results ...
team effectiveness as a dynamic process. We next review the research base to identify critical team processes and emergent states that contribute to team effectiveness. Having established that research foundation, we then consider factors that can in-fluence, shape, and create appropriate team processes. Thus, our basic questions in this ...
team resources explain effective team respon-ses to adverse events at work. Although the interest in studying team resi-lience has grown in recent years, research on team resilience suffers from inconsistent con-ceptual and methodological approaches. We see two main conceptual concerns: (a) the dif-fering conceptualizations of team resilience in
This difficulty arises from the complexities associated with randomly assigning teams in research focused on sports team dynamics. 3.3 Overall analysis 3.3.1 Overall effect size. The meta-analysis results, ... In any case, to have an effective team-building intervention, it is necessary to implement the intervention for a long enough period. ...
In this context, we evaluate and analyze the effectiveness of the function of human resource team building by looking at three key factors: Task Oriented Roles Factor, Relationship Oriented Roles ...
Overview of the Research on Team Effectiveness. This chapter summarizes the research literature on team effectiveness, highlighting findings on the key features that create challenges for team science outlined in Chapter 1. Based on its review of the literature (e.g., Marks, Mathieu, and Zaccaro, 2001; Kozlowski and Ilgen, 2006; Salas, Goodwin ...
Enhancing the Effectiveness of Team Science synthesizes and integrates the available research to provide guidance on assembling the science team; leadership, education and professional development for science teams and groups. It also examines institutional and organizational structures and policies to support science teams and identifies areas ...
The first step toward increased effectiveness is to gain understanding of the factors that facilitate or hinder team science and how these factors can be leveraged to improve the management, administration, and funding of team science. Although research is emerging from the science of team sci-. Page 5.
The science of teamwork has been extensively studied, 1 and with good reason. Successful teams improve business outcomes, including revenue and performance. 2 Many organizations are intentionally fostering a collaborative team-based culture, 2 and feeling like a part of a team is a primary driver of employee engagement. 3 Prior to the pandemic, organizational shifts had resulted in teams that ...
Looks at the use of the Team Management Index (TMI) as a team building intervention in a programme of organizational development (OD). Attempts to assess the instrument's effectiveness using a variety of measures (including the taxonomy of De Meuse and Liebowitz, 1981).
team building. Effectiveness of team building Much research effort has been directed at measuring the effectiveness of team-building interventions. A large number of descriptive, correlational, causal, and meta-analytical studies have been published on this subject (Salas et al., 1999; Klein et al., 2009; Martin et al., 2009).
(Shuffler et al., 2011) Main difference between team training and team building (Salas, 2015) Key elements of team training (Klein et al., 2009) Team building effectiveness
(Clearinghouse) conducted a brief, rapid review of the literature on the topic of building team effectiveness . Research examining these topics were identified by searching peer reviewed journal articles limited to publications between 2000 and 2019. Search terms included building effective teams, team effectiveness, team building, team and
Team-building Competencies, Personal Effectiveness and Job Satisfaction: The Mediating Effect of Transformational Leadership and Technology February 2018 Management and Labour Studies 43(1-2):109-122
Most corporate team building is a waste of time and money. I say this based on my 25+ years of research and practice in the field of team effectiveness. Seventeen of those years were with Mars Inc ...
Abstract. Abstrak Team building intervention is one form of intervention that is very popular in the world of organizational development practice. But unfortunately, empirically reported results ...