

Essay on Internet Privacy
Students are often asked to write an essay on Internet Privacy in their schools and colleges. And if you’re also looking for the same, we have created 100-word, 250-word, and 500-word essays on the topic.
Let’s take a look…
100 Words Essay on Internet Privacy
Understanding internet privacy.
Internet privacy is about protecting your personal data online. It’s important because when you use the internet, you share information that others could misuse.
Why is Internet Privacy Important?
Internet privacy is crucial to protect your identity and personal information. Without it, strangers could access your data, leading to potential harm.
How to Maintain Internet Privacy?
You can maintain internet privacy by using strong passwords, enabling privacy settings on social media, and avoiding sharing sensitive information online. Always remember, your online safety is in your hands.
250 Words Essay on Internet Privacy
Introduction to internet privacy.
Internet privacy, often synonymous with online privacy, is a subset of data privacy focusing on the protection of personal information in the digital realm. As the internet becomes increasingly integral to our daily lives, privacy issues have surged to the forefront of societal discourse.
The Importance of Internet Privacy
Threats to internet privacy.
Threats to internet privacy are manifold. They include cybercriminal activities, surveillance by government agencies, data mining by corporations, and even seemingly innocuous social media platforms that collect and utilize user data.
Internet Privacy: A Human Right?
Many argue that internet privacy is a fundamental human right. This perspective highlights the need for stringent laws and policies to protect individuals from intrusive surveillance and unauthorized data collection.
The Role of Individuals in Protecting Privacy
While legislation plays a vital role, individuals must also take proactive steps to safeguard their online privacy. This can include using encrypted communication, regularly updating software, and being mindful of the information shared online.
Internet privacy is a complex and critical issue in the digital age. The collective efforts of individuals, corporations, and governments are necessary to ensure the protection of personal information in the online sphere. As we continue to navigate this interconnected world, the importance of internet privacy will only increase.
500 Words Essay on Internet Privacy
Internet privacy is a subcategory of data privacy, focusing on the protection of user information shared online. It is a significant concern in the digital age, where data is considered the new oil. Internet privacy concerns the safeguarding of personal, financial, and data information of a private individual or organization.
Despite its importance, internet privacy is under constant threat. Cybercriminals often exploit security breaches to steal sensitive data. Also, many online platforms and services thrive on data collection, often without clear consent from users. Governments, too, may infringe upon internet privacy for surveillance and security purposes.
The Role of Legislation in Internet Privacy
Legislation plays a crucial role in protecting internet privacy. Laws like the General Data Protection Regulation (GDPR) in the European Union and the California Consumer Privacy Act (CCPA) in the United States are examples of attempts to regulate data collection and usage. However, enforcing these laws across borders is challenging, and loopholes often exist that allow for continued privacy infringements.
Individual Responsibility and Internet Privacy
Conclusion: the future of internet privacy.
The future of internet privacy is uncertain. On one hand, advancements in technology, such as blockchain and quantum computing, could potentially enhance data security. On the other hand, the increasing digitization of our lives threatens to erode privacy further. The challenge lies in finding a balance between the benefits of the digital age and the preservation of privacy. As we move forward, the discourse on internet privacy will remain a pivotal aspect of our digital lives.
That’s it! I hope the essay helped you.
Happy studying!
Leave a Reply Cancel reply
Your email address will not be published. Required fields are marked *

Home — Essay Samples — Law, Crime & Punishment — Privacy & Security — Internet Privacy
Essays on Internet Privacy
The importance of writing an essay on internet privacy.
Writing an essay on internet privacy is crucial in today's digital age. With the increasing use of the internet for communication, social networking, and online transactions, the issue of privacy has become more important than ever. It is essential to educate people about the potential risks and threats to their privacy online and to advocate for stronger privacy protections.
Internet privacy is a fundamental human right, and writing an essay on this topic can help raise awareness about the importance of protecting personal information online. It can also encourage individuals to take steps to safeguard their privacy and advocate for laws and regulations that protect their rights.
When writing an essay on internet privacy, it is important to research and gather relevant information from credible sources. This may include academic journals, government reports, and reputable news outlets. It is also important to consider different perspectives and arguments on the topic to provide a well-rounded and comprehensive analysis.
Additionally, it is crucial to clearly articulate the potential risks and threats to internet privacy, such as data breaches, online surveillance, and identity theft. Providing real-life examples and case studies can help illustrate the impact of these issues on individuals and society as a whole.
Furthermore, it is essential to offer practical tips and solutions for protecting internet privacy, such as using strong passwords, enabling two-factor authentication, and being cautious about sharing personal information online. By empowering individuals with the knowledge and tools to protect their privacy, the essay can have a positive impact on the reader and the broader community.
Writing an essay on internet privacy is important for raising awareness, advocating for stronger privacy protections, and empowering individuals to safeguard their personal information online. By conducting thorough research, considering different perspectives, and providing practical solutions, the essay can help contribute to a more privacy-conscious and informed society.
- The importance of internet privacy in the digital age
In today's technology-driven world, internet privacy has become a major concern for individuals and businesses alike. With the increasing amount of personal information being shared online, it is important to understand the importance of protecting one's privacy on the internet. This essay will delve into the reasons why internet privacy is important and the potential consequences of not safeguarding one's online information.
- The evolution of internet privacy laws
Over the years, there have been significant developments in internet privacy laws as governments and regulatory bodies have recognized the need to protect individuals' personal information online. This essay will explore the evolution of internet privacy laws, including the landmark legislation and regulations that have been enacted to safeguard online privacy rights.
- The impact of social media on internet privacy
Social media has revolutionized the way we communicate and share information, but it has also raised concerns about internet privacy. This essay will examine the impact of social media on internet privacy, including the risks associated with sharing personal information on social networking platforms and the measures individuals can take to protect their privacy online.
- The role of technology in internet privacy
Advancements in technology have both enhanced and compromised internet privacy. This essay will discuss the role of technology in internet privacy, including the development of encryption tools, the rise of data breaches, and the potential implications of emerging technologies on online privacy rights.
- The ethical considerations of internet privacy
As individuals and businesses navigate the digital landscape, ethical considerations surrounding internet privacy have come to the forefront. This essay will explore the ethical implications of internet privacy, including the ethical responsibilities of organizations to protect user data and the ethical dilemmas individuals face when sharing personal information online.
- The impact of data breaches on internet privacy
Data breaches have become a prevalent threat to internet privacy, as cybercriminals continue to target organizations to access sensitive personal information. This essay will examine the impact of data breaches on internet privacy, including the potential consequences for individuals and businesses and the measures that can be taken to mitigate the risks of data breaches.
- The future of internet privacy
As technology continues to evolve, the future of internet privacy remains uncertain. This essay will speculate on the future of internet privacy, including the potential challenges and opportunities that lie ahead as individuals and organizations strive to protect their online privacy rights.
- The intersection of internet privacy and cybersecurity
Internet privacy and cybersecurity are closely intertwined, as both are essential for protecting personal information online. This essay will explore the intersection of internet privacy and cybersecurity, including the measures that can be taken to safeguard online privacy and the role of cybersecurity in mitigating privacy risks.
- The global perspective on internet privacy
Internet privacy is a universal concern, and different countries have varying approaches to protecting online privacy rights. This essay will provide a global perspective on internet privacy, including the international laws and regulations that govern internet privacy and the challenges of ensuring privacy rights in a global digital landscape.
- The responsibility of individuals in protecting their internet privacy
Ultimately, individuals play a crucial role in protecting their internet privacy. This essay will discuss the responsibility of individuals in safeguarding their online privacy, including the best practices for maintaining internet privacy and the potential consequences of neglecting online privacy protection.
The Importance of Internet Privacy and Net Neutrality to Internet Users in The Modern Era
Why internet privacy should be protected, made-to-order essay as fast as you need it.
Each essay is customized to cater to your unique preferences
+ experts online
The Importance of Internet Privacy
The importance of staying safe on social media, cyber crime and internet privacy, the crucial role of internet privacy for a user, let us write you an essay from scratch.
- 450+ experts on 30 subjects ready to help
- Custom essay delivered in as few as 3 hours
A Privacy Aspect to The Internet of Things
Identifying threats and vulnerabilities in home internet connection, human rights on the digital era, brief history of cyber security, get a personalized essay in under 3 hours.
Expert-written essays crafted with your exact needs in mind
Privacy Issues in a Smart City
The concepts and outcomes of net neutrality, the singaporean government's ideologically conservative view on the internet, enhancing online security: qr code-based authentication for banking, secure online auction system, iot: addressing security challenges and possible solutions, analysis of the benefits of internet censorship, internet censorship as a modern way to protect the youth, internet censorship as the new 'norm', internet censorship: beneficial, but restrictive, personal outlook on the issue of internet censorship, useful alternatives for internet censorship, wikipedia censorship: the advantage for governments authorities, the data protection: how your personal information is used by organisations, businesses or the government, protect your data. then hope for a tech revolution, how technological advancement is going to affect us, should the internet be regulated: exploring possibilites to follow, should the internet be regulated: is it about net neutrality, should there be a legal age limit for social media, the internet: a challenge to copyright protection, relevant topics.
- Serial Killer
- War on Drugs
- Animal Cruelty
- Juvenile Delinquency
By clicking “Check Writers’ Offers”, you agree to our terms of service and privacy policy . We’ll occasionally send you promo and account related email
No need to pay just yet!
We use cookies to personalyze your web-site experience. By continuing we’ll assume you board with our cookie policy .
- Instructions Followed To The Letter
- Deadlines Met At Every Stage
- Unique And Plagiarism Free
Numbers, Facts and Trends Shaping Your World
Read our research on:
Full Topic List
Regions & Countries
- Publications
- Our Methods
- Short Reads
- Tools & Resources
Read Our Research On:
How Americans View Data Privacy
1. views of data privacy risks, personal data and digital privacy laws, table of contents.
- Role of social media, tech companies and government regulation
- Americans’ day-to-day experiences with online privacy
- Personal data and information
- Feelings of concern, confusion and a lack of control over one’s data
- Privacy laws and regulation
- Americans largely favor more regulation to protect personal information
- Trust in social media executives
- Children’s online privacy: Concerns and responsibility
- Law enforcement and surveillance
- AI and data collection
- Trust in companies that use AI
- How people approach privacy policies
- How people are protecting their digital privacy
- How Americans handle their passwords
- Data breaches and hacks
- Identifying the most and least knowledgeable, confident and concerned
- Knowledge and privacy choices
- Confidence and privacy choices
- Concern and privacy choices
- The case of privacy policies
- Acknowledgments
- The American Trends Panel survey methodology
- Appendix A: Law enforcement’s use of technology in investigations
- Appendix B: Privacy outcomes by knowledge, confidence and concern
- Appendix C: Confident and independent use of digital devices, by age and education
Online privacy is complex, encompassing debates over law enforcement’s data access, government regulation and what information companies can collect. This chapter examines Americans’ perspectives on these issues and highlights how views vary across different groups, particularly by education and age.
When managing their privacy online, most Americans say they trust themselves to make the right decisions about their personal information (78%), and a majority are skeptical that anything they do will make a difference (61%).
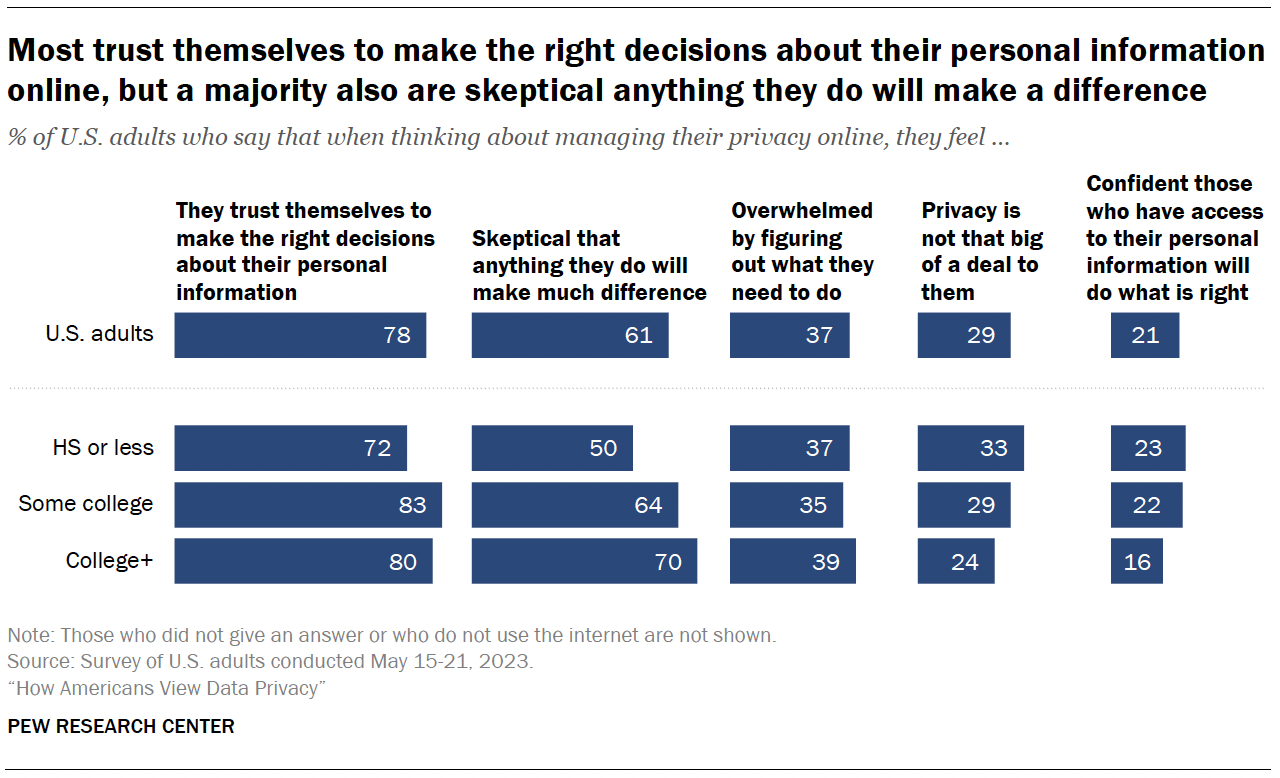
Far fewer mention being overwhelmed by figuring out what they need to do (37%) or say privacy is not that big of a deal to them (29%).
Another 21% are confident that those with access to their personal information will do what is right.
Education differences
- 81% of those with at least some college experience say they trust themselves to make the right decisions about their personal information online, compared with 72% of those with a high school diploma or less.
- 67% of those with at least some college are skeptical that anything they do to manage their online privacy will make a difference, compared with half of those with a high school diploma or less formal education.
On the other hand, those with a high school education or less are more likely than those with some college experience or more to say that privacy isn’t that big of a deal to them and that they are confident that those who have access to their personal information will do the right thing.
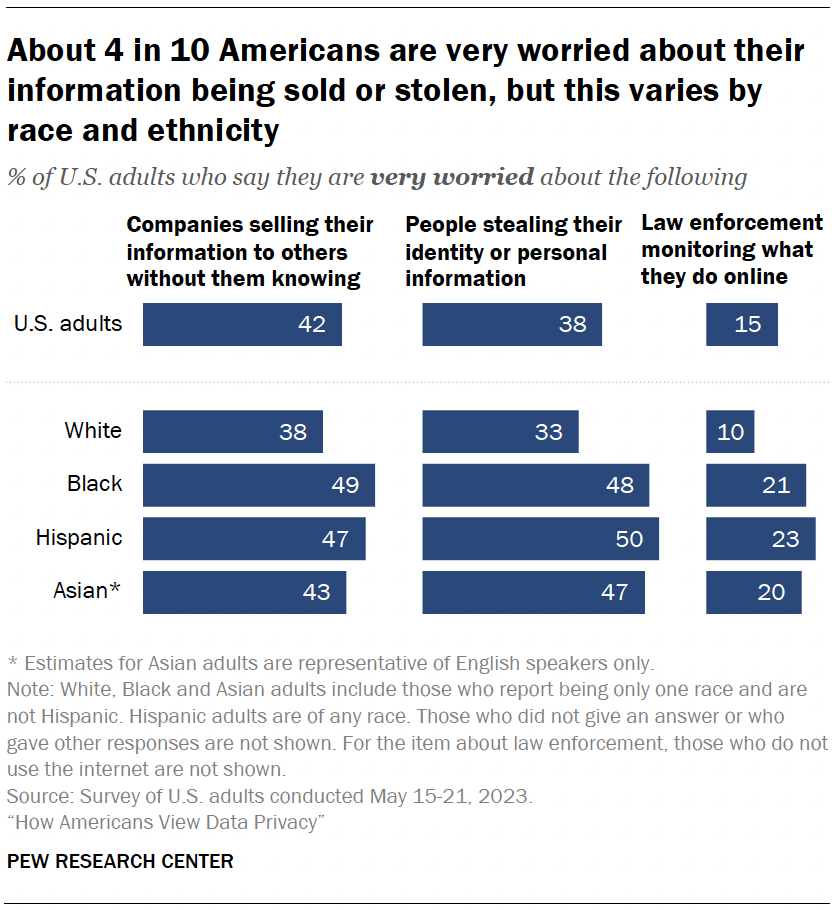
The survey also explores the concerns people have about data collection and security – specifically, how they feel about three scenarios around companies, law enforcement and identity theft.
Roughly four-in-ten Americans say they are very worried about companies selling their information to others without them knowing (42%) or people stealing their identity or personal information (38%). Fewer are apprehensive about law enforcement monitoring what they do online (15%).
Racial and ethnic differences
However, some of these shares are higher among Hispanic, Black or Asian adults: 1
- Roughly half of Hispanic, Black or Asian adults are very worried about people stealing their identity or personal information, compared with a third of White adults.
- About one-in-five of each group are very worried about law enforcement monitoring their online activity; 10% of White adults say this.
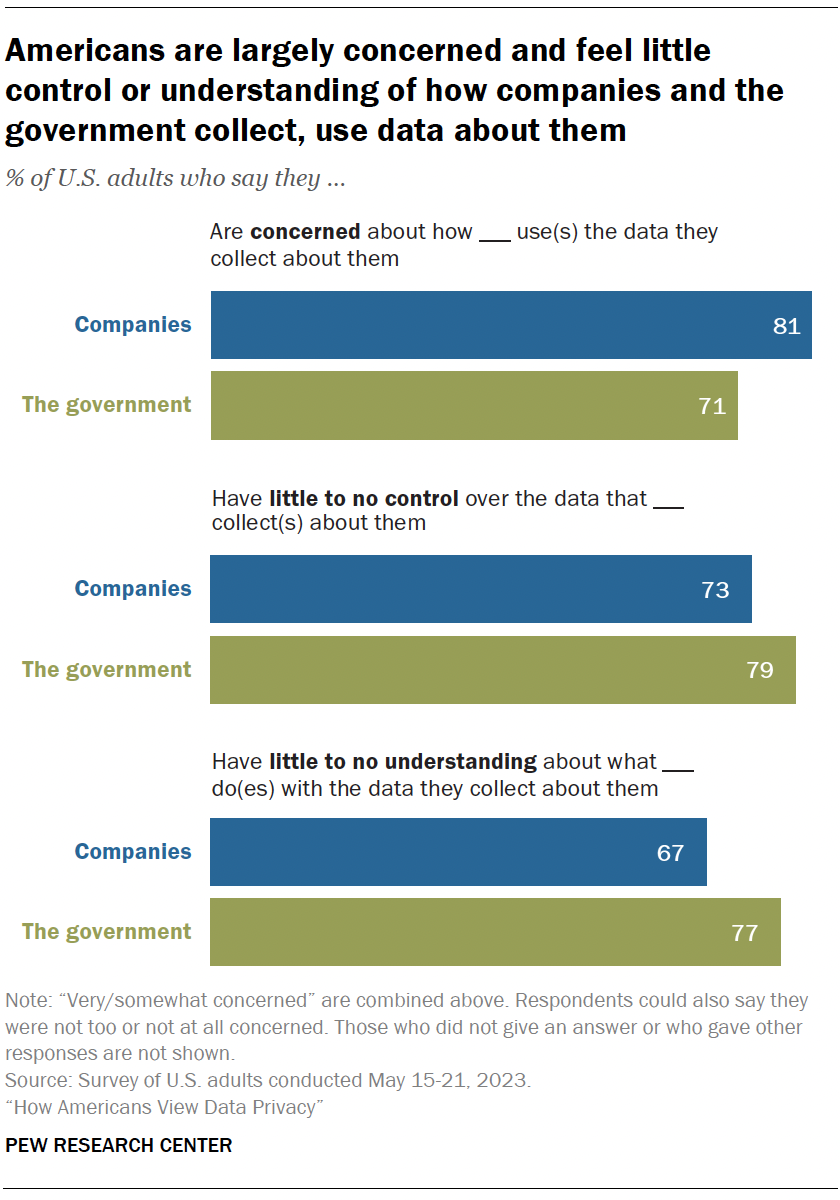
A majority of Americans say they are concerned, lack control and have a limited understanding about how the data collected about them is used. This is true whether it’s the government or companies using their data. Similar sentiments were expressed in 2019, when we last asked about this .
Concern is high: 81% say they feel very or somewhat concerned with how companies use the data they collect about them. Fully 71% say the same regarding the government’s use of data.
People don’t feel in control: Roughly three-quarters or more feel they have very little or no control over the data collected about them by companies (73%) or the government (79%).
Understanding is low: Americans also say they don’t understand what these actors are doing with the data collected about them. Majorities say they have very little or no understanding of this, whether by the government (77%) or companies (67%).
Americans are now less knowledgeable than before about how companies are using their personal data. The share who say they don’t understand this has risen from 59% in 2019 to 67% in 2023.
They have also grown more concerned about how the government uses the data it collects about them, with the share expressing concern up from 64% to 71% over this same period.
While these sentiments have not changed significantly since 2019 among Democrats and those who lean toward the Democratic Party, Republicans and GOP leaners have grown more wary of government data collection. Today, 77% of Republicans say they are concerned about how the government uses data it collects about them, up from 63% four years earlier.
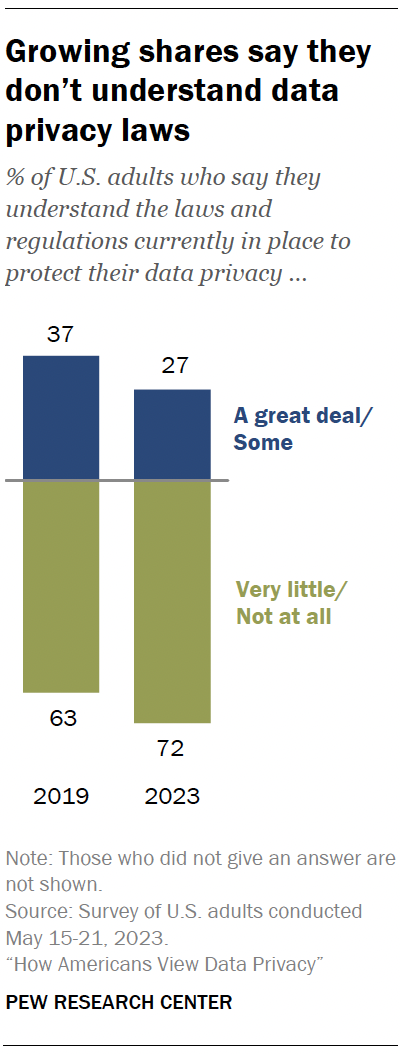
Americans are less knowledgeable about data privacy laws today than in the past.
Today, 72% of Americans say they have little to no understanding about the laws and regulations that are currently in place to protect their data privacy. This is up from 63% in 2019.
By comparison, the shares who say they understand some or a great deal about these laws decreased from 37% in 2019 to 27% in 2023.
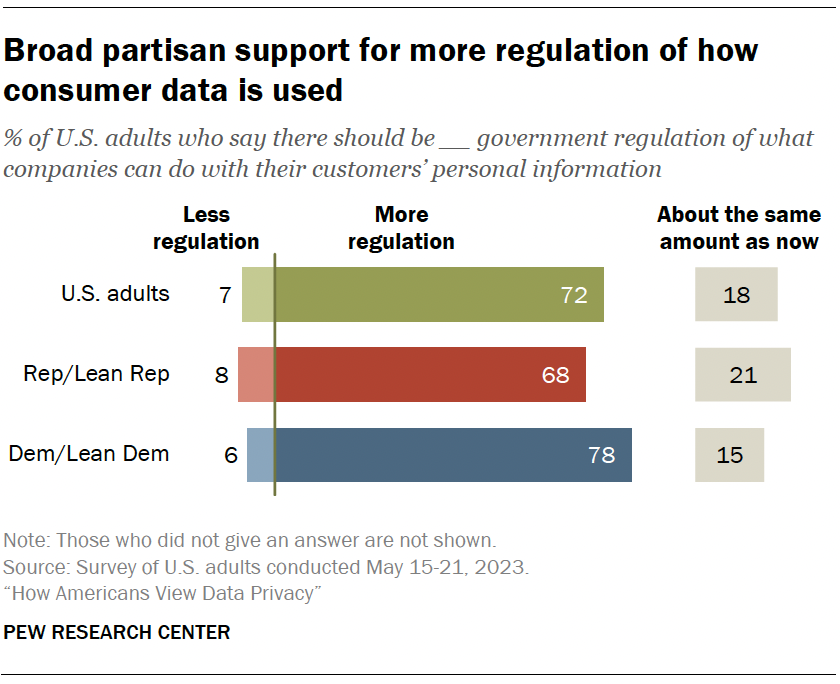
Overall, 72% say there should be more government regulation of what companies can do with their customers’ personal information. Just 7% say there should be less regulation. Another 18% say it should stay about the same.
Views by political affiliation
There is broad partisan support for greater involvement by the government in regulating consumer data.
A majority of Democrats and Republicans say there should be more government regulation for how companies treat users’ personal information (78% vs. 68%).
These findings are largely on par with a 2019 Center survey that showed strong support for increased regulations across parties.
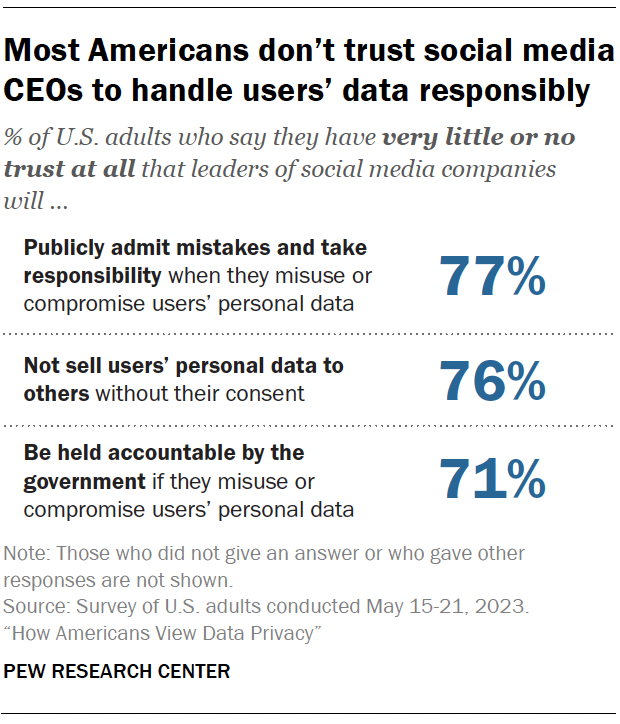
Majorities of Americans say they have little to no trust that leaders of social media companies will publicly admit mistakes regarding consumer data being misused or compromised (77%), that these leaders will not sell users’ personal data to others without their consent (76%), and that leaders would be held accountable by the government if they were to misuse or compromise users’ personal data (71%).
This includes notable shares who have no trust at all in those who are running social media sites. For example, 46% say they have no trust at all in executives of social media companies to not sell users’ data without their consent.
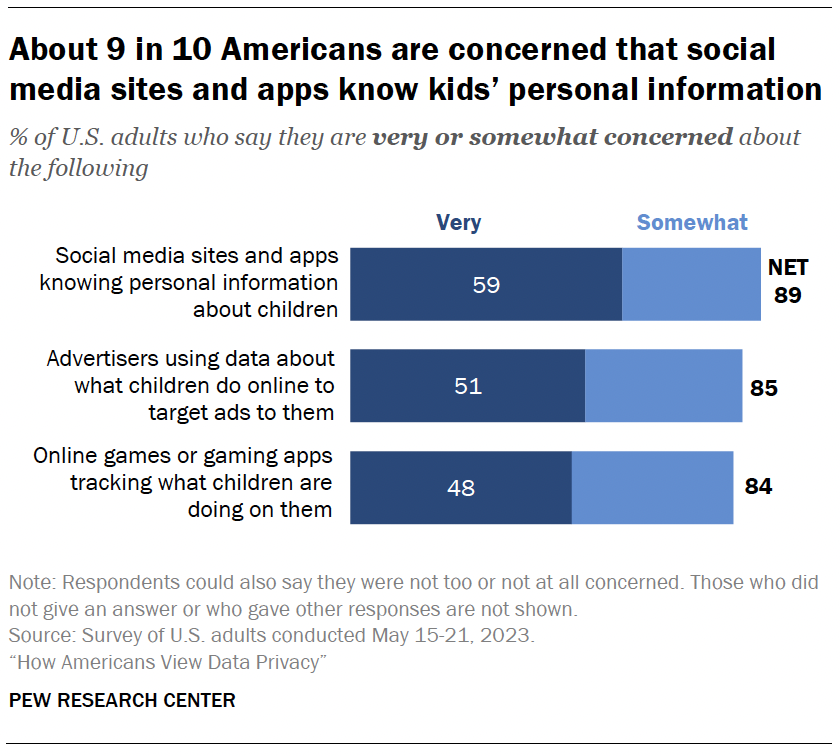
Most Americans say they are concerned about social media sites knowing personal information about children (89%), advertisers using data about what children do online to target ads to them (85%) and online games tracking what children are doing on them (84%).
Concern is widespread, with no statistically significant differences between those with and without children.
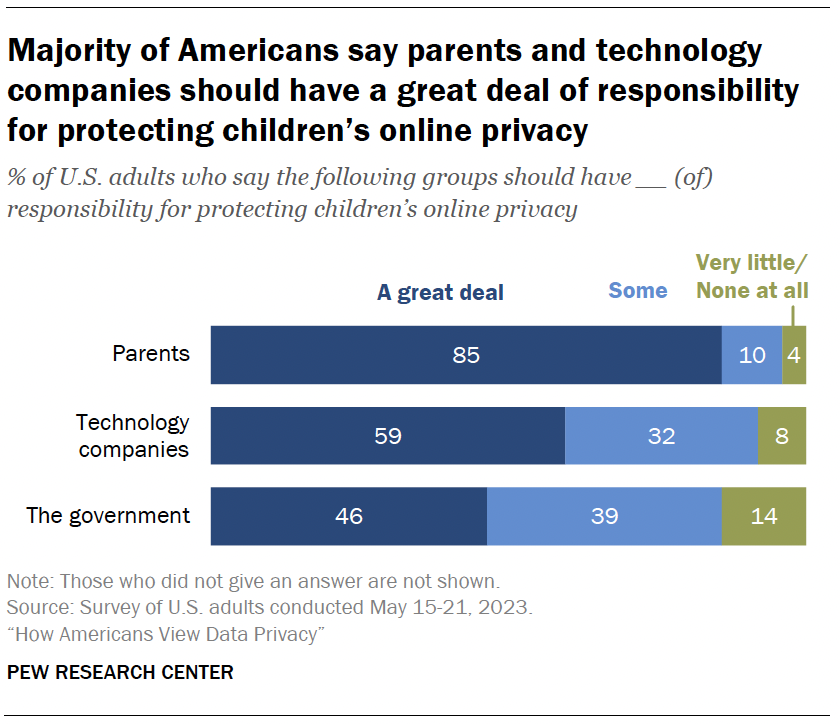
Another key question is who should be responsible for the actual protection of kids’ online privacy.
Fully 85% say parents bear a great deal of responsibility for protecting children’s online privacy. Roughly six-in-ten say the same about technology companies, and an even smaller share believe the government should have a great deal of responsibility.
The survey also measured how acceptable Americans think it is for law enforcement to use surveillance tools during criminal investigations.
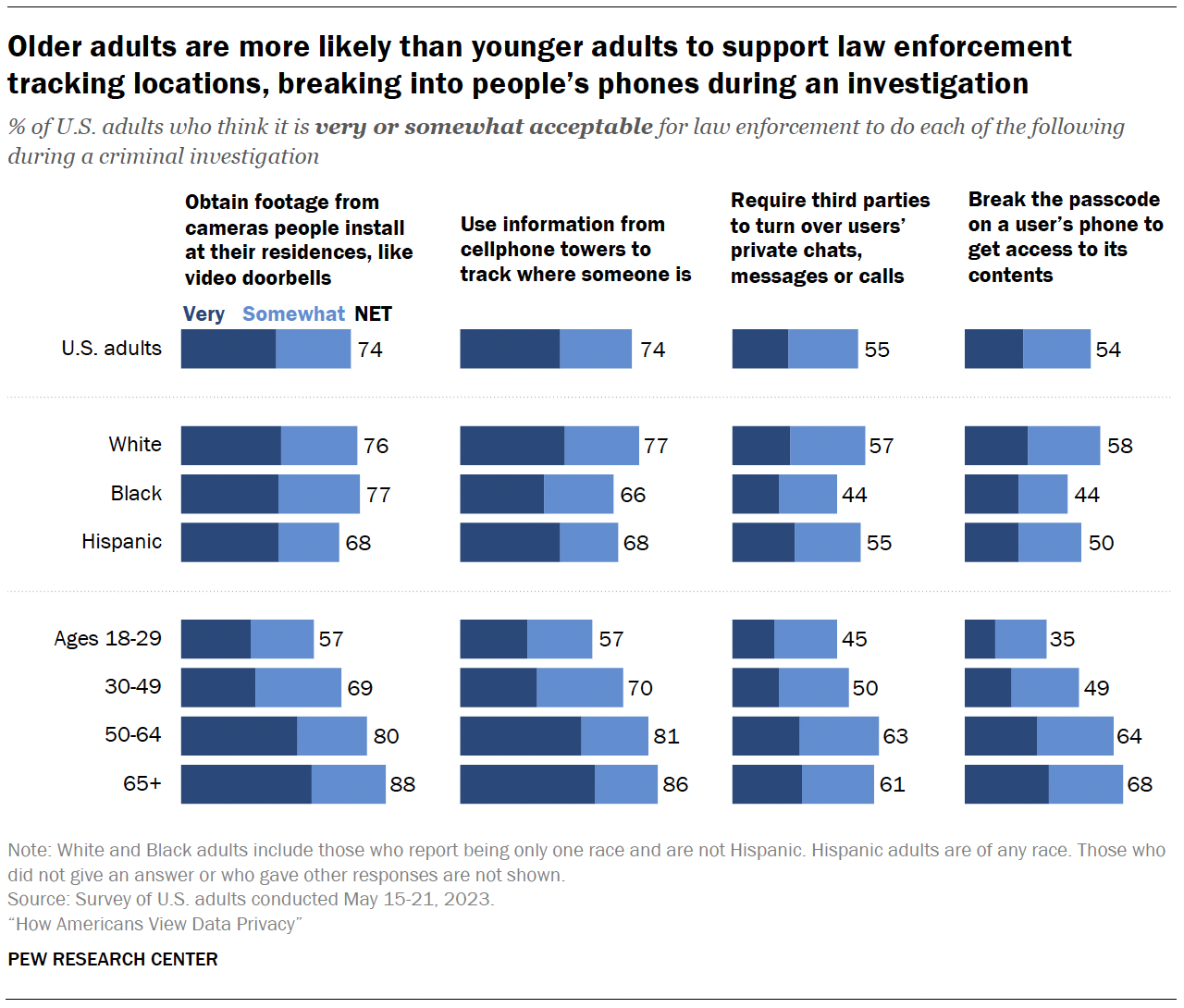
Roughly three-quarters of Americans say it’s very or somewhat acceptable for law enforcement to obtain footage from cameras people install at their residences during a criminal investigation or use information from cellphone towers to track where someone is.
By comparison, smaller shares – though still a slight majority – say it is acceptable to break the passcode on a user’s phone (54%) or require third parties to turn over users’ private chats, messages or calls (55%) during a criminal investigation. 2
About one-in-ten Americans say they aren’t sure how they feel about law enforcement doing each of these things.
Age differences
Older adults are much more likely than younger adults to say it’s at least somewhat acceptable for law enforcement to take each of these actions in criminal investigations.
For example, 88% of those 65 and older say it’s acceptable for law enforcement to obtain footage from cameras people install at their residences, compared with 57% of those ages 18 to 29.
In the case of a criminal investigation:
- White adults are more likely than Hispanic and Black adults to think it’s acceptable for law enforcement to use information from cellphone towers to track people’s locations and to break the passcode on a user’s phone to get access to its contents.
- White and Hispanic adults are more likely than Black adults to say it’s acceptable to require third parties to turn over users’ private chats, messages or calls.
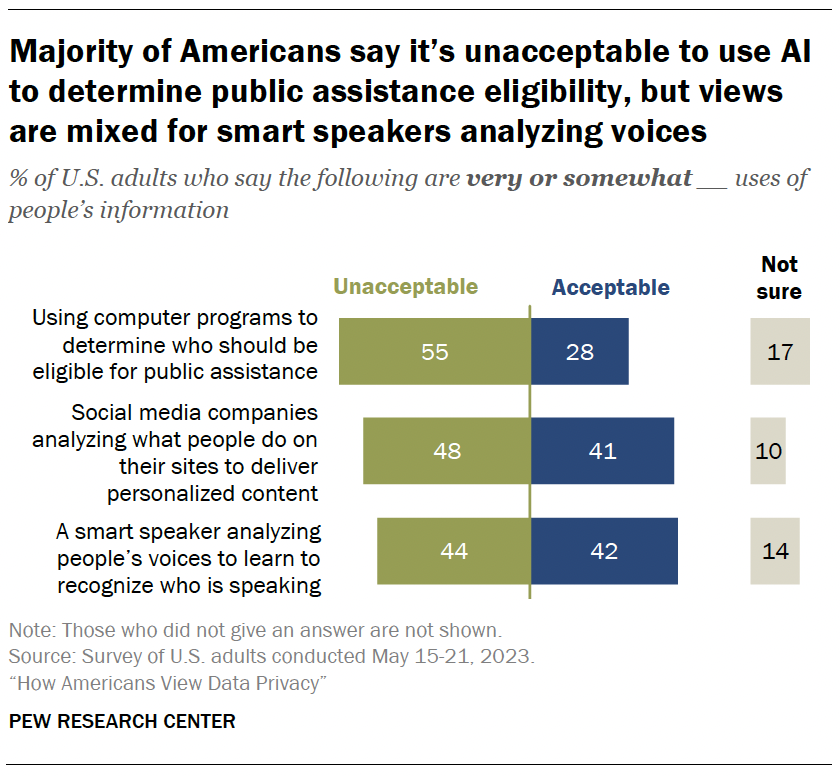
Artificial intelligence (AI) can be used to collect and analyze people’s personal information. Some Americans are wary of companies using AI in this way.
Fully 55% of adults say using computer programs to determine who should be eligible for public assistance is unacceptable. Roughly a quarter say it’s an acceptable use of AI.
Roughly half (48%) think it is unacceptable for social media companies to analyze what people do on their sites to deliver personalized content. Still, 41% are supportive of this.
Views are mixed when it comes to smart speakers analyzing people’s voices to learn who is speaking. Statistically equal shares say it’s unacceptable and acceptable (44% and 42%, respectively).
And some Americans – ranging from 10% to 17% – are uncertain about whether these uses are acceptable or not.
- 49% of adults 50 and older say it’s unacceptable for a smart speaker to analyze people’s voices to learn to recognize who’s speaking. This share drops to four-in-ten among adults under 50.
- Similarly, 56% of those 50 and older say social media companies analyzing what people do on their sites to deliver personalized content is unacceptable. But 41% of those under 50 say the same.
- There are no differences between those under 50 and those 50 and older over whether computer programs should be used to determine eligibility for public assistance.
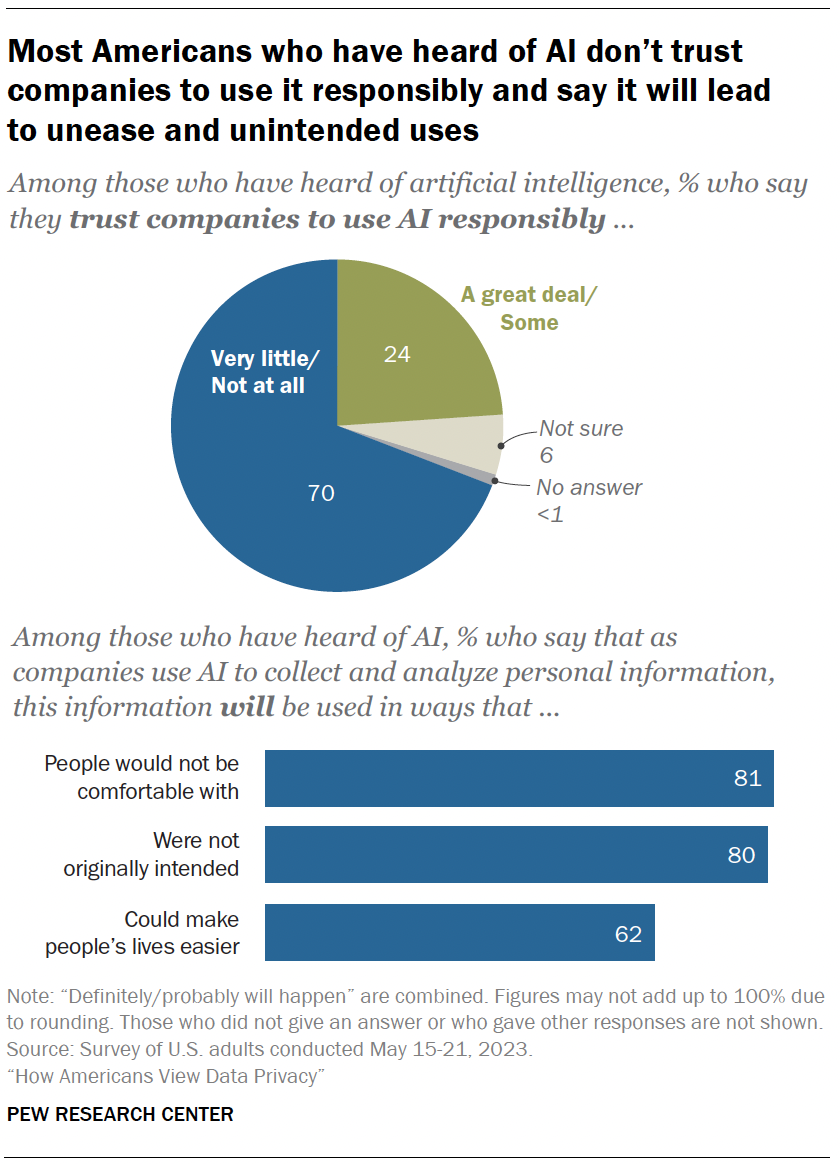
In addition to understanding people’s comfort level with certain uses of AI, the survey also measured the public’s attitudes toward companies that are utilizing AI in their products.
Among those who have heard of AI:
- 70% say they have little to no trust in companies to make responsible decisions about how they use AI in their products.
- Roughly eight-in-ten say the information will be used in ways people are not comfortable with or that were not originally intended.
- Views are more mixed regarding the potential that using AI to analyze personal details could make life easier. A majority of those who have heard of AI say this will happen (62%). Regarding differences by age, adults under 50 are more optimistic than those 50 and older (70% vs. 54%).
- 87% of those with a college degree or higher say companies will use AI to analyze personal details in ways people would not be comfortable with. Some 82% of those with some college experience and 74% with a high school diploma or less say the same.
- 88% of those with a bachelor’s degree or more say companies will use this information in ways that were not originally intended. This share drops to 80% among those with some college experience and 71% among those with a high school diploma or less.
- About three-quarters of those with a college degree or more (74%) say this information will be used in ways that could make people’s lives easier. But this share drops to 60% among those with some college experience and 52% among those with a high school diploma or less.
- This survey includes a total sample size of 364 Asian adults. The sample primarily includes English-speaking Asian adults and, therefore, it may not be representative of the overall Asian adult population. Despite this limitation, it is important to report the views of Asian adults on the topics in this study. As always, Asian adults’ responses are incorporated into the general population figures throughout this report. Asian adults are shown as a separate group when the question was asked of the full sample. Because of the relatively small sample size and a reduction in precision due to weighting, results are not shown separately for Asian adults for questions that were only asked of a random half of respondents (Form 1/Form 2). ↩
- Half of respondents were asked the questions above, and the other half received the same questions with the added context of it being a “criminal investigation where public safety is at risk.” Differences in response were largely modest. See Appendix A for these findings. ↩
Sign up for our weekly newsletter
Fresh data delivery Saturday mornings
Sign up for The Briefing
Weekly updates on the world of news & information
- Artificial Intelligence
- Online Privacy & Security
- Social Media
- Tech Companies
Social Media Fact Sheet
Teens and social media fact sheet, more americans are getting news on tiktok, bucking the trend seen on most other social media sites, life on social media platforms, in users’ own words, charting congress on social media in the 2016 and 2020 elections, most popular.
1615 L St. NW, Suite 800 Washington, DC 20036 USA (+1) 202-419-4300 | Main (+1) 202-857-8562 | Fax (+1) 202-419-4372 | Media Inquiries
Research Topics
- Email Newsletters
ABOUT PEW RESEARCH CENTER Pew Research Center is a nonpartisan fact tank that informs the public about the issues, attitudes and trends shaping the world. It conducts public opinion polling, demographic research, media content analysis and other empirical social science research. Pew Research Center does not take policy positions. It is a subsidiary of The Pew Charitable Trusts .
© 2024 Pew Research Center

Photo by Raghu Rai/Magnum
Privacy is power
Don’t just give away your privacy to the likes of google and facebook – protect it, or you disempower us all.
by Carissa Véliz + BIO
Imagine having a master key for your life. A key or password that gives access to the front door to your home, your bedroom, your diary, your computer, your phone, your car, your safe deposit, your health records. Would you go around making copies of that key and giving them out to strangers? Probably not the wisest idea – it would be only a matter of time before someone abused it, right? So why are you willing to give up your personal data to pretty much anyone who asks for it?
Privacy is the key that unlocks the aspects of yourself that are most intimate and personal, that make you most you, and most vulnerable. Your naked body. Your sexual history and fantasies. Your past, present and possible future diseases. Your fears, your losses, your failures. The worst thing you have ever done, said, and thought. Your inadequacies, your mistakes, your traumas. The moment in which you have felt most ashamed. That family relation you wish you didn’t have. Your most drunken night.
When you give that key, your privacy, to someone who loves you, it will allow you to enjoy closeness, and they will use it to benefit you. Part of what it means to be close to someone is sharing what makes you vulnerable, giving them the power to hurt you, and trusting that person never to take advantage of the privileged position granted by intimacy. People who love you might use your date of birth to organise a surprise birthday party for you; they’ll make a note of your tastes to find you the perfect gift; they’ll take into account your darkest fears to keep you safe from the things that scare you. Not everyone will use access to your personal life in your interest, however. Fraudsters might use your date of birth to impersonate you while they commit a crime; companies might use your tastes to lure you into a bad deal; enemies might use your darkest fears to threaten and extort you. People who don’t have your best interest at heart will exploit your data to further their own agenda. Privacy matters because the lack of it gives others power over you.
You might think you have nothing to hide, nothing to fear. You are wrong – unless you are an exhibitionist with masochistic desires of suffering identity theft, discrimination, joblessness, public humiliation and totalitarianism, among other misfortunes. You have plenty to hide, plenty to fear, and the fact that you don’t go around publishing your passwords or giving copies of your home keys to strangers attests to that.
You might think your privacy is safe because you are a nobody – nothing special, interesting or important to see here. Don’t shortchange yourself. If you weren’t that important, businesses and governments wouldn’t be going to so much trouble to spy on you.
You have your attention, your presence of mind – everyone is fighting for it. They want to know more about you so they can know how best to distract you, even if that means luring you away from quality time with your loved ones or basic human needs such as sleep. You have money, even if it is not a lot – companies want you to spend your money on them. Hackers are eager to get hold of sensitive information or images so they can blackmail you. Insurance companies want your money too, as long as you are not too much of a risk, and they need your data to assess that. You can probably work; businesses want to know everything about whom they are hiring – including whether you might be someone who will want to fight for your rights. You have a body – public and private institutions would love to know more about it, perhaps experiment with it, and learn more about other bodies like yours. You have an identity – criminals can use it to commit crimes in your name and let you pay for the bill. You have personal connections. You are a node in a network. You are someone’s offspring, someone’s neighbour, someone’s teacher or lawyer or barber. Through you, they can get to other people. That’s why apps ask you for access to your contacts. You have a voice – all sorts of agents would like to use you as their mouthpiece on social media and beyond. You have a vote – foreign and national forces want you to vote for the candidate that will defend their interests.
As you can see, you are a very important person. You are a source of power.
By now, most people are aware that their data is worth money. But your data is not valuable only because it can be sold. Facebook does not technically sell your data, for instance. Nor does Google. They sell the power to influence you. They sell the power to show you ads, and the power to predict your behaviour. Google and Facebook are not really in the business of data – they are in the business of power. Even more than monetary gain, personal data bestows power on those who collect and analyse it, and that is what makes it so coveted.
T here are two aspects to power. The first aspect is what the German philosopher Rainer Forst in 2014 defined as ‘the capacity of A to motivate B to think or do something that B would otherwise not have thought or done’. The means through which the powerful enact their influence are varied. They include motivational speeches, recommendations, ideological descriptions of the world, seduction and credible threats. Forst argues that brute force or violence is not an exercise of power, for subjected people don’t ‘do’ anything; rather, something is done to them. But clearly brute force is an instance of power. It is counterintuitive to think of someone as powerless who is subjecting us through violence. Think of an army dominating a population, or a thug strangling you. In Economy and Society (1978), the German political economist Max Weber describes this second aspect of power as the ability for people and institutions to ‘carry out [their] own will despite resistance’.
In short, then, powerful people and institutions make us act and think in ways in which we would not act and think were it not for their influence. If they fail to influence us into acting and thinking in the way that they want us to, powerful people and institutions can exercise force upon us – they can do unto us what we will not do ourselves.
There are different types of power: economic, political and so on. But power can be thought of as being like energy: it can take many different forms, and these can change. A wealthy company can often use its money to influence politics through lobbying, for instance, or to shape public opinion through paying for ads.
Power over others’ privacy is the quintessential kind of power in the digital age
That tech giants such as Facebook and Google are powerful is hardly news. But exploring the relationship between privacy and power can help us to better understand how institutions amass, wield and transform power in the digital age, which in turn can give us tools and ideas to resist the kind of domination that survives on violations of the right to privacy. However, to grasp how institutions accumulate and exercise power in the digital age, first we have to look at the relationship between power, knowledge and privacy.
There is a tight connection between knowledge and power. At the very least, knowledge is an instrument of power. The French philosopher Michel Foucault goes even further, and argues that knowledge in itself is a form of power . There is power in knowing. By protecting our privacy, we prevent others from being empowered with knowledge about us that can be used against our interests.
The more that someone knows about us, the more they can anticipate our every move, as well as influence us. One of the most important contributions of Foucault to our understanding of power is the insight that power does not only act upon human beings – it constructs human subjects (even so, we can still resist power and construct ourselves). Power generates certain mentalities, it transforms sensitivities, it brings about ways of being in the world. In that vein, the British political theorist Steven Lukes argues in his book Power (1974) that power can bring about a system that produces wants in people that work against their own interests. People’s desires can themselves be a result of power, and the more invisible the means of power, the more powerful they are. Examples of power shaping preferences today include when tech uses research about how dopamine works to make you addicted to an app, or when you are shown political ads based on personal information that makes a business think you are a particular kind of person (a ‘persuadable’, as the data-research company Cambridge Analytica put it, or someone who might be nudged into not voting, for instance).
The power that comes about as a result of knowing personal details about someone is a very particular kind of power. Like economic power and political power, privacy power is a distinct type of power, but it also allows those who hold it the possibility of transforming it into economic, political and other kinds of power. Power over others’ privacy is the quintessential kind of power in the digital age.
T wo years after it was funded and despite its popularity, Google still hadn’t developed a sustainable business model. In that sense, it was just another unprofitable internet startup. Then, in 2000, Google launched AdWords, thereby starting the data economy. Now called Google Ads, it exploited the data produced by Google’s interactions with its users to sell ads. In less than four years, the company achieved a 3,590 per cent increase in revenue.
That same year, the Federal Trade Commission had recommended to US Congress that online privacy be regulated. However, after the attacks of 11 September 2001 on the Twin Towers in New York, concern about security took precedence over privacy, and plans for regulation were dropped. The digital economy was able to take off and reach the magnitude it enjoys today because governments had an interest in having access to people’s data in order to control them. From the outset, digital surveillance has been sustained through a joint effort between private and public institutions.
The mass collection and analysis of personal data has empowered governments and prying companies. Governments now know more about their citizens than ever before. The Stasi (the security service of the German Democratic Republic), for instance, managed to have files only on about a third of the population, even if it aspired to have complete information on all citizens. Intelligence agencies today hold much more information on all of the population. To take just one important example, a significant proportion of people volunteer private information in social networks. As the US filmmaker Laura Poitras put it in an interview with The Washington Post in 2014: ‘Facebook is a gift to intelligence agencies.’ Among other possibilities, that kind of information gives governments the ability to anticipate protests, and even pre-emptively arrest people who plan to take part. Having the power to know about organised resistance before it happens, and being able to squash it in time, is a tyrant’s dream.
Tech companies’ power is constituted, on the one hand, by having exclusive control of data and, on the other, by the ability to anticipate our every move, which in turn gives them opportunities to influence our behaviour, and sell that influence to others. Companies that earn most of their revenues through advertising have used our data as a moat – a competitive advantage that has made it impossible for alternative businesses to challenge tech titans. Google’s search engine, for example, is as good as it is partly because its algorithm has much more data to learn from than any of its competitors. In addition to keeping the company safe from competitors and allowing it to train its algorithm better, our data also allows tech companies to predict and influence our behaviour. With the amount of data it has access to, Google can know what keeps you up at night, what you desire the most, what you are planning to do next. It then whispers this information to other busybodies who want to target you for ads.
Tech wants you to think that the innovations it brings into the market are inevitable
Companies might also share your data with ‘data brokers’ who will create a file on you based on everything they know about you (or, rather, everything they think they know), and then sell it to pretty much whoever is willing to buy it – insurers, governments, prospective employers, even fraudsters.
Data vultures are incredibly savvy at using both the aspects of power discussed above: they make us give up our data, more or less voluntarily, and they also snatch it away from us, even when we try to resist. Loyalty cards are an example of power making us do certain things that we would otherwise not do. When you are offered a discount for loyalty at your local supermarket, what you are being offered is for that company to conduct surveillance on you, and then influence your behaviour through nudges (discounts that will encourage you to buy certain products). An example of power doing things to us that we don’t want it to do is when Google records your location on your Android smartphone, even when you tell it not to.
Both types of power can also be seen at work at a more general level in the digital age. Tech constantly seduces us into doing things we would not otherwise do, from getting lost down a rabbit hole of videos on YouTube, to playing mindless games, or checking our phone hundreds of times a day. The digital age has brought about new ways of being in the world that don’t always make our lives better. Less visibly, the data economy has also succeeded in normalising certain ways of thinking. Tech companies want you to think that, if you have done nothing wrong, you have no reason to object to their holding your data. They also want you to think that treating your data as a commodity is necessary for digital tech, and that digital tech is progress – even when it might sometimes look worryingly similar to social or political regress. More importantly, tech wants you to think that the innovations it brings into the market are inevitable. That’s what progress looks like, and progress cannot be stopped.
That narrative is complacent and misleading. As the Danish economic geographer Bent Flyvbjerg points out in Rationality and Power (1998), power produces the knowledge, narratives and rationality that are conducive to building the reality it wants. But technology that perpetuates sexist and racist trends and worsens inequality is not progress. Inventions are far from unavoidable. Treating data as a commodity is a way for companies to earn money, and has nothing to do with building good products. Hoarding data is a way of accumulating power. Instead of focusing only on their bottom line, tech companies can and should do better to design the online world in a way that contributes to people’s wellbeing. And we have many reasons to object to institutions collecting and using our data in the way that they do.
Among those reasons is institutions not respecting our autonomy, our right to self-govern. Here is where the harder side of power plays a role. The digital age thus far has been characterised by institutions doing whatever they want with our data, unscrupulously bypassing our consent whenever they think they can get away with it. In the offline world, that kind of behaviour would be called matter-of-factly ‘theft’ or ‘coercion’. That it is not called this in the online world is yet another testament to tech’s power over narratives.
I t’s not all bad news, though. Yes, institutions in the digital age have hoarded privacy power, but we can reclaim the data that sustains it, and we can limit their collecting new data. Foucault argued that, even if power constructs human subjects, we have the possibility to resist power and construct ourselves. The power of big tech looks and feels very solid. But tech’s house of cards is partly built on lies and theft. The data economy can be disrupted. The tech powers that be are nothing without our data. A small piece of regulation, a bit of resistance from citizens, a few businesses starting to offer privacy as a competitive advantage, and it can all evaporate.
No one is more conscious of their vulnerability than tech companies themselves. That is why they are trying to convince us that they do care about privacy after all (despite what their lawyers say in court). That is why they spend millions of dollars on lobbying. If they were so certain about the value of their products for the good of users and society, they would not need to lobby so hard. Tech companies have abused their power, and it is time to resist them.
In the digital age, resistance inspired by the abuse of power has been dubbed a techlash. Abuses of power remind us that power needs to be curtailed for it to be a positive influence in society. Even if you happen to be a tech enthusiast, even if you think that there is nothing wrong with what tech companies and governments are doing with our data, you should still want power to be limited, because you never know who will be in power next. Your new prime minister might be more authoritarian than the old one; the next CEO of the next big tech company might not be as benevolent as those we’ve seen thus far. Tech companies have helped totalitarian regimes in the past, and there is no clear distinction between government and corporate surveillance. Businesses share data with governments, and public institutions share data with companies.
When you expose your privacy, you put us all at risk
Do not give in to the data economy without at least some resistance. Refraining from using tech altogether is unrealistic for most people, but there is much more you can do short of that. Respect other people’s privacy. Don’t expose ordinary citizens online. Don’t film or photograph people without their consent, and certainly don’t share such images online. Try to limit the data you surrender to institutions that don’t have a claim to it. Imagine someone asks for your number in a bar and won’t take a ‘No, thank you’ for an answer. If that person were to continue to harass you for your number, what would you do? Perhaps you would be tempted to give them a fake number. That is the essence of obfuscation, as outlined by the media scholars Finn Bruton and Helen Nissenbaum in the 2015 book of that name. If a clothing company asks for your name to sell you clothes, give them a different name – say, Dr Private Information, so that they get the message. Don’t give these institutions evidence they can use to claim that we are consenting to our data being taken away from us. Make it clear that your consent is not being given freely.
When downloading apps and buying products, choose products that are better for privacy. Use privacy extensions on your browsers. Turn your phone’s wi-fi, Bluetooth and locations services off when you don’t need them. Use the legal tools at your disposal to ask companies for the data they have on you, and ask them to delete that data. Change your settings to protect your privacy. Refrain from using one of those DNA home testing kits – they are not worth it. Forget about ‘smart’ doorbells that violate your privacy and that of others. Write to your representatives sharing your concerns about privacy. Tweet about it. Take opportunities as they come along to inform business, governments and other people that you care about privacy, that what they are doing is not okay.
Don’t make the mistake of thinking you are safe from privacy harms, maybe because you are young, male, white, heterosexual and healthy. You might think that your data can work only for you, and never against you, if you’ve been lucky so far. But you might not be as healthy as you think you are, and you will not be young forever. The democracy you are taking for granted might morph into an authoritarian regime that might not favour the likes of you.
Furthermore, privacy is not only about you. Privacy is both personal and collective. When you expose your privacy, you put us all at risk. Privacy power is necessary for democracy – for people to vote according to their beliefs and without undue pressure, for citizens to protest anonymously without fear of repercussions, for individuals to have freedom to associate, speak their minds, read what they are curious about. If we are going to live in a democracy, the bulk of power needs to be with the people. If most of the power lies with companies, we will have a plutocracy. If most of the power lies with the state, we will have some kind of authoritarianism. Democracy is not a given. It is something we have to fight for every day. And if we stop building the conditions in which it thrives, democracy will be no more. Privacy is important because it gives power to the people. Protect it.

Biography and memoir
The adoption paradox
Even happy families cannot avoid the reality – my reality – that adoption is predicated on transacting the life of a child
Fiona Sampson

Pleasure and pain
Me versus myself
I work against myself through procrastination, distraction and addiction. Why do I consistently sabotage my own life?
Eliane Glaser

Global history
The route to progress
Anticolonial modernity was founded upon the fight for liberation from communists, capitalists and imperialists alike
Frank Gerits

Thinkers and theories
Paper trails
Husserl’s well-tended archive has given him a rich afterlife, while Nietzsche’s was distorted by his axe-grinding sister
Peter Salmon

Philosophy of mind
The problem of erring animals
Three medieval thinkers struggled to explain how animals could make mistakes – and uncovered the nature of nonhuman minds

Moral progress is annoying
You might feel you can trust your gut to tell right from wrong, but the friction of social change shows that you can’t
Daniel Kelly & Evan Westra
The New York Times
Opinion | the privacy project, the privacy project.
APRIL 10, 2019
The New York Times is launching an ongoing examination of privacy. We’ll dig into the ideas, history and future of how our information navigates the digital ecosystem and what’s at stake.
Companies and governments are gaining new powers to follow people across the internet and around the world, and even to peer into their genomes. The benefits of such advances have been apparent for years; the costs — in anonymity, even autonomy — are now becoming clearer. The boundaries of privacy are in dispute, and its future is in doubt. Citizens, politicians and business leaders are asking if societies are making the wisest tradeoffs. The Times is embarking on this monthslong project to explore the technology and where it’s taking us, and to convene debate about how it can best help realize human potential.
Does Privacy Matter?
What do they know, and how do they know it, what should be done about this, what can i do.
View all Privacy articles
Stuart A. Thompson and Charlie Warzel
One Nation, Tracked
Dec. 19, 2019
Timothy Libert
This Article Is Spying On You
Sept. 18, 2019
Agnes Callard
The Real Cost of Tweeting About My Kids
Nov. 11, 2019
Bianca Vivion Brooks
I Used to Fear Being a Nobody. Then I Left Social Media.
Oct. 1, 2019
From the Newsroom
A Surveillance Net Blankets China’s Cities, Giving Police Vast Powers
Dec. 17, 2019
Mark Bowden
The Worm That Nearly Ate the Internet
June 29, 2019
James Orenstein
I’m a Judge. Here’s How Surveillance Is Challenging Our Legal System.
June 13, 2019
Sahil Chinoy
We Built an ‘Unbelievable’ (but Legal) Facial Recognition Machine
April 16, 2019
Bill Hanvey
Your Car Knows When You Gain Weight
May 20, 2019
As Cameras Track Detroit’s Residents, a Debate Ensues Over Racial Bias
July 8, 2019
Chris Hughes
It’s Time to Break Up Facebook
May 9, 2019
The Editorial Board
Total Surveillance Is Not What America Signed Up For
Dec. 21, 2019
Glenn S. Gerstell
N.S.A. Official: We Need to Prepare for the Future of War
Sept. 13, 2019
Charlie Warzel
Amazon Wants to Surveil Your Dog
Oct. 10, 2019
15 Ways Facebook, Google, Apple and Amazon Are in Government Cross Hairs
Sept. 6, 2019
Patrick Berlinquette
I Used Google Ads for Social Engineering. It Worked.
August 4, 2019
Bekah Wells
The Trauma of Revenge Porn
May 6, 2019
Jack Poulson
I Used to Work for Google. I Am a Conscientious Objector.
April 23, 2019
Roseanna Sommers and Vanessa K. Bohns

Would You Let the Police Search Your Phone?
April 30, 2019
Now Some Families Are Hiring Coaches to Help Them Raise Phone-Free Children
July 6, 2019
Illustrations by Max Guther
More on NYTimes.com
Advertisement
Internet Privacy - Essay Examples And Topic Ideas For Free
Internet privacy refers to the right or expectation of privacy in the digital realm, encompassing issues related to the protection of personal data, confidentiality, and anonymity online. Essays on internet privacy could delve into the risks and challenges associated with digital surveillance, data breaches, or online tracking, the impact of laws and regulations on privacy, or the ways in which individuals and organizations can protect privacy online. They might also explore the ethical, social, and political implications of privacy in the digital age, or the tensions between privacy, security, and convenience online. A substantial compilation of free essay instances related to Internet Privacy you can find at PapersOwl Website. You can use our samples for inspiration to write your own essay, research paper, or just to explore a new topic for yourself.
Impact of Technology on Privacy
The 21st Century is characterized by the heavy impact technology has on us as a society while it continues to develop new devices and modernize technology. Millions of individuals around the world are now connected digitally, in other words, people globally rely heavily on smartphones tablets, and/ or computers that store or save a majority of their personal information. Critical and extremely personal data is available and collected in these smart technology such as credit card details, fingerprint layout, and […]
A World Without Internet
On the street is the 21st century. Almost all people on our planet have access to the Internet. And they are actively using it. But they forget that they use it almost around the clock. From watching the weather in the morning to texting on social media in the evening. Instead of writing an essay by hand, a modern student simply downloads it. People on the Internet are already looking for work, pay for housing and communal services, participate in […]
Positive and Negative Effects of Internet
The topic of the pros and cons of the Internet is one of the most controversial topics. People often cannot give a definite answer to it. The topic of the Internet is quite versatile. Let's look at it from the positive side first. The Internet is the greatest invention of mankind, which made life easier and continues to do it for us hundreds of times. Its first plus is, of course, the available information. Now you can find out any […]
We will write an essay sample crafted to your needs.
Security Versus Freedom?
Welcome to the Digital Age. In today’s connected world, we are living much of our live online. As a result, companies everywhere are creating large storehouses of data on all of us. The most obvious information being collected is social media data. Everything we post publicly and some cases privately, is being stored and analysed. But it is not just social media, there is now a digital record of everything we buy, everything we watch, where we go and what […]
Internet Access Restrictions May Vary
Fantastic. In most instances, they are placed on search quarries and are most prominent at education centers. This is simply to keep minds safe from content unsuitable for most ages (Gonchar). Although this is an effective plan with good intentions, it can become more effective by being enforced on younger ages rather than those who have already been exposed to the negative side of the internet. As you enter high school you have nearly done and seen everything there […]
Securing Cyberspace: Crafting Tomorrow’s Internet Privacy Laws
In an era where digital footprints shape our daily lives, the quest to safeguard personal privacy in the vast expanse of the internet has become more critical than ever before. Transitioning from the pixels that construct our online world to the intricate policies governing its boundaries signifies a pivotal juncture in the evolution of digital governance. As we navigate through this landscape of data, the formulation of robust internet privacy legislation emerges as a beacon of protection against the perils […]
Silent Struggle: Assessing Threats to Internet Privacy and Security
In today's digital age, the internet serves as the cornerstone of modern communication, commerce, and entertainment. However, amidst the convenience and connectivity it offers, lurks a pervasive and often invisible battle for privacy and security. From data breaches to surveillance, the threats to our online well-being are manifold and ever-evolving. One of the most concerning threats is the rampant collection and misuse of personal data by corporations and governments alike. Every click, search, and purchase leaves a digital footprint, eagerly […]
Safeguarding Cyberspace: the Vital Role of AI in Preserving Online Privacy
In an era where our digital footprints grow larger with every click, the question of how to protect our online privacy becomes increasingly pertinent. Enter Artificial Intelligence, our modern-day guardians in the complex realm of cyberspace. Far beyond mere machines crunching numbers, AI has evolved into a formidable force in the fight against privacy breaches. The first and foremost duty of AI guardians is to fortify our virtual boundaries. Picture them as vigilant sentinels stationed at the gates of our […]
Preserving Digital Integrity: a Scholarly Evaluation of Internet Privacy
In the contemporary digital epoch, where the internet serves as an omnipotent conduit for global interaction, commerce, and information dissemination, the concept of cyber privacy emerges as a pivotal concern. As an academic critic, entrusted with scrutinizing the intricacies of cyber privacy, it becomes essential to unravel the diverse facets of this intricate matter, ranging from its legal and ethical dimensions to its societal and technological reverberations. Cyber privacy fundamentally entails the right of individuals to govern their personal information […]
Additional Example Essays
- Positive Effects of Social Media
- Instagram and body dysmorphia
- The Negative Effects of Social Media On Mental Health
- The Mental Health Stigma
- How the Roles of Women and Men Were Portrayed in "A Doll's House"
- Psychiatric Nurse Practitioner
- Substance Abuse and Mental Illnesses
- Importance Of Accountability
- Are Electric Cars Better Than Petrol Diesel Cars?
- "A Doll's House" as a Modern Tragedy
- Poems “The Negro Speaks of Rivers” and “Still I Rise”
- The Unique Use of Literary Devices in The Tell-Tale Heart
1. Tell Us Your Requirements
2. Pick your perfect writer
3. Get Your Paper and Pay
Hi! I'm Amy, your personal assistant!
Don't know where to start? Give me your paper requirements and I connect you to an academic expert.
short deadlines
100% Plagiarism-Free
Certified writers
- Undergraduate
- High School
- Architecture
- American History
- Asian History
- Antique Literature
- American Literature
- Asian Literature
- Classic English Literature
- World Literature
- Creative Writing
- Linguistics
- Criminal Justice
- Legal Issues
- Anthropology
- Archaeology
- Political Science
- World Affairs
- African-American Studies
- East European Studies
- Latin-American Studies
- Native-American Studies
- West European Studies
- Family and Consumer Science
- Social Issues
- Women and Gender Studies
- Social Work
- Natural Sciences
- Pharmacology
- Earth science
- Agriculture
- Agricultural Studies
- Computer Science
- IT Management
- Mathematics
- Investments
- Engineering and Technology
- Engineering
- Aeronautics
- Medicine and Health
- Alternative Medicine
- Communications and Media
- Advertising
- Communication Strategies
- Public Relations
- Educational Theories
- Teacher's Career
- Chicago/Turabian
- Company Analysis
- Education Theories
- Shakespeare
- Canadian Studies
- Food Safety
- Relation of Global Warming and Extreme Weather Condition
- Movie Review
- Admission Essay
- Annotated Bibliography
- Application Essay
- Article Critique
- Article Review
- Article Writing
- Book Review
- Business Plan
- Business Proposal
- Capstone Project
- Cover Letter
- Creative Essay
- Dissertation
- Dissertation - Abstract
- Dissertation - Conclusion
- Dissertation - Discussion
- Dissertation - Hypothesis
- Dissertation - Introduction
- Dissertation - Literature
- Dissertation - Methodology
- Dissertation - Results
- GCSE Coursework
- Grant Proposal
- Marketing Plan
- Multiple Choice Quiz
- Personal Statement
- Power Point Presentation
- Power Point Presentation With Speaker Notes
- Questionnaire
- Reaction Paper
Research Paper
- Research Proposal
- SWOT analysis
- Thesis Paper
- Online Quiz
- Literature Review
- Movie Analysis
- Statistics problem
- Math Problem
- All papers examples
- How It Works
- Money Back Policy
- Terms of Use
- Privacy Policy
- We Are Hiring
Privacy and Internet Policy, Essay Example
Pages: 3
Words: 856
Hire a Writer for Custom Essay
Use 10% Off Discount: "custom10" in 1 Click 👇
You are free to use it as an inspiration or a source for your own work.
Establishing an effective privacy and Internet policy requires a strategic approach to understanding the challenges and limitations of these requirements. It is evident that with modern technology, there is an increased ability to intercept confidential information and to use it to one’s advantage in a negative manner. Therefore, it becomes necessary to identify criteria that will ensure that this information is protected at all costs as best as possible. Since the Internet as a whole is extremely difficult to manage in terms of protecting personal and confidential information. This is a necessary step so that Internet users experience a feeling of safety and security when sharing their information across this channel. The following discussion will address the requirements and trends in privacy and Internet policy, and will consider the issues and challenges that individuals face from a privacy perspective when using the Internet for personal or professional reasons.
It is very important to consider the requirements involved in protecting the rights of all people, and that they are entitled to express themselves and share information on an individual basis, and to develop effective measures to enhance the protection of personal information, regardless of the source. Therefore, a number of laws and regulations have been established in the United States that attempt to protect this information from unnecessary risk or harm, such as the Electronic Communications Privacy Act, which “makes it unlawful under certain circumstances for someone to read or disclose the contents of an electronic communication” (Privacy Rights Clearinghouse, 2010). In this context, it is important for individuals and organizations to take the steps that are necessary to protect information from being shared unlawfully under specific circumstances, and to also demonstrate that despite the freedom that Americans possess to speak in their own way, they must also adhere to the same rights of others, and to work collaboratively to protect information from being tampered with as best as possible (Privacy Rights Clearinghouse, 2010).
Since there are so many levels of privacy and Internet policy, it is necessary to consider how these policies influence and impact organizational needs in different ways. To be specific, when organizations seek information from consumers to develop products and services that will be applicable to their needs, but this is a difficult concept to manage, as noted in the following: “the ease of collecting consumer data has resulted in fraud, violations of consumer privacy, and identity theft. As a result, consumers are increasingly wary of providing personal information, and more laws are being passed to protect their rights” (Verio, 2010). Therefore, by developing a privacy and Internet policy that protects this information at all costs, it is possible to strike a balance between the concerns that are involved in supporting organizational objectives, while also considering how to protect information from being stolen or duplicated (Verio, 2010). This is not a unique problem, but it nonetheless requires a clear sense of direction and focus so that navigating the Internet is a safe practice (Verio, 2010).
Perhaps the most important aspect of privacy and Internet policy is to ensure that customers or other users of different websites and systems are not uncomfortable with the level of information that they are required to share, and that this information is protected from thieves and other hackers at maximum levels. Since privacy and Internet policies often posses general similarities but must cater to specific needs, these policies must create opportunities to ensure that customers and other users are provided with the best possible protection from invasion of their privacy and personal information.
Finally, it is essential for those using the Internet to be provided with a series of opportunities that will ensure that their use of the Internet and subsequent information sharing is supported by organizations that have their best interests in mind, and that privacy policies are made public and are explicitly detailed in favor of supporting consumer rights and protections (American Express). This will ensure that consumers will experience a level of comfort in sharing this information, and will know that the law is on their side when providing personal data that is transmitted through a website (American Express). The public disclosure of these policies and procedures also demonstrates an effective approach to supporting the rights and protections of all citizens, and as the Internet platform continues to evolve, there are even greater alternatives, such as encryption of data, that are available that will ensure that users will experience a sense of comfort in knowing that their data is not be shared unlawfully with others (American Express). The protection of personal information that is shared across the Internet must be a key priority of today’s organizations, and must demonstrate that their privacy policies are a key component of doing business in today’s society, where the Internet is a key priority and focus of today’s modern organization in terms of providing service and doing business as a whole.
American Express (2010). Internet privacy statement. Retrieved July 11, 2010, from https://www212.americanexpress.com/dsmlive/dsm/dom/us/en/privacystatement/internetprivacystatement.do?vgnextoid=f25533fadb4ca110VgnVCM100000defaad94RCRD&vgnextchannel=9823f30b6b1ca110VgnVCM100000defaad94RCRD&
Privacy Rights Clearinghouse (2010). Fact sheet 18: online privacy: using the Internet safely. Retrieved July 11, 2010, from http://www.privacyrights.org/fs/fs18-cyb.htm#PART_ONE
Verio (2010). Privacy policies and Internet advertising law. Retrieved July 11, 2010, from http://www.verio.com/resource-center/business-guides/internet-law/
Stuck with your Essay?
Get in touch with one of our experts for instant help!
Integrated Software Applications, Research Paper Example
Connecting the Future in Healthcare Institutions, Research Paper Example
Time is precious
don’t waste it!
Plagiarism-free guarantee
Privacy guarantee
Secure checkout
Money back guarantee

Related Essay Samples & Examples
Voting as a civic responsibility, essay example.
Pages: 1
Words: 287
Utilitarianism and Its Applications, Essay Example
Words: 356
The Age-Related Changes of the Older Person, Essay Example
Pages: 2
Words: 448
The Problems ESOL Teachers Face, Essay Example
Pages: 8
Words: 2293
Should English Be the Primary Language? Essay Example
Pages: 4
Words: 999
The Term “Social Construction of Reality”, Essay Example
Words: 371

45,000+ students realised their study abroad dream with us. Take the first step today
Here’s your new year gift, one app for all your, study abroad needs, start your journey, track your progress, grow with the community and so much more.

Verification Code
An OTP has been sent to your registered mobile no. Please verify

Thanks for your comment !
Our team will review it before it's shown to our readers.

Speech on Internet Privacy
- Updated on
- Jul 2, 2021

It is rightly said that today’s era is a digital era. We may not realize it now, but the internet has become a new necessity in our lives. It has witnessed a boom like never before. In today’s time, the internet is as important to us as food, water, air is. Having said that, internet or internet privacy does have a dark side about which we must be aware of. Internet users must be well-versed in the methods for safeguarding their data on the internet. In this blog, we have brought to you a speech on internet privacy that you can refer to for your English homework, assignments, and exams.
Table of contents
What is internet privacy, speech on internet privacy: sample 1 (200-300 words), speech on internet privacy: sample 2 (400-500 words), relatable links.
Must Read: Essay on Internet: Advantages and Disadvantages
Before actually skipping onto the speech on internet privacy, let us first discuss what is meant by internet privacy. The amount of privacy protection an individual has while connected to the Internet is defined as online privacy or internet privacy. It discusses the level of internet security accessible for personal and financial information, conversations, and preferences. Internet users frequently try to enhance their online privacy by using anti-virus software, creating strong passwords, disabling tracking, evaluating site security, and selecting for tougher privacy settings. Online privacy threats vary from phishing schemes to viruses, and issues with website security can lead to identity theft. Internet privacy is a complicated topic that encompasses how your personal information is utilized, gathered, shared, and kept on your own devices and when connected to the Internet. Personal information about your habits, purchasing, and location can be gathered and shared with third parties via your phone, GPS, and other devices. Users of the internet and mobile devices have the right to know how their information will be used and to examine online privacy policies.
Also Read: Cyber Security Courses: A Detailed Guide and Top 10 Cybersecurity Skills for Beginners
Good morning everyone! I am Aryaman and today I stand before you to present an insightful and informative speech on Internet Privacy. Privacy, whether offline or online, is definitely our right, which should be demanded and expected no matter what the cost, but one might wonder why there is so much concern centered around internet privacy. Most of our lives have become virtual in the pandemic era, and all activities that were previously done offline are now done online. Be it our bank details, legal discussions with CA , or our professional work-related details, there is no guarantee that privacy on the internet is guarded.
In the year 1997, the Consumer Internet Privacy Protection Act was passed by the government as per which the consumer information shared on the internet should be safeguarded at any cost, but still, it is a matter of utmost concern and importance because the internet offers various communication tools which are frequently used and there too, the information being shared can be tracked by someone who knows how to do it and also technology has grown at a steadfast level that even our old messages that are deleted can be easily retrieved because of availability of countless apps. Certain websites use cookies that record data while we sign up or log in and, even if we are anonymous, it is relatively easy in this technologically advanced era to know our true identity, personal details, and Internet Service Provider details as well.
As a result, whatever web-based email services we use, such as Yahoo, Hotmail, or Gmail, we must be familiar with the privacy policies of those services before signing up or logging in to protect our privacy, and we must not hesitate to take action against heinous cybercrimes if we become aware of any kind of cyber abuse.
Also Read: Safer Internet Day 2021
Good morning everyone! I am Aryaman and today I stand before you to present an insightful and informative speech on Internet Privacy. We can define internet privacy as safeguarding our personal, financial, and other important information when we are online. However, after decoding the definition, one must ask, “Is internet privacy a reality or a myth?”Let us further explore this problem and crack the code. Due to the pandemic, most of our lives have now taken a virtual turn and most of our tasks, be it our work meetings, binge-watching our favorite web series, chatting with friends, online business transactions, and banking transactions, are all done online.
In real life, we only disclose information that we believe is not confidential, but in the online world, simple information such as email IDs and passwords can be traced by a skilled individual, and technology has advanced to the point where the internet and mobile phones are available to children, making them just as vulnerable as adults. After understanding the gravity of the situation, we must explore the ways in which we can ensure our online privacy. To begin with, there are a plethora of software applications that ensure online privacy, such as anti-viruses and anti-malware, and it is critical that these software applications are updated to their most recent version to avoid any sort of privacy problem. Second of all, internet history must be cleared on a regular basis. Online investments and banking transactions must be done through reliable sources only. Thirdly, online shopping must be done on reliable websites only which have credibility and authenticity, and we must avoid giving our information to those websites which don’t seem to be genuine and authentic. Also, we must keep a strong password for our email IDs and for other accounts as well.
We must be well-versed in Internet privacy laws, and if we encounter any type of online privacy issue, we must report it immediately so that the problem does not worsen. After attaining a crystal clear understanding of internet privacy, we must continually educate ourselves about this problem and be aware and prevent ourselves from having any sort of online privacy problem. In the end, I would like to say my heartiest thanks to the audience for listening to my speech on internet privacy with patience.
- Speech on Indian Education System
- Speech on Importance of English
- Generation Gap Speech for Students
- Sample Essay & Speech on Fear for ASL
- Speech on Co-Education For School Students
How did you all find the speech? Do let us know your thoughts on the same in the comments section. Also, feel free to reach our experts at Leverage Edu , to seek guidance at every step of your study abroad education journey.
Team Leverage Edu
Leave a Reply Cancel reply
Save my name, email, and website in this browser for the next time I comment.
Contact no. *

Leaving already?
8 Universities with higher ROI than IITs and IIMs
Grab this one-time opportunity to download this ebook
Connect With Us
45,000+ students realised their study abroad dream with us. take the first step today..

Resend OTP in

Need help with?
Study abroad.
UK, Canada, US & More
IELTS, GRE, GMAT & More
Scholarship, Loans & Forex
Country Preference
New Zealand
Which English test are you planning to take?
Which academic test are you planning to take.
Not Sure yet
When are you planning to take the exam?
Already booked my exam slot
Within 2 Months
Want to learn about the test
Which Degree do you wish to pursue?
When do you want to start studying abroad.
September 2024
January 2025
What is your budget to study abroad?
How would you describe this article ?
Please rate this article
We would like to hear more.
- EssayBasics.com
- Pay For Essay
- Write My Essay
- Homework Writing Help
- Essay Editing Service
- Thesis Writing Help
- Write My College Essay
- Do My Essay
- Term Paper Writing Service
- Coursework Writing Service
- Write My Research Paper
- Assignment Writing Help
- Essay Writing Help
- Call Now! (USA) Login Order now
- EssayBasics.com Call Now! (USA) Order now
- Writing Guides
The Internet Privacy (Essay/Paper Sample)
Table of Contents
The Internet Privacy
Internet privacy entails securing personal data that is published on the internet. This kind of privacy encompasses safeguarding of sensitive and private information, data, preferences, and communications. In the current cyberspace, different people have raised complaints regarding loss of personal information whenever they do online transactions, visit social media sites, and participate in online games as well as attending forums. In such circumstances, many people exhibit incidences of compromised passwords, the revelation of victims’ identities, and fraud. Such privacy issues come as a result of negligence by the users or website developers who do not comply with the regulations and standards that curb privacy violation. Thus, internet privacy is under threat due to the inability of the internet service providers who have no explicit permission to gain access or share confidential information. This essay presents a discussion of internet privacy and how online users fall victims due to increased vulnerability of online security.
Internet privacy is a paradoxical and difficult to understand. People are aware of their behaviors online and are bound to use strong passwords when before accessing their own accounts. In the same note, users are supposed to log out their own accounts when ceasing access to the internet so that they leave it safe and secure from intruders. However, regardless of such knowledge and clear understanding of the privacy policy, they do not bother. Instead, they lament of the increased vulnerability due to such negligence. On a separate note, people tend to care about protecting their personal information and normally feel insecure when issuing it on the internet. Therefore, this behavior brings about privacy paradox since they are unable to gain control of their own digital information.
Internet privacy faces numerous risks that include phishing that encompasses hacking activities that are used to obtain secured information, usernames, passwords, security PIN, credit card numbers and bank account numbers. Furthermore, users have been under attack through pharming which covers redirection of legitimate website users to a new and different IP address. Others include the use of offline applications that get information without user’s consent. In such circumstances, a computer that is online can be accessed to get the previously acquired data that is sent to the spyware source. On a separate note, there is a rise in the usage of malware which allows an illegal damage of computers both online and offline through application viruses, Trojan, and spyware.
Need an essay customized under your requirements? We can help you
In addition to the above measures, users should always keep their operating systems and windows up to date to avoid vulnerability. A rise in software vulnerability is enhanced through the use of outdated systems. This increases loopholes for cyber criminals. For example, Flash and Java are normally vulnerable to security threats hence expose their users to cyber attacks. On the same note, users should avoid accessing free Wi-Fi networks since such networks are used by hackers with network sniffers that retrieve crucial information. Lastly, users should always update and change their privacy settings on regular basis.
In conclusion, the essay has elaborated on internet privacy based on the different risks and vulnerability that users are facing besides highlighting the different measures that should be put in place. However, reduction of vulnerability of internet privacy begins with the user’s behavior regarding internet usage. Users should incorporate all the measures and should be careful when revealing their personal information online. Lastly, users should be aware of their privacy rights and should fight for such rights especially in cases when breaches occur.

Internet Issues: Teens, Social Media and Privacy Essay
- To find inspiration for your paper and overcome writer’s block
- As a source of information (ensure proper referencing)
- As a template for you assignment
Introduction
Potential threats, influence factors, works cited.
The Internet can easily be viewed as a single greatest factor that shapes the contemporary world. Since its emergence and popularization two decades ago it has changed the way humans handle information and improved on every single aspect of our lives related to it including education, media, trade, culture, and social interactions (Pew Research Center). The growing online presence also created an unprecedented visibility opportunities, which immediately raised privacy concerns. With the increasing number of controversies surrounding the safety of personal information, the Internet has been termed by some “the final blow to privacy.” However, I argue that while it certainly changed the way we perceive safety of information, the situation may be far less grim than portrayed by sensationalist media.
It is hard to argue that the Internet opened up numerous vulnerable spots in our personal spaces. It has become extremely easy to post a silly photograph and end up being bullied by the entire country. The recent history of the Web is abundant with the cases such as the Dog Poo Girl – a woman from Korea whose photograph was published online as an attempt to persuade her to clean after her dog in the subway. Initially intended as a righteous act, the disclosure quickly got out of control and reached threatening proportions (“Dog Poo Girl”). On some occasions, such events led to tragic outcomes. In fact, Facebook is named as a reason behind the divorce in one case out of three (Chatel). Numerous examples exist where the information published online cost people their jobs (Price). To further complicate the matter, the very premise of safe online communication seems to be threatened by the recent developments in the legal sphere (Wagner). There is little doubt that privacy as we know it is under real threat.
At this point, it is worth pointing out the “as we know it” part of the allegation. I argue that it is our understanding of privacy that provides the solution and that the Internet is the biggest factor that influences it. From my personal experience, I can say that several years ago, when social network resources were gaining popularity, users (especially young ones) were absolutely reckless in setting up their accounts. Any friendship request could be confirmed instantly, and privacy policy was something utterly boring and hardly necessary. In comparison, today the majority of youth know how to configure the essential privacy settings and how to spot a suspicious link (Madden et al.).
While the former example could be interpreted by some as an illustration of the potential threat created by the Web to the inexperienced users, I suggest that it actually illustrates our pre-Internet understanding of information safety. In other words, by facing the controversial cases like that of the Dog Poo Girl, we learn to acknowledge responsibilities for sensitive information (both ours and that of others) and make conscious decisions instead of happily agreeing to everything. Essentially, prior to the emergence of the Internet, we had little opportunity to manage our information in a way that presented a feasible threat and, because of that, had only a vague idea of the concept of privacy.
Considering the information above, it would be tempting to say that the Internet taught us to handle the very threat it created. I do not think this is the case. Rather it presented the problem on the level that is easy to grasp and illustrative enough to communicate the importance of privacy to people. Safety of information has always been crucial – the Web just made it relevant and approachable enough to become a universal issue. I consider it a good thing, and while there is no doubt that it creates risks, we certainly are capable of handling them.
Chatel, Amanda. “ The Real Reason Facebook Causes One-Third of Divorces .” YourTango . 2014. Web.
“ Dog Poo Girl .” Know Your Meme , n.d. Web.
Madden, Mary, et al. “ Teens, Social Media, and Privacy .” Pew Research Center , 2013. Web.
Pew Research Center. “Internet Seen as Positive Influence on Education but Negative on Morality in Emerging and Developing Nations.” Pew Research Center . 2015.
Price, Lydia. “20 Tales of Employees Who were Fired Because of Social Media Posts.” People . 2016.
Wagner, Meg. “Congress Votes to Repeal Internet Privacy Protections.” WNEP . 2017.
- Understanding Teen Depression
- Dogs, Their History, and Bonding with Human
- Web Privacy - Reliance on Internet
- Internet Monopolies: Everybody Wants to Rule the World
- Wireless Networks' Historical Development
- Electronic Nature of Information Systems
- Mobile Internet and Its Economics
- Recommender Systems of Internet
- Chicago (A-D)
- Chicago (N-B)
IvyPanda. (2020, September 13). Internet Issues: Teens, Social Media and Privacy. https://ivypanda.com/essays/internet-issues-teens-social-media-and-privacy/
"Internet Issues: Teens, Social Media and Privacy." IvyPanda , 13 Sept. 2020, ivypanda.com/essays/internet-issues-teens-social-media-and-privacy/.
IvyPanda . (2020) 'Internet Issues: Teens, Social Media and Privacy'. 13 September.
IvyPanda . 2020. "Internet Issues: Teens, Social Media and Privacy." September 13, 2020. https://ivypanda.com/essays/internet-issues-teens-social-media-and-privacy/.
1. IvyPanda . "Internet Issues: Teens, Social Media and Privacy." September 13, 2020. https://ivypanda.com/essays/internet-issues-teens-social-media-and-privacy/.
Bibliography
IvyPanda . "Internet Issues: Teens, Social Media and Privacy." September 13, 2020. https://ivypanda.com/essays/internet-issues-teens-social-media-and-privacy/.
Privacy and data protection
Promoting respect for privacy is essential for a well-functioning digital economy. When individuals have confidence in the protections surrounding their personal data, they are more likely to engage in online activities, share information, and participate in the digital economy. This, in turn, drives economic growth, fosters innovation, and encourages the free flow of data across borders.
- OECD Privacy Guidelines
- Review of the OECD Recommendation on Enforcement of Privacy Laws

Select a language
Key messages, privacy is key for trust in the collection and use of data.
The OECD promotes respect for privacy as a fundamental value and a critical condition for the free flow of personal data across borders. The OECD Privacy Guidelines are the first internationally agreed-upon set of principles and have inspired data protection frameworks around the globe.
Privacy can enhance trust around the collection and use of data and facilitate data sharing and the generation of economic and social value. International co-operation is key to ensure effective enforcement, innovative responses to data governance challenges, and trustworthy and privacy-enhancing AI.
Privacy and data protection are an essential component of digital policies
Data is everywhere in today's economies and societies. When governments act on digital policies, they need to consider privacy and data protection as a matter of priority. Effective protection of people's personal data helps to improve trust in the digital environment.
Sectoral regulations need to be consistent with high levels of privacy and data protection. The OECD works to improve cross-sectoral regulatory co-operation on privacy and data protection, especially regarding competition, health , banking , finance , and payments.
Privacy enhancing technologies (PETs) complement privacy and data protection frameworks but need clear guidance to tackle regulatory, technical and adoption challenges
PETs serve as crucial advanced tools for enabling collection, analysis and sharing of information while protecting data confidentiality and privacy. They do not replace existing legal frameworks but rather support and enhance the implementation of privacy protection principles. However, their effectiveness is still contingent upon overcoming some regulatory, technical, and adoption hurdles.
Critical to their success is the need for clear guidance and efforts to bridge knowledge gaps. Additionally, PETs' role in facilitating cross-border data flows with trust warrants further exploration of their potential and limitations. Beyond privacy, PETs are also key in fostering trust for collaborations by protecting intellectual property rights and fostering digital security.
Government access cannot be unconstrained or unreasonable
Governments need to access personal data held by the private sector for national security and law enforcement purposes. However, such access cannot be unconstrained or unreasonable.
The Declaration on Government Access to Personal Data Held by Private Sector Entities adopted by OECD Members and the European Union in 2022 embodies the commonality in safeguards put in place by countries. The Declaration helps to ensure that government access is in accordance with democratic values, safeguards for privacy and other human rights and freedoms, and the rule of law.
Individuals who do not submit official forms online due to privacy and security concerns
Concerns about the protection and security of personal data are still reported as a reason for not submitting official forms online. However, this share of individuals across the OECD has been decreasing since its significant peak in 2014.
In 2023, only 1.34% of the individuals in the OECD did not submit official forms online due to privacy and security concerns compared to almost 4% in 2014. The share can still be as high as 4.7% in Hungary (compared to its peak of 11.5% in 2015), 4.2% in France (compared to 10.3% in 2015), and 3.4% in Portugal (compared to 7.8% in 2017). Other reasons for not submitting official forms include lack of skills and service availability.
Individuals who read privacy policy statements before providing personal data
An OECD study reveals that online service providers' choice architecture, including default settings and information presentation, often 'nudges' consumers towards decisions that benefit the providers more, not the consumers. This issue known as ‘dark patterns’ is exacerbated by lengthy and complex privacy statements, making truly informed consent challenging.
Evidence shows that consumer engagement with these statements varies significantly by country, ranging between almost 50% in Norway and Finland to only 20% in Luxembourg, France and Belgium. This indicates a widespread issue with individuals understanding and consenting to the use of their personal data.
Related data
Related publications.

Programmes of work
- Data free flow with trust Digital technologies create, capture, copy and consume vast amounts of data, and a lot of these data travel across borders. Data Free Flow with Trust (DFFT) aims to promote the free flow of data while ensuring trust in privacy, security, and intellectual property rights. Learn more
Related policy issues
- Cross-border data flows Cross-border data flows are critical for today’s global economic and social interactions. They underpin international business operations, logistics, supply chains and global communication. However, cross-border data flows also pose challenges, amplifying concerns about privacy and data protection, intellectual property, digital security, national security, regulatory reach and trade. Learn more
- Data governance Data governance encompasses technical, policy, and regulatory frameworks to manage data along its value cycle — from creation to deletion — and across policy domains including health, research, public administration, and finance. It ranks as a top priority for governments aiming to maximise the benefits of data while addressing challenges such as privacy and intellectual property as well as competition and empowerment. Learn more
- Privacy enhancing technologies Privacy enhancing technologies (PETs) enable the collection, analysis and sharing of information while protecting data confidentiality and privacy. Learn more
- Privacy principles Protecting people’s privacy ensures their safety, dignity, and other fundamental rights and freedoms such as freedom of thought and expression. Using personal data through digital technologies provides great social and economic benefits, but it can also compromise privacy. With the Privacy Guidelines, which contain the first internationally agreed-upon set of principles, the OECD has been at the forefront of promoting respect for privacy as a fundamental value and a critical condition for the free flow of personal data across borders. Learn more

IMAGES
VIDEO
COMMENTS
Get custom essay. Ultimately, the importance of internet privacy extends beyond individual convenience; it is a fundamental right that underpins our freedom, security, and individuality in the digital age. By recognizing the significance of internet privacy and taking meaningful steps to protect it, we can ensure that the digital landscape ...
Internet privacy is a subcategory of data privacy, focusing on the protection of user information shared online. It is a significant concern in the digital age, where data is considered the new oil. Internet privacy concerns the safeguarding of personal, financial, and data information of a private individual or organization.
Writing an essay on internet privacy is important for raising awareness, advocating for stronger privacy protections, and empowering individuals to safeguard their personal information online. By conducting thorough research, considering different perspectives, and providing practical solutions, the essay can help contribute to a more privacy ...
Internet privacy involves the right or mandate of personal privacy concerning the storage, re-purposing, provision to third parties, and display of information pertaining to oneself via the Internet. [1] [2] Internet privacy is a subset of data privacy .
Over 30 years ago, Mason (Citation 1986) voiced ethical concerns over the protection of informational privacy, or "the ability of the individual to personally control information about one's self" (Stone et al., Citation 1983), calling it one of the four ethical issues of the information age.Since the 1980s, scholars have remained concerned about informational privacy, especially given ...
1. Views of data privacy risks, personal data and digital privacy laws. Online privacy is complex, encompassing debates over law enforcement's data access, government regulation and what information companies can collect. This chapter examines Americans' perspectives on these issues and highlights how views vary across different groups ...
Power over others' privacy is the quintessential kind of power in the digital age. T wo years after it was funded and despite its popularity, Google still hadn't developed a sustainable business model. In that sense, it was just another unprofitable internet startup. Then, in 2000, Google launched AdWords, thereby starting the data economy.
From 2010- 2012 it continues to rise beyond 350,000 per year, with a monetary loss of over $300 million per year. The top 5 internet scams per (Info-graphic Highlights) with the most complaints: 1. 14.4 % - Identity theft. 2. 13.2% - FBI-related scams. 3. 9.8% - Miscellaneous fraud.
Companies and governments are gaining new powers to follow people across the internet and around the world, and even to peer into their genomes. The benefits of such advances have been apparent ...
9 essay samples found. Internet privacy refers to the right or expectation of privacy in the digital realm, encompassing issues related to the protection of personal data, confidentiality, and anonymity online. Essays on internet privacy could delve into the risks and challenges associated with digital surveillance, data breaches, or online ...
The present paper has evaluated several methodologies through which users can guarantee privacy on the internet. Some of the methodologies discussed include employing strong passwords, making use of antivirus software, using secure systems, safe Internet browsing, avoiding fake websites and avoiding phishing sites.
A privacy guideline plays an important role with regard to personal information collected on the internet. Sound policies enable users to feel comfortable because it enables the user in identifying safe sites on the internet.
The user should have knowledge of how his or her information is being collected, the purpose of collection and how the party is going to use the information.
"While the Internet-based economy provides many benefits, it also raises new concerns for maintaining the privacy of information. “Internet privacy is the privacy and security level of personal data published via the Internet.
On the other hand, Harper's article is based on the positive side of the internet privacy, which means that the internet privacy is good and scary, but people need to be careful of their own information and browsing histories, and websites. Jim Harper's essay is more relevant and reasonable than the Nicholas Carr and Lori Andrews's essays.
In this sense, internet privacy represents a challenge indeed. Internet privacy is a relatively new term and the definitions are therefore rather scarce or general. For instance, it can be defined as "the ability of individuals to determine for themselves when, how, and to what extent information about them is communicated to others."
Perhaps the most important aspect of privacy and Internet policy is to ensure that customers or other users of different websites and systems are not uncomfortable with the level of information that they are required to share, and that this information is protected from thieves and other hackers at maximum levels.
Internet privacy is the security of a user's personal data that is stored or published on the internet. The internet is an important part of every individual's daily life. In today's society, the internet is used by many different people for many reasons. It can be used for research, communication, and purchasing items.
Internet privacy is a complicated topic that encompasses how your personal information is utilized, gathered, shared, and kept on your own devices and when connected to the Internet. Personal information about your habits, purchasing, and location can be gathered and shared with third parties via your phone, GPS, and other devices.
This essay presents a discussion of internet privacy and how online users fall victims due to increased vulnerability of online security. Internet privacy is a paradoxical and difficult to understand. People are aware of their behaviors online and are bound to use strong passwords when before accessing their own accounts.
The growing online presence also created an unprecedented visibility opportunities, which immediately raised privacy concerns. With the increasing number of controversies surrounding the safety of personal information, the Internet has been termed by some "the final blow to privacy.". However, I argue that while it certainly changed the way ...
While many believe that privacy and security are only important for criminals, the document outlines several reasons why internet privacy is important for all users. It explains that anyone can have legitimate reasons for wanting privacy, such as expressing unpopular opinions or communicating sensitive business information. The internet makes private communications much easier but also less ...
Invasion of privacy is a serious issue concerning the Internet, as e-mails can be read if not encrypted, and cookies can track a user and store personal information. Lack of privacy policies and employee monitoring threatens security also. Individuals should have the right to protect themselves as much as possible from privacy invasion and ...
Promoting respect for privacy is essential for a well-functioning digital economy. When individuals have confidence in the protections surrounding their personal data, they are more likely to engage in online activities, share information, and participate in the digital economy. This, in turn, drives economic growth, fosters innovation, and encourages the free flow of data across borders.